What is Webhook Vulnerability? Ways to Exploit, Examples and Impact
Explore webhook vulnerabilities like SSRF and replay attacks. Learn technical exploitation methods and best practices to secure your callback endpoints.
Webhooks have become the invisible glue of the modern internet, enabling real-time communication between disparate software systems. While they offer immense convenience for developers, they also introduce a unique set of security challenges that are frequently overlooked during the development lifecycle. This post explores the technical intricacies of webhook vulnerabilities, how attackers exploit them, and the critical steps you must take to protect your infrastructure.
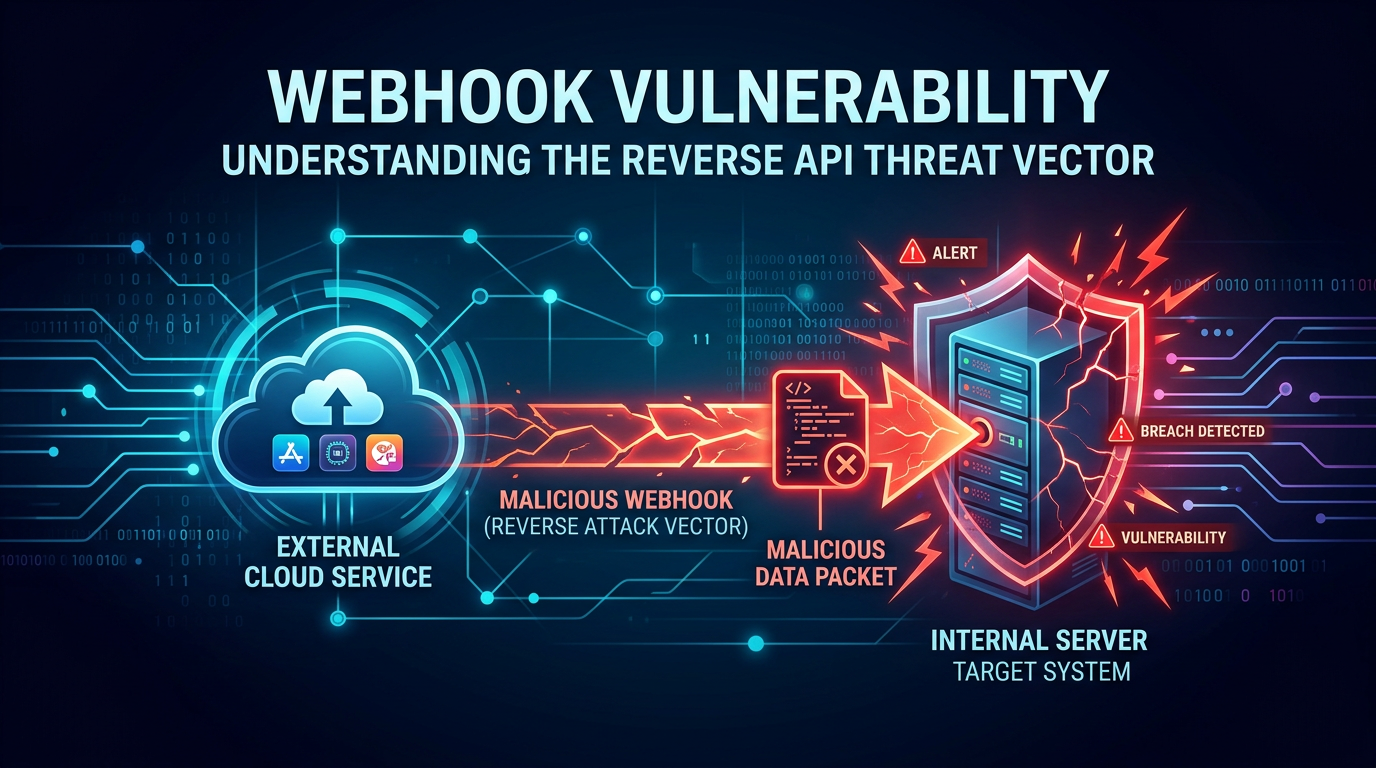
Understanding the Webhook Architecture
Before diving into vulnerabilities, it is essential to understand what a webhook is from a technical perspective. A webhook is essentially a "reverse API." In a traditional API model, a client makes a request to a server to retrieve data (the "Pull" model). In a webhook model, the server sends data to the client automatically when a specific event occurs (the "Push" model).
For example, when a customer completes a purchase on an e-commerce platform, the payment provider (the source) sends an HTTP POST request to the e-commerce store's backend (the destination) to notify it that the payment was successful. This destination endpoint is what we call a "webhook listener" or "webhook URL."
Because these endpoints are designed to be reachable by external services over the public internet, they are inherently exposed. If the listener does not properly verify the identity of the sender or the integrity of the data, it becomes a prime target for exploitation.
Common Types of Webhook Vulnerabilities
1. Server-Side Request Forgery (SSRF)
Server-Side Request Forgery (SSRF) is perhaps the most dangerous vulnerability associated with webhooks. This occurs when a web application allows a user to provide a URL for a webhook and then attempts to send a request to that URL without proper validation.
In a typical SSRF scenario involving webhooks, an attacker might register a webhook URL that points to an internal resource rather than an external service. For instance, instead of providing https://my-analytics.com/webhook, the attacker provides http://169.254.169.254/latest/meta-data/ (the AWS metadata service endpoint). If the server processes this, it might leak sensitive cloud credentials or internal network configurations.
2. Missing Authentication and Forged Events
Many developers assume that because a webhook URL is "secret" or obscure, it is secure. This is a classic example of security through obscurity. If an attacker discovers the webhook endpoint—perhaps through a leaked JavaScript file, a misconfigured log, or brute-forcing—they can send forged HTTP POST requests directly to it.
Without a mechanism to verify that the request actually came from the trusted provider (like GitHub, Stripe, or Slack), the application will process the malicious payload as if it were legitimate. This can lead to unauthorized actions, such as marking an unpaid order as "paid" or triggering a deployment of malicious code.
3. Replay Attacks
A replay attack happens when an attacker intercepts a valid webhook request and sends it multiple times to the destination server. Even if the request is signed and authenticated, if the application does not check for uniqueness, it may process the same event repeatedly.
Consider a webhook that handles credits for a user's account. If an attacker captures a valid "add 10 credits" webhook and replays it 1,000 times, they could effectively steal value from the system. Preventing this requires the use of timestamps and unique event IDs (idempotency keys).
4. Insecure Deserialization
Webhooks often transmit data in JSON or XML formats. If the receiving application uses an insecure library to deserialize this data, it could be vulnerable to Remote Code Execution (RCE). An attacker can craft a malicious serialized object in the webhook payload that, when parsed by the server, executes arbitrary commands on the underlying operating system.
How to Exploit Webhook Vulnerabilities: Technical Examples
Example 1: Exploiting Blind SSRF via Webhook Configuration
Imagine an application that allows users to set up a "Status Notification" webhook. The user enters a URL, and the server sends a test ping.
The Malicious Request:
An attacker enters the following as their webhook URL:http://internal-admin-panel.local/delete_user?id=1
The Server's Action:
The backend server, acting as a proxy, sends an internal GET request to the admin panel. Because the request originates from the internal network, it may bypass firewall rules or authentication checks that usually protect the admin panel from the public internet.
Example 2: Forging a Stripe Payment Webhook
Suppose a developer implements a Stripe webhook listener but forgets to verify the Stripe-Signature header. An attacker can send a spoofed JSON payload to the endpoint.
The Payload (attacker_payload.json):
{
"id": "evt_test_webhook",
"type": "checkout.session.completed",
"data": {
"object": {
"id": "cs_test_123",
"amount_total": 50000,
"currency": "usd",
"customer_details": {
"email": "attacker@evil.com"
},
"payment_status": "paid"
}
}
}
The Attack Command:
curl -X POST https://api.victim-site.com/webhooks/stripe \
-H "Content-Type: application/json" \
-d @attacker_payload.json
If the server processes this without signature verification, the attacker receives $500 worth of goods or services for free.
Example 3: Replay Attack on a GitHub Webhook
If a CI/CD pipeline triggers a build based on a GitHub webhook and doesn't check the X-GitHub-Delivery ID or the X-Hub-Signature-256 timestamp, an attacker can resend an old, valid payload. If the attacker knows that a specific previous commit had a vulnerability that has since been patched, they can replay the webhook for that old commit to force the server to redeploy the vulnerable version of the software.
The Impact of Webhook Exploitation
The consequences of failing to secure webhooks can be catastrophic for an organization:
- Financial Loss: As seen in the payment spoofing example, attackers can bypass billing logic.
- Data Breaches: SSRF can allow attackers to pivot into internal databases or cloud metadata services, leading to massive data exfiltration.
- Account Takeover: If webhooks are used to sync user data between services, a forged webhook could change a user's email address or password.
- Resource Exhaustion: A "Webhook Bomb" (sending thousands of requests per second) can overwhelm a server, leading to a Denial of Service (DoS) for legitimate users.
- Unauthorized Infrastructure Control: In DevOps environments, webhooks often trigger builds, deployments, or infrastructure changes. Compromising these can give an attacker full control over your production environment.
How to Secure Webhooks: Best Practices for Developers
To build resilient and secure webhook integrations, follow these industry-standard mitigation strategies.
1. Implement HMAC Signatures
The gold standard for webhook security is Hash-based Message Authentication Code (HMAC). The provider and the listener share a "secret key." The provider signs the payload using this key and sends the signature in a header (e.g., X-Signature).
Example: Verifying a Signature in Node.js
const crypto = require('crypto');
function verifyWebhook(payload, headerSignature, secret) {
const expectedSignature = crypto
.createHmac('sha256', secret)
.update(payload)
.digest('hex');
// Use timingSafeEqual to prevent timing attacks
return crypto.timingSafeEqual(
Buffer.from(headerSignature),
Buffer.from(expectedSignature)
);
}
2. Use Timestamps to Prevent Replay Attacks
Include a timestamp in the signed header. When your server receives the request, check if the timestamp is too old (e.g., older than 5 minutes). If the signature covers the timestamp, an attacker cannot modify the timestamp to make an old request look new.
3. Implement IP Whitelisting
If the webhook provider publishes their IP ranges (like GitHub or Stripe), configure your firewall or web server to only accept requests from those specific IP addresses. While IP addresses can theoretically be spoofed, it adds a significant layer of difficulty for most attackers.
4. Enforce Strict Input Validation
Treat every webhook payload as untrusted user input. Use a schema validator (like Joi or Zod) to ensure the JSON structure matches exactly what you expect. If the payload contains URLs, ensure they belong to an allowed list of domains and do not point to internal IP addresses.
5. Mutual TLS (mTLS)
For high-security environments, consider Mutual TLS. This requires both the sender and the receiver to present a valid certificate. This ensures that only the authorized provider can even establish a connection to your webhook listener.
Conclusion
Webhooks are a powerful tool for building interconnected systems, but their simplicity is deceptive. Because they sit on the boundary between your internal network and the public internet, they are a high-value target for hackers. By understanding the mechanics of SSRF, replay attacks, and forged events, you can implement robust defenses like HMAC signatures and strict input validation.
Security is not a one-time setup but a continuous process of monitoring and improvement. As your attack surface grows, keeping track of every exposed endpoint becomes increasingly difficult.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.