What is Time-of-Check to Time-of-Use (TOCTOU) Flaw? Ways to Exploit, Examples and Impact
Discover how Time-of-Check to Time-of-Use (TOCTOU) flaws create race conditions. Learn to identify, exploit, and mitigate these vulnerabilities in your code.
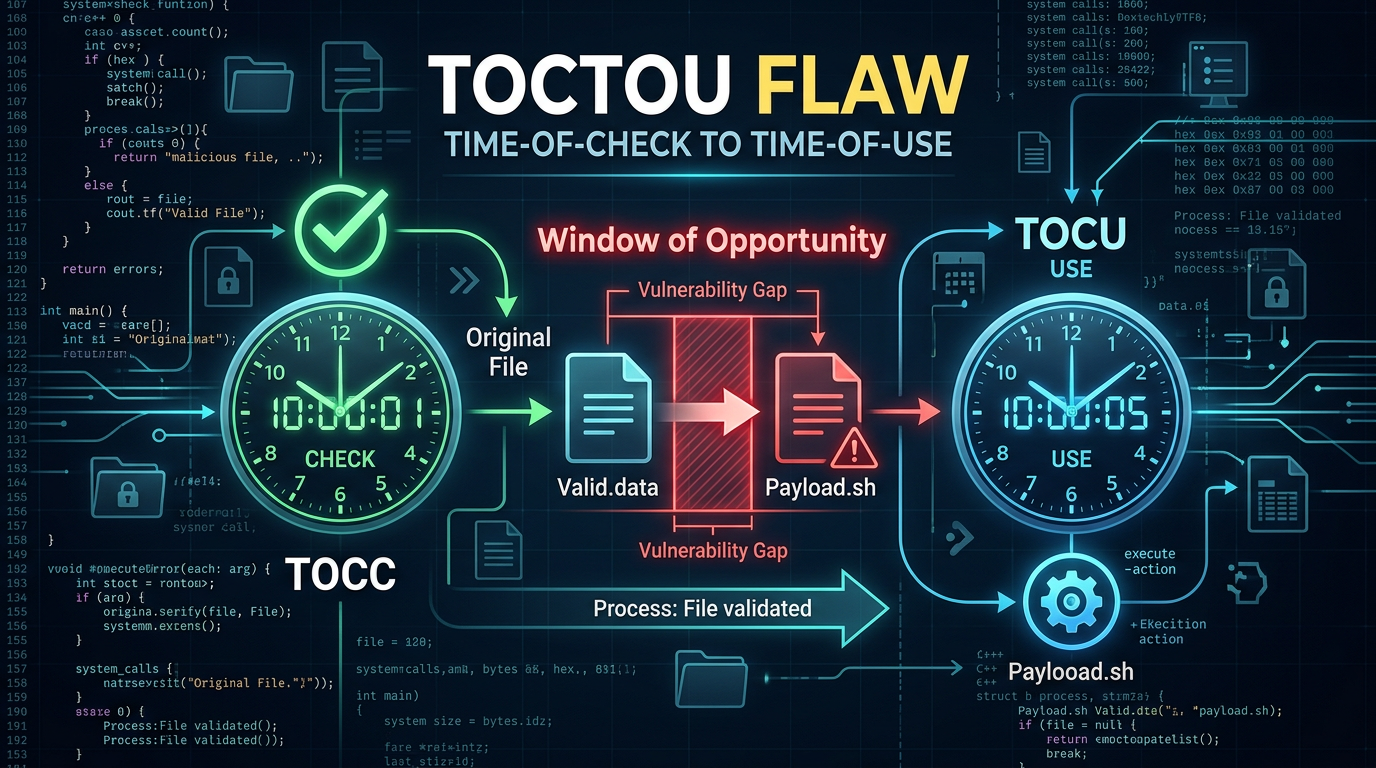
In the world of cybersecurity, timing is often everything. While many vulnerabilities arise from poor input validation or weak encryption, a specific class of software bugs known as race conditions relies entirely on the sequence and timing of events. Among these, the Time-of-Check to Time-of-Use (TOCTOU) flaw stands out as one of the most persistent and dangerous. A TOCTOU vulnerability occurs when a program checks the state of a resource (like a file or a database record) and then performs an action based on that state, but the state changes between the "check" and the "use."
Understanding TOCTOU is essential for any developer or security professional because it challenges the assumption that code executes in a perfectly linear, isolated environment. In modern multi-tasking operating systems, processes are constantly interrupted, and files can be manipulated by external actors at any microsecond. This blog post will dive deep into what TOCTOU flaws are, how they are exploited, real-world examples, and how you can defend your infrastructure against them.
Understanding the Core Logic of TOCTOU
To grasp the concept of TOCTOU, think of it as a race between a legitimate program and an attacker. The vulnerability is fundamentally a "race condition." In a typical execution flow, a program performs two distinct steps:
- The Check: The program verifies a condition (e.g., "Does this user have permission to write to this file?").
- The Use: The program performs an operation based on the result of the check (e.g., "Open the file and write data").
The "window of vulnerability" is the time elapsed between these two steps. If an attacker can change the resource during this window, the program will perform the action on a resource that no longer meets the original criteria.
The Classic File System Example
In Unix-like systems, a classic TOCTOU scenario involves the access() system call and the open() system call. The access() function checks if the real user ID of the process has permission to access a file. The open() function actually opens the file.
Consider a setuid program (a program that runs with root privileges) that wants to let a normal user write to a file, but only if that user already has permission to do so. The code might look like this:
if (access("/tmp/user_file", W_OK) == 0) {
// The check passed, now we use the file
int fd = open("/tmp/user_file", O_WRONLY);
write(fd, buffer, sizeof(buffer));
close(fd);
}
On the surface, this looks secure. However, an attacker can exploit the gap between access() and open(). If the attacker replaces /tmp/user_file with a symbolic link (symlink) to /etc/passwd immediately after the access() check succeeds but before open() is called, the program will unwittingly write user-controlled data into a critical system file with root privileges.
How to Exploit TOCTOU Flaws
Exploiting a TOCTOU flaw requires the attacker to "win the race." This involves high-speed manipulation of the target resource. While it may seem difficult to time an action down to the millisecond, attackers use several techniques to increase their chances of success.
1. Winning the Race via Loops
Since the window of vulnerability is small, an attacker typically runs a script in a continuous loop. One process attempts to toggle a file between a safe version and a malicious symlink, while another process repeatedly executes the vulnerable program. Eventually, the timing aligns perfectly.
# Attacker script snippet
while true; do
touch /tmp/user_file
rm /tmp/user_file
ln -s /etc/shadow /tmp/user_file
rm /tmp/user_file
done
2. File System Stressing
An attacker can artificially widen the window of vulnerability by slowing down the system. By consuming CPU resources or performing heavy I/O operations, the attacker ensures that the operating system's scheduler takes longer to switch back to the vulnerable process, giving the attacker more time to swap the resource.
3. Exploiting Multi-core Systems
On modern multi-core processors, the "check" and the "attacker's swap" can happen literally at the same time on different cores. This makes race conditions even more prevalent in multi-threaded applications where shared memory or shared variables are accessed without proper locking mechanisms.
Real-World Examples and Scenarios
TOCTOU flaws are not limited to C programs or file systems; they manifest in web applications, database transactions, and even hardware.
Example 1: Web Application Double-Spending
In financial applications or e-commerce platforms, TOCTOU can lead to "double-spending" or balance manipulation. Imagine a function that processes a withdrawal:
# Vulnerable Python Pseudo-code
def withdraw_funds(user_id, amount):
balance = db.get_balance(user_id)
if balance >= amount:
# TOCTOU Window: What if another request happens here?
new_balance = balance - amount
db.update_balance(user_id, new_balance)
return True
return False
If a user sends two withdrawal requests simultaneously, both threads might read the same initial balance. Both will pass the if balance >= amount check. Both will then subtract the amount and update the database. If the user had $100 and tried to withdraw $100 twice, they might end up with a successful $200 withdrawal because the second "check" happened before the first "use" (the update) was finalized.
Example 2: Temporary File Vulnerabilities
Many applications create temporary files in shared directories like /tmp. If an application checks that a filename doesn't exist and then creates it, an attacker can create a symlink with that name in between those steps. This can lead to the application overwriting sensitive files or following a link to a location where the attacker has read/write access.
The Impact of TOCTOU Vulnerabilities
The consequences of a successful TOCTOU exploit can be devastating, depending on the privileges of the vulnerable application.
- Privilege Escalation: As seen in the
access()/open()example, a TOCTOU flaw in a privileged process can allow an unprivileged user to gain root or administrator access. - Data Corruption: By swapping files or database records, attackers can corrupt critical system data, leading to application crashes or permanent data loss.
- Unauthorized Data Access: Attackers can redirect a program's output to a file they control, allowing them to steal sensitive information like passwords, API keys, or personal user data.
- Bypassing Security Controls: TOCTOU can be used to bypass sandbox restrictions or anti-virus scans. If a file is scanned (the check) and then executed (the use), an attacker can swap the file with malware after the scan completes.
How to Prevent and Mitigate TOCTOU Flaws
Preventing TOCTOU requires a shift in how developers think about resource handling. The goal is to make operations "atomic"—meaning the check and the use happen as a single, indivisible step.
1. Use Atomic System Calls
Instead of checking a property and then acting on it, use system calls that perform both at once. For example, in file operations, instead of access() followed by open(), use open() with specific flags.
If you want to ensure you are creating a new file and not following a symlink, use the O_EXCL and O_CREAT flags in C:
int fd = open("/tmp/new_file", O_WRONLY | O_CREAT | O_EXCL, 0600);
if (fd < 0) {
// File already exists or an error occurred, handle safely
}
2. Work with File Descriptors, Not Paths
Once a file is opened, use its file descriptor (an integer referring to the open file object) rather than its string path for subsequent operations like changing permissions (fchmod) or checking status (fstat). Paths can be changed via symlinks, but a file descriptor stays pointed at the original file that was opened.
3. Implement Proper Locking
In multi-threaded or multi-process environments, use mutexes, semaphores, or file locks (flock). In database environments, use transactions with appropriate isolation levels (like SELECT FOR UPDATE) to ensure that a record cannot be changed by another process until the current operation is finished.
4. Avoid Shared Directories
Whenever possible, avoid performing security-sensitive operations in directories where untrusted users have write access (like /tmp). If you must use a temporary directory, create a private subdirectory with restricted permissions first.
Conclusion
Time-of-Check to Time-of-Use (TOCTOU) flaws serve as a stark reminder that software does not exist in a vacuum. The interaction between code, the operating system, and the file system creates complex timing dynamics that attackers are eager to exploit. By understanding the "window of vulnerability" and adopting atomic programming patterns, developers can close the door on race conditions.
In a modern infrastructure, identifying these subtle logic flaws manually is nearly impossible. Automated tools and continuous monitoring are required to maintain a strong security posture. Understanding your external footprint is the first step in identifying where these vulnerabilities might be hiding in your exposed services.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon. Jsmon provides the visibility needed to track changes in your infrastructure, helping you spot the architectural weaknesses that lead to TOCTOU and other complex race conditions.



