What is Stack Smashing? Ways to Exploit, Examples and Impact
Stack smashing remains one of the most foundational concepts in software security and exploit development. Despite decades of research and the implementation of numerous hardware and software defenses, buffer overflows that lead to stack smashing continue to surface in modern applications, particularly those written in low-level languages like C and C++. Understanding how these attacks work is essential for any aspiring security professional or developer looking to write robust, secure code.
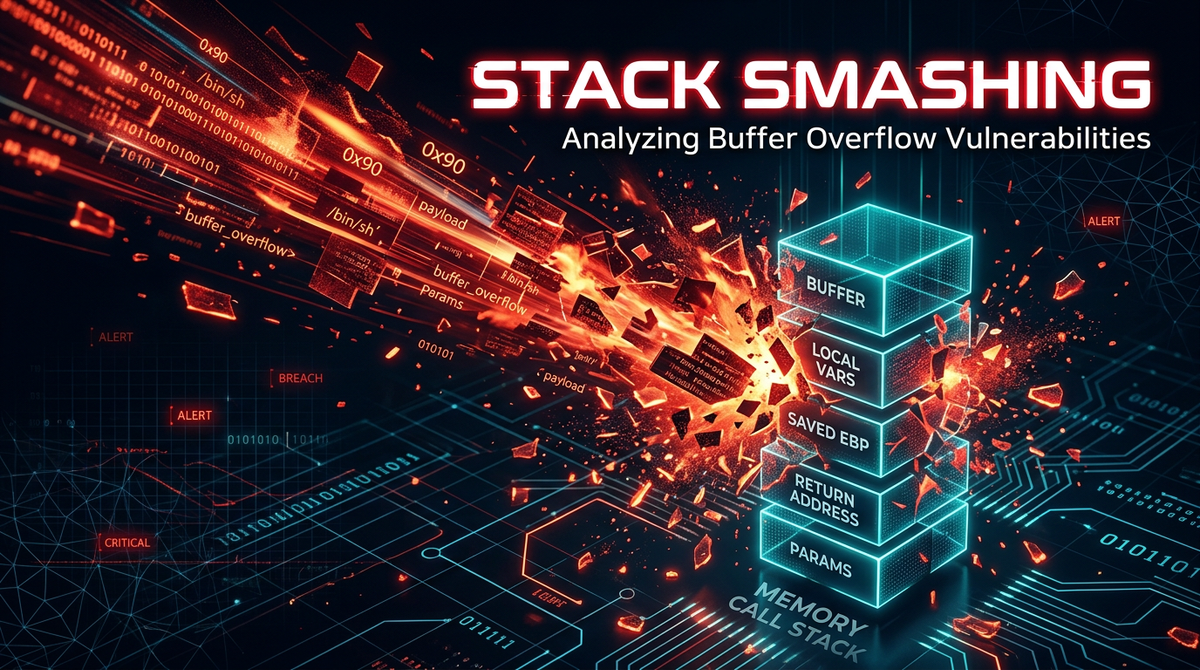
Understanding the Call Stack
To understand stack smashing, we must first understand the "stack" itself. In computer architecture, the stack is a region of memory that stores temporary data created by each function (or method) in a program. It operates on a Last-In, First-Out (LIFO) basis. When a function is called, a new block of memory called a "stack frame" is pushed onto the stack. This frame contains the function's local variables, its arguments, and—crucially—the return address.
The return address is the memory location the CPU should jump back to once the current function finishes executing. In a standard x86 architecture, the stack grows downward (from high memory addresses to low memory addresses). The Stack Pointer (ESP/RSP) tracks the top of the stack, while the Base Pointer (EBP/RBP) marks the start of the current stack frame.
What is Stack Smashing?
Stack smashing is a specific type of buffer overflow attack where an attacker provides more data to a program than its internal buffer can hold. Because the stack grows downward and local variables are written upward, an unchecked input can "overflow" its allocated space and overwrite adjacent data.
If the input is long enough, it eventually reaches the saved return address on the stack. By overwriting this return address with a memory address of their choosing, an attacker can hijack the program's execution flow. Instead of returning to the legitimate calling function, the program jumps to whatever code the attacker has specified—often a malicious payload known as shellcode.
How Stack Smashing Works: A Technical Walkthrough
To visualize this, let's look at a classic vulnerable C code snippet. Many legacy C functions, such as strcpy(), gets(), and sprintf(), do not perform bounds checking. They continue copying data until they encounter a null terminator, regardless of the destination buffer's size.
#include <string.h>
#include <stdio.h>
void vulnerable_function(char *str) {
char buffer[16];
// This is the vulnerability: strcpy does not check the size of str
strcpy(buffer, str);
}
int main(int argc, char *argv[]) {
if (argc > 1) {
vulnerable_function(argv[1]);
}
return 0;
}
In the example above, the buffer is allocated 16 bytes on the stack. If a user provides an input string of 10 characters, everything works as expected. However, if a user provides an input of 32 characters, the strcpy function will write past the 16-byte boundary.
On the stack, the memory layout for vulnerable_function looks roughly like this (from low to high addresses):
- Local variables (
buffer[16]) - Saved Base Pointer (EBP)
- Saved Return Address (EIP)
- Function Arguments
When the overflow occurs, the data fills the 16 bytes of the buffer, then overwrites the saved EBP, and finally overwrites the saved EIP (the return address). When the function reaches its ret instruction, the CPU pops the value at the EIP location and attempts to execute code at that address. If the attacker has placed the address of their shellcode there, the system is compromised.
A Practical Example of a Stack Overflow Exploit
Let's walk through a conceptual exploit scenario. Suppose an attacker wants to gain a command shell on a target system. They would follow these general steps:
1. Determining the Offset
First, the attacker needs to know exactly how many bytes are required to reach the return address. They might use a debugger like GDB and provide a unique pattern (e.g., "AAAABBBBCCCC...") to the program. If the program crashes and the debugger shows that the EIP register contains 0x44444444 (the hex for "DDDD"), the attacker knows that the return address starts at the 20th byte (16 bytes for the buffer + 4 bytes for the saved EBP).
2. Crafting the Payload
The payload usually consists of three parts:
- The NOP Sled: A series of "No Operation" instructions (
0x90in x86). This provides a "landing zone." If the return address points anywhere within this sled, the CPU will simply slide down until it hits the actual shellcode. - The Shellcode: A small piece of machine code designed to perform a specific task, such as spawning
/bin/shor opening a reverse shell connection back to the attacker. - The Target Address: The memory address that points back into the NOP sled, which is used to overwrite the original return address.
3. Execution
The attacker executes the program with the crafted payload as input.
# Conceptual payload structure
./vulnerable_program $(python -c 'print "\x90"*100 + SHELLCODE + "\x41"*OFFSET + TARGET_ADDRESS')
When vulnerable_function finishes, it "returns" to the TARGET_ADDRESS, slides down the NOPs, executes the shellcode, and grants the attacker control over the process.
The Impact of Stack Smashing Attacks
The consequences of a successful stack smashing attack are severe. Because the attacker gains control over the instruction pointer, they can execute arbitrary code with the same privileges as the running process.
- Remote Code Execution (RCE): If the vulnerable application is a network service (like a web server or mail server), an attacker can take over the entire server from across the internet.
- Privilege Escalation: If a local user exploits a SUID-root binary, they can elevate their permissions to become the root user, gaining total control over the local machine.
- Data Exfiltration: Attackers can use code injection to read sensitive files, access databases, or steal cryptographic keys.
- Denial of Service (DoS): Even if the attacker fails to gain control, overwriting the stack usually causes the program to crash, disrupting service availability.
Historical examples like the Morris Worm in 1988 used stack smashing in the fingerd daemon to spread across the early internet, demonstrating the massive scale at which these vulnerabilities can be exploited.
Modern Mitigations and Protections
Because stack smashing is so dangerous, modern operating systems and compilers have introduced several defensive layers.
1. Stack Canaries (Stack Guard)
A stack canary is a small, random value placed on the stack just before the return address. Before a function returns, the program checks if the canary value is still the same. If an overflow has occurred, the canary will be overwritten, the program will detect the change, and it will terminate immediately before the malicious return address can be used. Compilers like GCC enable this by default with the -fstack-protector flag.
2. Address Space Layout Randomization (ASLR)
ASLR randomizes the memory addresses used by the system, including the base of the stack, heap, and libraries. This makes it significantly harder for an attacker to predict the TARGET_ADDRESS needed for their exploit. Without knowing where the shellcode is located in memory, the attacker cannot reliably redirect execution.
3. Data Execution Prevention (DEP) / NX Bit
DEP (or the No-Execute bit) marks certain areas of memory, like the stack, as non-executable. Even if an attacker successfully overwrites the return address to point to their shellcode on the stack, the CPU will refuse to execute it, causing a segmentation fault instead. This forces attackers to use more complex techniques like Return-Oriented Programming (ROP).
4. Safe Coding Practices
The most effective defense is writing secure code from the start. Developers should avoid dangerous functions and use safer alternatives:
- Use
strncpy()instead ofstrcpy(). - Use
fgets()instead ofgets(). - Use
snprintf()instead ofsprintf(). - Always validate the length of user-provided input before processing it.
Conclusion
Stack smashing is a classic exploit technique that highlights the critical importance of memory safety. While modern mitigations like ASLR and Stack Canaries make exploitation much more difficult, they are not silver bullets. Attackers continue to find creative ways to bypass these defenses, making proactive monitoring and secure development practices more important than ever.
As applications grow in complexity, their attack surface expands. Understanding the low-level mechanics of how memory can be manipulated is the first step toward building more resilient systems. By combining secure coding standards with modern compiler protections and robust infrastructure monitoring, organizations can significantly reduce their risk of falling victim to these devastating attacks.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



