What is Payment Gateway Bypass? Ways to Exploit, Examples and Impact
Learn how to identify and prevent payment gateway bypass vulnerabilities including parameter tampering and webhook spoofing in this technical guide.
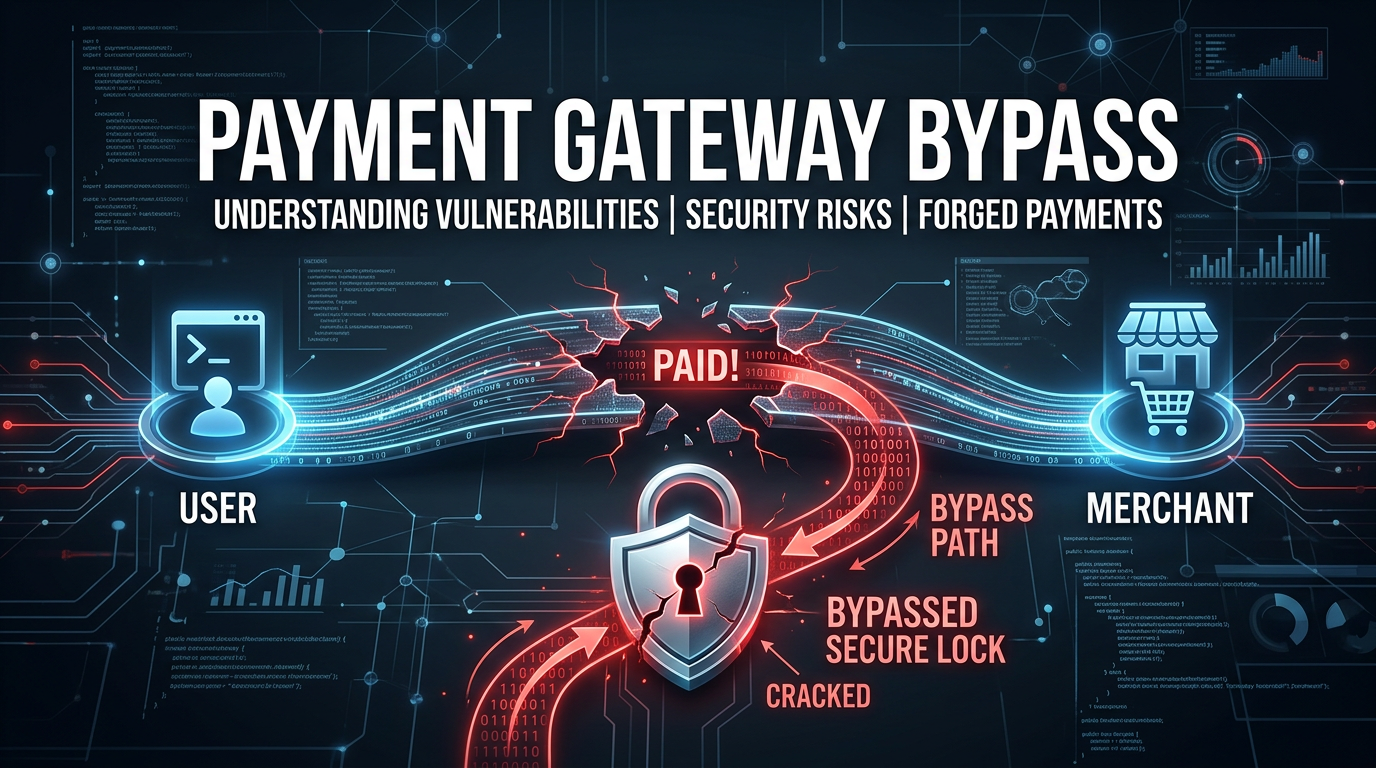
In the modern digital economy, the payment gateway is the bridge between a customer's bank account and a merchant's revenue. For businesses, it is the most critical piece of infrastructure, yet for attackers, it represents the ultimate target: the point where data turns into direct financial gain. A payment gateway bypass occurs when an attacker manipulates the checkout process to receive goods or services without paying the full price, or sometimes without paying at all. Understanding these vulnerabilities is essential for developers, security researchers, and business owners who rely on Jsmon to monitor their external attack surfaces.
Understanding the Payment Gateway Workflow
Before diving into the exploits, we must understand how a standard payment transaction works. Typically, the process involves three main parties: the Client (user's browser), the Merchant Server (the e-commerce website), and the Payment Gateway (e.g., Stripe, PayPal, Razorpay).
- Initiation: The user adds items to a cart and clicks "Checkout."
- Order Creation: The Merchant Server calculates the total and creates an order ID in its database.
- Payment Request: The Merchant Server sends the order details (amount, currency, order ID) to the Payment Gateway. This often happens via a client-side redirect or a server-side API call.
- Transaction: The user enters their credit card details on the Gateway's secure page.
- Verification & Callback: The Gateway processes the payment and sends a response back to the Merchant Server. This is usually done via a "Return URL" (client-side) and a "Webhook" (server-side).
- Fullfilment: If the Merchant Server receives a "Success" signal, it marks the order as paid and ships the product.
A bypass occurs when an attacker interferes with any of these steps to trick the Merchant Server into believing a payment was successful when it was not.
Common Methods to Exploit Payment Gateways
1. Parameter Tampering (Price Manipulation)
This is the most common and "classic" form of payment bypass. It occurs when the Merchant Server trusts the price sent from the client-side browser instead of validating it on the backend. If the price is passed in a hidden HTML field or a JavaScript variable, an attacker can intercept the request using a proxy tool like Burp Suite and modify the value.
Example Scenario:
An attacker sees a request like this being sent to the payment gateway:
POST /v1/checkout HTTP/1.1
Host: api.paymentgateway.com
Content-Type: application/x-www-form-urlencoded
item_id=sku_9921&amount=1500.00¤cy=USD&callback_url=https://merchant.com/success
The attacker changes amount=1500.00 to amount=0.01. If the merchant's backend only checks if the payment was "Successful" but doesn't verify that the amount paid matches the price of the item in the database, the attacker gets a $1,500 product for a penny.
2. Manipulating the Return URL (Client-Side Callback)
Many legacy or poorly implemented systems rely on the client-side redirect to confirm a payment. After a successful transaction, the gateway redirects the user to https://merchant.com/payment/success?order_id=123.
If the merchant server assumes that reaching this URL implies a successful payment, an attacker can simply skip the payment page entirely and navigate directly to the success URL.
Payload Example:
An attacker might try to guess the order ID or find their own pending order ID and append it to the success path:https://merchant.com/checkout/complete?status=paid&orderid=8872
Without server-side verification (checking the status via the gateway's API), the system may trigger the fulfillment logic immediately.
3. Webhook and IPN Spoofing
Webhooks (or Instant Payment Notifications - IPN) are server-to-server messages sent by the gateway to the merchant. They are the "source of truth." However, if the merchant does not verify that the webhook actually came from the trusted gateway, an attacker can forge a webhook request.
The Vulnerability:
The merchant has an endpoint at https://merchant.com/api/webhooks/paypal. The merchant expects a JSON body like this:
{
"event": "payment.captured",
"data": {
"order_id": "ORD-990",
"status": "completed",
"amount": "500.00"
}
}
If the merchant doesn't check for a cryptographic signature (like an HMAC header) or doesn't whitelist the Gateway's IP addresses, an attacker can send this exact JSON payload directly to the webhook endpoint using curl:
curl -X POST https://merchant.com/api/webhooks/paypal \
-H "Content-Type: application/json" \
-d '{"event": "payment.captured", "data": {"order_id": "MY_PENDING_ORDER", "status": "completed"}}'
4. Currency Switching Exploits
In some cases, the system validates the amount but fails to validate the currency. If an item costs 100 GBP (British Pounds), an attacker might change the currency code to a much weaker currency, such as the Iranian Rial (IRR) or the Vietnamese Dong (VND).
If the backend checks if (paid_amount == 100), it returns true. However, 100 VND is worth a fraction of a cent compared to 100 GBP. This logic flaw allows for massive discounts through simple parameter manipulation.
5. Race Conditions in Wallet Top-ups
For platforms that use internal wallets, race conditions can lead to a balance bypass. If an attacker sends multiple simultaneous requests to "confirm" a single payment transaction, a poorly designed database logic might credit the user's wallet multiple times for a single payment.
Technical Example:
An attacker captures the "Confirm Payment" request and uses a tool like Turbo Intruder to send 50 identical requests in the same millisecond. If the code looks like this:
# Vulnerable Logic
if payment_valid(transaction_id):
current_balance = user.get_balance()
user.update_balance(current_balance + amount)
Because the requests happen so fast, multiple threads might read the same current_balance before any of them have finished updating it, leading to an inflated balance.
Real-World Impact of Payment Bypasses
The impact of a payment gateway bypass is almost always "Critical" in a bug bounty context or a risk assessment.
- Direct Revenue Loss: The most immediate impact is the loss of money for the goods or services provided.
- Inventory Exhaustion: Attackers can use scripts to "purchase" an entire stock of limited-edition items for free, preventing legitimate customers from buying them.
- Compliance Violations: Failure to secure payment flows can lead to the loss of PCI-DSS certification, resulting in heavy fines and the inability to process credit cards.
- Reputational Damage: If news leaks that a platform can be easily exploited for free goods, it destroys consumer trust and brand equity.
How to Prevent Payment Gateway Bypass
Securing the payment flow requires a "Zero Trust" approach toward any data coming from the client browser. Here are the best practices for developers:
1. Never Trust Client-Side Data
Always store the price of your items in a secure server-side database. When initiating a payment, the Merchant Server should pull the price from the database based on the item_id, rather than accepting a price parameter from the frontend.
2. Implement Server-Side Verification
Never rely on the redirect to the "Success" page. Before marking an order as paid, the Merchant Server must call the Payment Gateway's API (e.g., GET /v1/payments/{id}) to verify the status and the exact amount paid.
3. Secure Your Webhooks
Webhooks must be protected using at least two of the following methods:
- Signature Verification: Most modern gateways (Stripe, Adyen) include a signature in the header (e.g.,
X-Hub-Signature). Re-calculate this signature on your server using your secret key to ensure the payload hasn't been tampered with. - IP Whitelisting: Only allow POST requests to your webhook endpoint from the Gateway's known IP ranges.
- Idempotency: Use idempotency keys to ensure that the same transaction ID cannot be processed twice, preventing race conditions.
4. Use Cryptographic Hashes for Form Data
If you must pass data through the client, use a checksum or hash. For example, concatenate amount + currency + order_id + secret_key and create a SHA-256 hash. Send this hash along with the data. The gateway (or your return handler) can then re-hash the data to ensure nothing was changed in transit.
Conclusion
Payment gateway bypasses are a reminder that even the most secure third-party integrations can be undermined by weak implementation logic on the merchant's side. From simple parameter tampering to complex race conditions, attackers have numerous avenues to exploit the checkout process. By moving validation to the server-side, verifying webhook signatures, and maintaining a strict inventory of your external assets, you can significantly reduce your risk profile.
To proactively monitor your organization's external attack surface and catch exposures in your payment endpoints before attackers do, try Jsmon.



