What is Parameter Tampering? Ways to Exploit, Examples and Impact
Learn how parameter tampering works, see real-world exploitation examples, and discover how to prevent this critical web vulnerability.
Web applications are built on the exchange of data between a client—usually a web browser—and a server. This exchange relies on parameters to communicate everything from user preferences to the contents of a shopping cart. However, when a web application trusts these parameters implicitly without server-side verification, it opens the door to a critical vulnerability known as Parameter Tampering. In this guide, we will explore what parameter tampering is, the various ways it can be exploited, and how you can protect your infrastructure.
What is Parameter Tampering?
Parameter tampering is a form of web-based attack where an intruder modifies data sent between the client and the server to change application behavior or access unauthorized information. This data can reside in URL query strings, HTTP headers, cookies, or form fields.
The core of the issue lies in the stateless nature of the HTTP protocol. Because the server often treats each request as an independent event, it may rely on the data provided within that request to make logic decisions. If an attacker can manipulate that data before it reaches the server, they can trick the application into performing actions it wasn't intended to do, such as lowering the price of an item or escalating their own user privileges.
The Mechanics of the Attack
At its simplest, parameter tampering involves capturing a request, modifying a specific value, and forwarding it to the server. Attackers use tools like browser developer tools or intercepting proxies (such as Burp Suite) to view and edit these parameters. Since the modification happens on the client side or in transit, traditional client-side validations (like JavaScript checks) are completely bypassed.
Common Attack Vectors for Parameter Tampering
To understand how to defend against these attacks, we must first look at where these parameters are typically found and how they are manipulated.
1. URL Query Strings
Query strings are the most visible parameters, appearing directly in the URL after a question mark. For example:https://example.com/view_profile?user_id=5521
An attacker can simply change user_id=5521 to user_id=5522 in the browser's address bar. If the application does not check if the current session has permission to view profile 5522, the attacker has successfully performed an Insecure Direct Object Reference (IDOR) attack via parameter tampering.
2. Hidden Form Fields
Developers often use hidden HTML fields to store data that they don't want the user to see or edit directly, such as product IDs or prices. A typical form might look like this:
<form action="/checkout" method="POST">
<input type="hidden" name="product_id" value="99">
<input type="hidden" name="price" value="499.00">
<input type="submit" value="Buy Now">
</form>
While the user cannot see the price on the page, they can easily inspect the source code or use an intercepting proxy to change the value of price from 499.00 to 0.01 before submitting the form.
3. HTTP Headers
HTTP headers contain metadata about the request, such as the User-Agent, Referer, or custom headers used by the application logic. If an application uses the Referer header to validate where a request originated or uses a custom header like X-Admin-Access: false to determine permissions, an attacker can easily spoof these values to bypass security controls.
4. Cookies
Cookies are frequently used to store session identifiers and user preferences. However, some poorly designed applications store security-sensitive information in cookies, such as role=user. By modifying the cookie value to role=admin, an attacker might gain administrative access to the web portal.
Technical Examples and Exploitation Scenarios
Let’s dive into some practical, technical scenarios to see how parameter tampering looks in the real world.
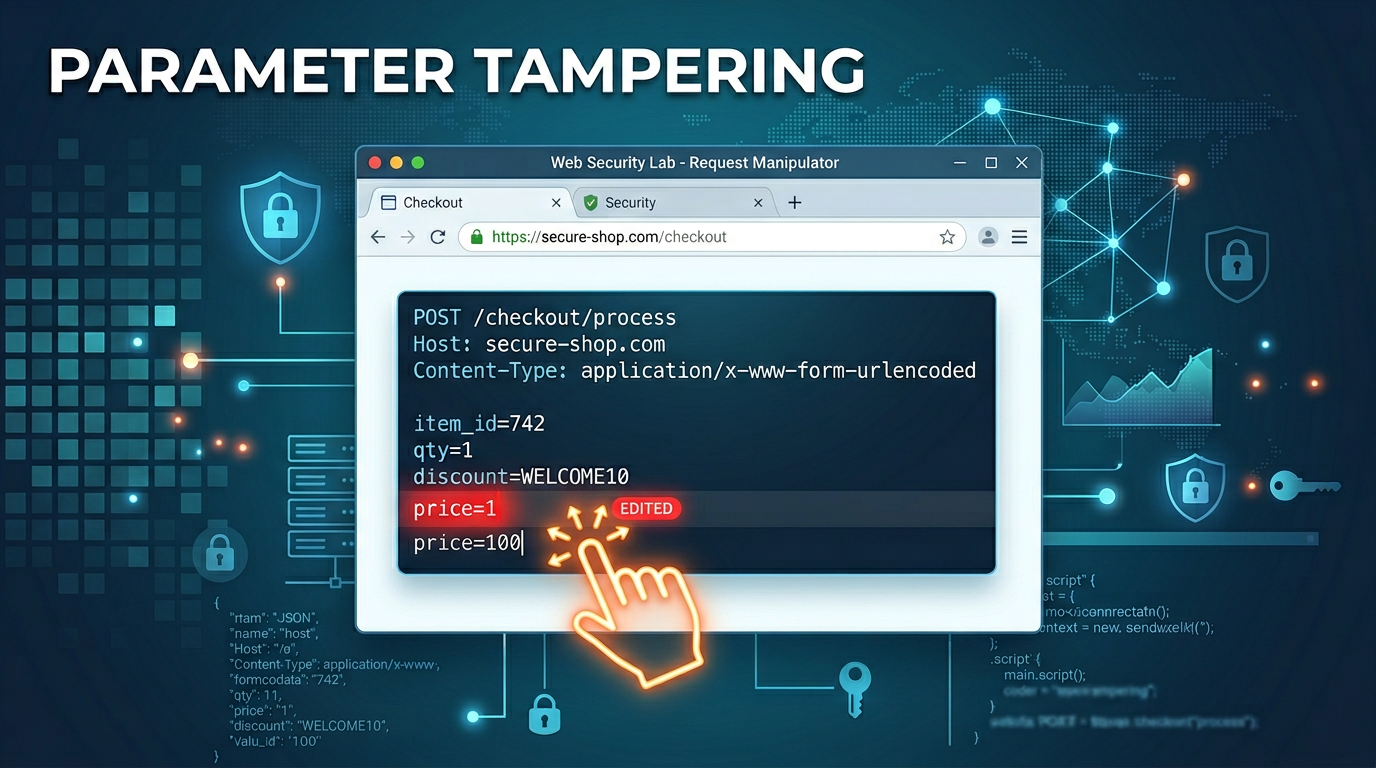
Example 1: Price Manipulation in E-commerce
Imagine an e-commerce site where the final checkout request looks like this:
POST /api/v1/order HTTP/1.1
Host: shop.example.com
Content-Type: application/x-www-form-urlencoded
item_id=prod_882&quantity=1&total_amount=1500.00¤cy=USD
In this case, the application is trusting the client to tell it how much the order costs. An attacker intercepts this request and modifies the total_amount parameter:
POST /api/v1/order HTTP/1.1
Host: shop.example.com
Content-Type: application/x-www-form-urlencoded
item_id=prod_882&quantity=1&total_amount=1.00¤cy=USD
If the server-side code simply processes the payment for the amount provided in the total_amount parameter without re-calculating the price based on the item_id in the database, the attacker gets a $1500 product for $1.
Example 2: Bypassing Quantity Limits
Some applications have business logic constraints, such as "maximum 5 items per customer." An attacker might find a parameter that controls this limit.
Original Request:
POST /add-to-cart HTTP/1.1
item_id=101&qty=5
By tampering with the qty parameter to a negative value or a very large number, the attacker might trigger unexpected behavior. For instance, sending qty=-1 might result in a credit to the user's account or bypass a validation check that only looks for numbers greater than 5.
Example 3: Privilege Escalation via Cookie Tampering
A web application uses a cookie to track the user's subscription tier.
GET /premium-content HTTP/1.1
Host: example.com
Cookie: session_id=abc123xyz; sub_type=free
The server checks the sub_type cookie. If it says free, it denies access. If it says pro, it grants access. An attacker simply changes their cookie to sub_type=pro and refreshes the page. Without verifying this status against a backend database, the server grants access to restricted content.
The Impact of Parameter Tampering
The impact of successful parameter tampering can range from minor annoyances to catastrophic data breaches.
- Financial Loss: As seen in the price manipulation example, companies can suffer direct financial hits when attackers modify transaction values.
- Unauthorized Data Access: By tampering with IDs (IDOR), attackers can download sensitive documents, view other users' private information, or export entire databases.
- Privilege Escalation: Modifying role or permission parameters allows attackers to gain administrative control, leading to full system compromise.
- Data Corruption: Attackers might modify parameters that control database writes, leading to the corruption of records or the insertion of malicious payloads (like XSS) into the system.
- Reputational Damage: News of a vulnerability that allows users to cheat the system or access private data can destroy customer trust.
How to Prevent Parameter Tampering
Security must always be enforced on the server. Client-side controls are for user experience, not for security. Here are the primary methods to mitigate parameter tampering:
1. Never Trust Client Input
This is the golden rule of web security. Every piece of data coming from the client—whether it's a hidden field, a cookie, or a URL parameter—must be treated as untrusted.
2. Server-Side Validation and Re-calculation
In the e-commerce example, the server should never accept the price from the client. Instead, it should take the item_id, look up the price in a secure database, and calculate the total itself. If the client sends a total_amount, the server should compare it against its own calculation and reject the request if they don't match.
3. Use Session-Based State Management
Instead of storing roles or permissions in cookies or hidden fields, store them in a secure session object on the server. The client should only hold a session ID. When a request comes in, the server looks up the permissions associated with that session ID in its own memory or database.
4. Implement Integrity Checks (HMAC)
If you must pass sensitive data through the client, use a Hashed Message Authentication Code (HMAC). This involves signing the parameters with a secret key known only to the server. If an attacker changes a value, the signature will no longer match, and the server will reject the request.
// Example of creating a signed URL parameter
$price = "499.00";
$secret_key = "super-secret-key";
$signature = hash_hmac('sha256', $price, $secret_key);
// URL: /checkout?price=499.00&sig=a1b2c3d4...
5. Use Indirect Object References
Instead of using database IDs (like user_id=5521) in the URL, use mapped values or random UUIDs that are harder to guess. Furthermore, always verify that the authenticated user has the right to access the specific object requested.
Detecting Tampering with Modern Tools
For security professionals and developers, identifying these flaws early is essential. Manual testing with tools like Burp Suite allows you to intercept and modify every part of an HTTP request. Automated scanners can also help identify common patterns, such as parameters that appear to control prices or permissions.
However, the best defense is a proactive one. Understanding your external attack surface is the first step in identifying where an attacker might try to manipulate your application's logic. By mapping out every endpoint and parameter, you can ensure that validation logic is applied consistently across your entire infrastructure.
Conclusion
Parameter tampering is a deceptively simple yet highly effective attack vector. It exploits the fundamental trust that developers sometimes mistakenly place in the data sent by a user's browser. By understanding that every parameter—from a URL string to a hidden form field—is under the attacker's control, you can design more robust, secure applications. Always validate on the server, use secure session management, and never let the client dictate the rules of your business logic.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



