What is Null Pointer Dereference? Ways to Exploit, Examples and Impact
Memory safety remains one of the most significant challenges in modern software development. Among the various types of memory-related vulnerabilities, the Null Pointer Dereference (CWE-476) is perhaps the most well-known and frequently encountered. While it often results in a simple application crash, in certain environments—particularly within operating system kernels or embedded systems—it can lead to severe security breaches, including privilege escalation. Understanding how these vulnerabilities work is essential for any developer or security researcher using Jsmon to monitor their infrastructure's attack surface.
Understanding the Fundamentals: What is a Pointer?
To understand a null pointer dereference, we must first define what a pointer is. In low-level programming languages like C and C++, a pointer is a variable that stores the memory address of another value. Instead of holding data directly (like an integer or a character), the pointer "points" to a specific location in the system's RAM where that data resides.
The Concept of NULL
A NULL pointer is a special pointer value that is reserved to indicate that the pointer does not point to any valid memory location. In most environments, NULL is defined as the integer 0. When a pointer is set to NULL, it is effectively a signal to the program that the pointer is uninitialized or that a specific resource was not found.
Dereferencing a pointer means accessing the value stored at the memory address the pointer holds. If a pointer holds the address 0x1234, dereferencing it tells the CPU to go to 0x1234 and read the data there. However, if the pointer is NULL (holding address 0x0), and the program attempts to dereference it, the system encounters a problem because address 0x0 is typically reserved or protected by the operating system.
How Null Pointer Dereference Occurs
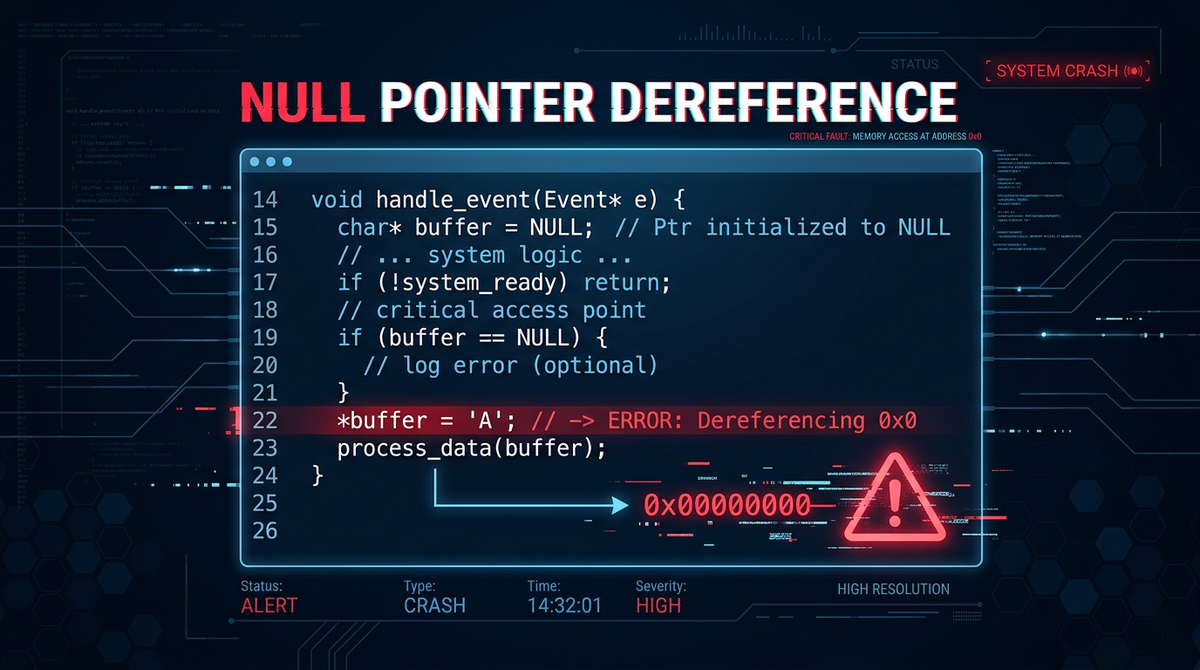
A null pointer dereference occurs when an application attempts to read or write to memory through a pointer that it expects to be valid, but which is actually NULL. This usually happens due to a logic error in the code where a check for NULL was omitted or bypassed.
Common Programming Errors Leading to NULL Dereferences
- Failure to Check Return Values: Many standard library functions, such as
malloc()in C, returnNULLif they fail to allocate the requested memory. If a developer assumes the allocation succeeded and immediately uses the pointer, a crash occurs. - Uninitialized Pointers: In some languages, local pointer variables are not automatically initialized to
NULL. They may contain "garbage" values from previous stack operations. If these are later set toNULLbut used before being assigned a valid address, a dereference error follows. - Race Conditions: In multi-threaded applications, one thread might set a pointer to
NULL(e.g., during a cleanup routine) while another thread is in the middle of using it. - Logic Flaws in Conditional Branches: A program might have a complex
if-elsestructure where one path initializes a pointer and another does not, but both paths eventually lead to code that dereferences that pointer.
The Technical Impact: From Crashes to Security Breaches
The impact of a null pointer dereference depends entirely on the context in which the application is running. While modern operating systems provide protections, the consequences can still be dire.
Denial of Service (DoS)
In most user-space applications (like a web browser or a text editor), a null pointer dereference results in a Segmentation Fault (SIGSEGV on Linux) or an Access Violation (on Windows). The operating system detects that the process is trying to access memory it doesn't own (the zero page) and terminates the process immediately. For a network service, this results in a Denial of Service. An attacker can repeatedly trigger the crash to keep the service offline, bypassing the monitoring capabilities of tools like Jsmon if the service is not resilient.
Privilege Escalation and Remote Code Execution (RCE)
While a crash is the most common outcome, null pointer dereferences can be exploited for more than just DoS, especially in Kernel Space. If a vulnerability exists within the OS kernel, a null pointer dereference can lead to a "Kernel Panic" or a Blue Screen of Death (BSOD), taking down the entire system.
Historically, attackers could exploit these by "mapping the zero page." If an attacker could convince the OS to allow them to allocate memory at address 0, they could place malicious code at that address. When the kernel then suffered a null pointer dereference, it would jump to address 0 and execute the attacker's code with kernel-level privileges. Modern operating systems have mitigated this by forbidding the mapping of the zero page (via mmap_min_addr in Linux), but variations of this technique still appear in specialized hardware and legacy systems.
Exploitation Techniques in Detail
Exploiting a null pointer dereference requires the attacker to control the environment around the crash. In modern exploitation, this often involves "grooming" the heap or manipulating the program state so that the NULL value is used in a way that influences program flow.
Mapping the Zero Page (The Classic Method)
In older Linux kernels (pre-2.6.23), a user could use the mmap system call to map a page of memory at address 0.
// Historical exploit concept (Mitigated in modern OS)
void *zero_page = mmap(0, 4096, PROT_READ | PROT_WRITE | PROT_EXEC,
MAP_FIXED | MAP_ANONYMOUS | MAP_PRIVATE, -1, 0);
if (zero_page == NULL) {
// Place shellcode here
memcpy(zero_page, "\x90\x90\xeb...", 100);
}
If a kernel driver subsequently had a bug like this:
struct device_ops *ops = get_ops(device);
ops->initialize(); // If ops is NULL, it calls address 0
The kernel would execute the shellcode at address 0. Today, this is much harder because mmap_min_addr prevents unprivileged users from mapping low memory addresses.
Practical Code Examples and Payloads
To better understand the vulnerability, let's look at how it manifests in actual code snippets.
C++ Example: The Classic Segmentation Fault
Consider a simple program that manages user profiles. If a profile is not found, the function returns NULL.
#include <iostream>
#include <string>
struct UserProfile {
std::string name;
int id;
};
UserProfile* findUser(int id) {
// Logic to find user... if not found:
return nullptr;
}
int main() {
UserProfile* user = findUser(999);
// VULNERABILITY: No check for nullptr before access
std::cout << "User Name: " << user->name << std::endl;
return 0;
}
When findUser returns nullptr, the expression user->name attempts to access memory at an offset from 0. This triggers an immediate crash.
Failed Memory Allocation
In embedded systems or high-load environments, memory allocation failure is a real possibility. Failing to handle this is a common source of vulnerabilities.
#include <stdlib.h>
#include <string.h>
void process_data(char *input) {
char *buffer = (char *)malloc(1024);
// VULNERABILITY: If malloc fails, buffer is NULL
// strcpy will attempt to write to address 0
strcpy(buffer, input);
free(buffer);
}
In this case, an attacker providing a very large input or triggering a memory-exhaustion state could cause the application to crash via strcpy writing to a null pointer.
Detection and Identification
Detecting null pointer dereferences is a standard part of the software development lifecycle. Several methods can be employed:
- Static Analysis (SAST): Tools like SonarQube, Coverity, or even compiler warnings (
-Wmaybe-uninitializedin GCC) can identify paths where a pointer might be used without aNULLcheck. - Dynamic Analysis (DAST) and Fuzzing: Fuzzers like AFL++ or libFuzzer provide random inputs to a program to trigger crashes. If the program crashes with a segmentation fault at address 0, a null pointer dereference is likely the cause.
- Manual Code Review: Security auditors look for functions that return pointers and trace their usage to ensure every call site includes a validation check.
For organizations managing large external infrastructures, identifying services that are prone to crashing is a key part of maintaining uptime. Using Jsmon helps in identifying changes in your infrastructure that might expose new, unvetted services to the public internet where they could be fuzzed by attackers.
Mitigation and Prevention Strategies
Preventing null pointer dereferences requires a combination of disciplined coding practices and modern language features.
Defensive Programming and Null Checks
The simplest defense is the "Null Check." Always validate pointers before use, especially those returned from external functions or library calls.
char *buffer = (char *)malloc(1024);
if (buffer == NULL) {
// Handle error gracefully
return;
}
Using Modern Programming Languages and Tools
Modern languages have introduced features that make null pointer dereferences almost impossible at compile-time:
- Rust: Uses the
Option<T>type. You cannot access the value inside anOptionwithout explicitly handling theNonecase. - C++ Smart Pointers:
std::unique_ptrandstd::shared_ptrhelp manage ownership, though they can still benullptr. However, modern C++ patterns encourage references (&) which cannot be null. - Java/C#: While they have
NullPointerException, they provideOptionalclasses and null-conditional operators (?.) to make checks more concise.
Conclusion
Null pointer dereference vulnerabilities are a classic example of how a simple oversight—forgetting a single if statement—can lead to significant stability and security issues. While the days of easy kernel exploitation via the zero page are largely over, the Denial of Service impact remains a potent threat to service availability. By employing rigorous testing, utilizing modern language features, and maintaining a clear view of your external assets, you can significantly reduce the risk posed by these memory errors.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



