What is Negative Quantity Vulnerability? Ways to Exploit, Examples and Impact
Learn how negative quantity vulnerabilities allow attackers to manipulate e-commerce totals. Explore exploit examples, technical impacts, and prevention tips.
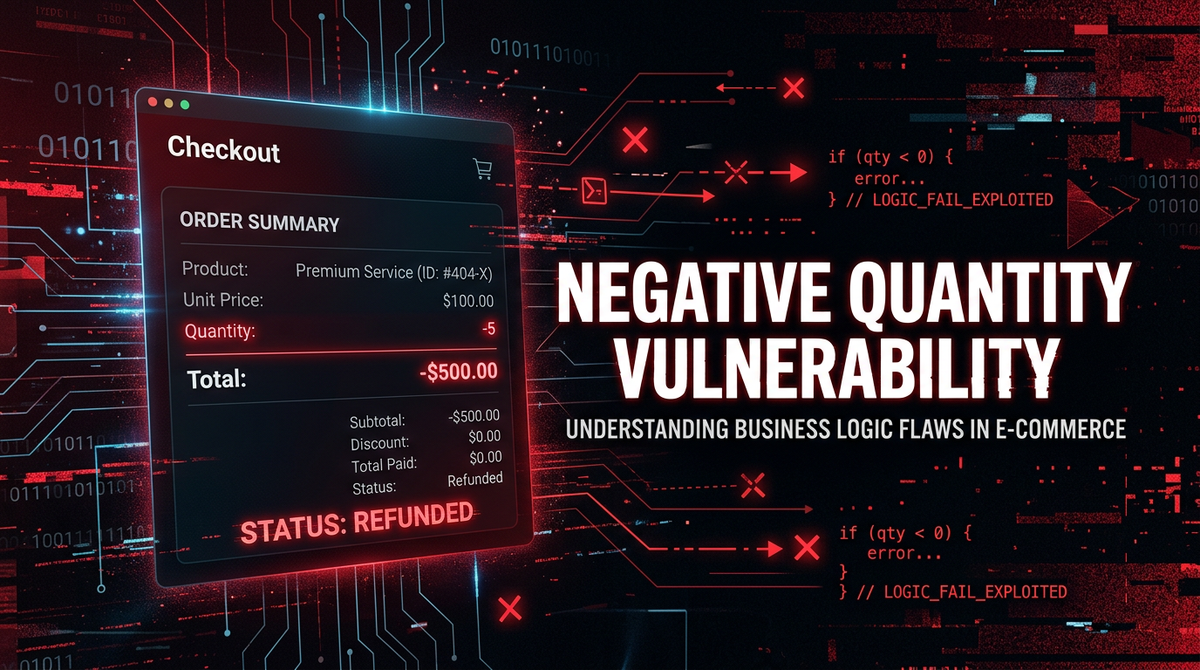
In the world of web application security, we often focus on complex technical exploits like memory corruption or sophisticated cryptographic attacks. However, some of the most devastating vulnerabilities arise from simple failures in business logic. One such classic example is the Negative Quantity Vulnerability. This flaw occurs when an application fails to properly validate numerical input, allowing a user to submit a negative value for a quantity field, which can lead to unintended financial transactions, inventory corruption, or unauthorized discounts.
Understanding the Core Concept
At its heart, a Negative Quantity Vulnerability is a type of business logic flaw. Business logic vulnerabilities are different from traditional injection attacks like SQL Injection or Cross-Site Scripting (XSS) because they don't necessarily involve "breaking" the code. Instead, they involve using the application's intended functionality in a way that the developers did not anticipate.
In an e-commerce setting, the application typically calculates the total price of an order using a simple formula: Total = Price * Quantity. Developers often assume that a user will only ever enter a positive integer for the Quantity. If the application does not explicitly check that the quantity is greater than zero on the server side, an attacker can input a negative number. This results in a negative total, which can confuse the payment processor or allow the attacker to "offset" the cost of other items in their shopping cart.
Why Does This Vulnerability Exist?
This vulnerability usually stems from a reliance on client-side validation. A developer might use an HTML5 input field like <input type="number" min="1">. While this prevents a regular user from typing a negative number in a standard browser, it provides zero security against a malicious actor. An attacker can easily bypass browser-level restrictions using a proxy tool like Burp Suite or by simply using the browser's developer tools to modify the request before it is sent to the server.
If the server-side code assumes the data is safe because it was "validated" in the UI, the logic breaks. The backend might process the negative value, perform the multiplication, and proceed to the checkout phase with a corrupted total. This is why Jsmon emphasizes the importance of monitoring the entire attack surface; even simple logic flaws can be discovered by mapping out how an application handles various inputs across its infrastructure.
How to Exploit Negative Quantity Vulnerabilities
Exploiting this flaw usually requires intercepting the HTTP request sent from the client to the server. Let's look at a few common scenarios.
1. The "Price Offset" Attack
Imagine an attacker wants to buy a high-end laptop worth $2,000 but only wants to pay $100. They add the laptop to their cart and then find a cheaper item, such as a USB cable worth $10. By manipulating the request, they add -190 USB cables to the cart.
The Calculation:
- Laptop: 1 * $2,000 = $2,000
- USB Cables: -190 * $10 = -$1,900
- Total: $100
If the system accepts this, the attacker successfully checks out and pays only $100 for a $2,000 laptop. The backend sees a positive total of $100 and authorizes the transaction, while the warehouse system might get confused by a request to "ship" -190 cables.
2. The "Negative Total" Refund Trick
In more extreme cases, an attacker might try to make the entire order total negative. Suppose an attacker adds -1 item worth $500 to their cart. The total becomes -$500. If the payment gateway is poorly integrated, it might interpret a negative charge as a refund. The attacker completes the "purchase," and instead of paying money, they receive $500 back onto their credit card or store credit balance.
3. Bypassing Minimum Order Requirements
Some sites offer free shipping or discounts if you spend over $100. An attacker could add $150 worth of items to trigger the discount and then add a negative quantity of a different item to bring the actual payable amount down to $5, while still retaining the "Free Shipping" or "$20 Off" coupon logic that was triggered by the initial high value.
Technical Example: Vulnerable Code vs. Secure Code
To understand this from a developer's perspective, let's look at a simplified example using Python and the Flask framework.
Vulnerable Implementation
In this snippet, the developer calculates the total without checking if the quantity is positive.
@app.route('/checkout', methods=['POST'])
def checkout():
item_id = request.form.get('item_id')
quantity = int(request.form.get('quantity')) # No validation!
price = get_item_price(item_id)
total_price = price * quantity
# Process payment with total_price
process_payment(total_price)
return f"Purchase complete! Total charged: {total_price}"
An attacker sends a POST request with quantity=-5. If the price is $10, total_price becomes -$50.
Secure Implementation
To fix this, the server must explicitly validate the range of the input.
@app.route('/checkout', methods=['POST'])
def checkout():
item_id = request.form.get('item_id')
try:
quantity = int(request.form.get('quantity'))
except ValueError:
return "Invalid input", 400
# Strict server-side validation
if quantity <= 0:
return "Quantity must be greater than zero", 400
price = get_item_price(item_id)
total_price = price * quantity
process_payment(total_price)
return f"Purchase complete! Total charged: {total_price}"
Real-World Impact
The impact of a Negative Quantity Vulnerability is primarily financial and operational.
- Direct Financial Loss: The most obvious impact is the loss of revenue when users buy products for prices lower than intended or effectively steal money through "negative" checkouts.
- Inventory Management Chaos: E-commerce platforms are usually linked to inventory management systems. A negative quantity order might increment the stock count instead of decrementing it, or it might cause database errors that crash the fulfillment pipeline.
- Reputational Damage: If news of such a loophole spreads on social media or "deal" forums, a company can face a massive influx of fraudulent orders in a very short time, leading to a PR nightmare and the need to cancel thousands of orders.
- Legal and Compliance Issues: Handling fraudulent transactions can lead to complications with payment processors like Stripe or PayPal, potentially resulting in higher transaction fees or the suspension of the merchant account.
How to Test for Negative Quantity Flaws
If you are a penetration tester or a developer auditing your own app, follow these steps to identify the flaw:
- Identify Input Fields: Look for any part of the application that accepts numerical input related to quantities, amounts, or prices.
- Intercept the Request: Use a tool like Burp Suite or OWASP ZAP. Add an item to your cart and capture the outgoing POST or PUT request.
- Modify the Payload: Change the quantity value to a negative integer (e.g.,
-1,-999, or even0). - Observe the Response:
- Does the cart update with a negative total?
- Does the checkout page show a reduced price?
- Does the application throw a generic error, or does it process the request?
- Test Boundary Conditions: Try extremely large negative numbers to see if you can trigger an integer underflow, though this is rarer in modern high-level languages.
Mitigation Strategies
Preventing this vulnerability requires a "defense in depth" approach. While client-side validation is good for user experience, server-side validation is mandatory for security.
- Server-Side Validation: Always verify that quantities are positive integers. Use strict type checking and range validation.
- Use Unsigned Integers: If your programming language or database supports it, use unsigned integer types for quantities. An unsigned integer cannot represent a negative value; attempting to store one will usually result in an error or a wrap-around (which you must also handle).
- Logic Consistency Checks: Before finalizing a payment, the system should re-verify the total price by fetching the latest prices from the database and ensuring the math adds up to a positive value.
- API Security: Ensure that your APIs (REST, GraphQL) apply the same validation rules as your web front-end. Attackers often target APIs directly to bypass UI restrictions.
Conclusion
Negative Quantity Vulnerabilities serve as a powerful reminder that security is not just about stopping hackers from "breaking in"—it's also about ensuring your business logic cannot be subverted. By failing to validate a simple number, an organization can expose itself to significant financial and operational risk. As applications become more complex and interconnected, mapping these logic paths becomes increasingly difficult.
To proactively monitor your organization's external attack surface and catch exposures like these before attackers do, try Jsmon. By keeping a constant eye on your infrastructure and how your endpoints behave, you can stay one step ahead of logic-based exploits.



