What is Mutation XSS (mXSS)? Ways to Exploit, Examples and Impact
Discover how Mutation XSS (mXSS) works, why it bypasses sanitizers, and real-world examples. Learn to secure your web apps with Jsmon's guide.
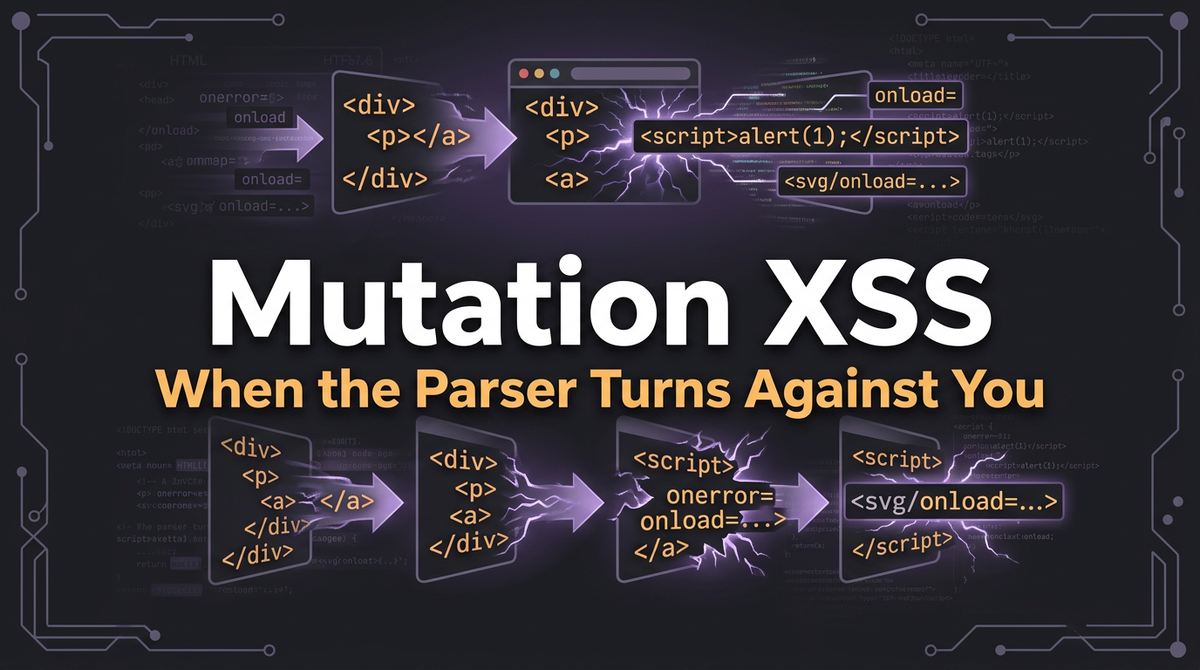
In the ever-evolving landscape of web security, Cross-Site Scripting (XSS) remains one of the most persistent threats to modern applications. While most developers are familiar with Reflected, Stored, and DOM-based XSS, a more subtle and dangerous variant has emerged: Mutation XSS (mXSS). This vulnerability exploits the way browsers interpret and "fix" malformed HTML, turning seemingly harmless code into malicious scripts. As web applications rely more heavily on client-side rendering and complex sanitization libraries, understanding mXSS is crucial for any cybersecurity professional.
What is Mutation XSS (mXSS)?
Mutation XSS (mXSS) is a specialized form of XSS that occurs when an application takes untrusted input, passes it through a sanitizer, and then assigns it to a DOM element's innerHTML property. The "mutation" happens because the browser's HTML parser attempts to correct or normalize the input before it is rendered. During this normalization process, a payload that appeared benign to the sanitizer can be transformed into executable JavaScript.
Unlike traditional XSS, where the payload is malicious from the start, an mXSS payload is often "latent." It looks like broken or weirdly formatted HTML that doesn't actually contain a script. However, once the browser's engine gets its hands on the string to build the Document Object Model (DOM), it "helps" the developer by rewriting the code into a valid, and suddenly dangerous, format.
The Role of Browser Parsing and the DOM
To understand mXSS, we must first understand how browsers handle HTML. When you set the innerHTML of an element, the browser doesn't just paste the string. It triggers a complex parsing algorithm defined by the HTML5 specification. This algorithm is designed to be "forgiving"-if you forget a closing tag or misplace an attribute, the browser tries its best to guess your intent and create a valid DOM tree.
This process involves a "round-trip" that looks like this:
- Input String: The raw, untrusted string provided by the user.
- Sanitization: A library like DOMPurify or a custom filter checks the string for dangerous tags (like
<script>). - Assignment: The "clean" string is assigned to
element.innerHTML. - Parsing/Mutation: The browser parses the string to create DOM nodes. If the string is ambiguous, the browser mutates it to make it valid.
- Serialization: If the application later reads
element.innerHTMLback out, the browser generates a string from the current DOM state. This serialized string may be different from the original input.
mXSS occurs when the mutation in Step 4 or the re-serialization in Step 5 introduces a script execution vector that was not present (or was hidden) during Step 2.
Why Sanitizers Struggle with mXSS
Sanitizers work by parsing a string into a temporary DOM, removing dangerous elements/attributes, and then turning it back into a string. The problem is that the sanitizer's parser might interpret a piece of code differently than the actual browser parser that will eventually render the content.
Modern browsers have different parsing rules for different contexts, such as inside <svg>, <math>, or <noscript> tags. A sanitizer might see a string as a harmless attribute value, but when the browser renders it, it might treat it as a closing tag that breaks out of the current context. This "context-switching" is the primary engine behind most mXSS exploits.
Technical Examples of Mutation XSS
Let's look at a few technical scenarios where mXSS manifests. These examples demonstrate how the browser's attempt to be helpful results in a security breach.
1. The <noscript> Tag Mutation
In some older browser versions or specific configurations, the <noscript> tag was a common source of mXSS. The browser's behavior changes depending on whether JavaScript is enabled. If a sanitizer parses the HTML with JS disabled, it might treat the contents of <noscript> as raw text. However, if the final page renders with JS enabled, the browser might treat it differently.
Consider this payload:
<noscript><p title="</noscript><img src=x onerror=alert(1)>"></noscript>
When a sanitizer looks at this, it sees a <p> tag inside a <noscript> tag. The title attribute contains some text. Since <noscript> is generally considered safe, the sanitizer allows it.
However, when the browser processes element.innerHTML = ..., it might close the <noscript> tag early because of the </noscript> string inside the attribute. The resulting DOM would look like this:
<noscript><p title=""></noscript>
<img src="x" onerror="alert(1)">
<p></p>
The img tag is now outside the noscript context and the onerror event fires immediately.
2. SVG and MathML Context Switching
One of the most famous mXSS techniques involves switching between standard HTML and foreign content like SVG (Scalable Vector Graphics) or MathML. These namespaces have different parsing rules. For example, in HTML, the <style> tag contains raw text, but inside an SVG, it can behave differently.
Consider a payload targeting a sanitizer that doesn't perfectly account for nested namespaces:
<svg><p><style><img src="</style><img src=x onerror=alert(1)>">
A sanitizer might think the <img> tag is safely neutralized inside a <style> block. But when the browser parses this inside an <svg> element, it might "correct" the structure by moving the <img> tag out of the style block, leading to execution.
3. Backtick and Attribute Mutations
In older versions of Internet Explorer, backticks (`) were sometimes treated as attribute delimiters. This led to a classic mXSS where a sanitizer would see an attribute as a single string, but the browser would see it as multiple attributes, one of which could be an event handler.
<img src="x" title="` onerror=alert(1) `">
If the sanitizer doesn't recognize the backtick as a special character, it leaves it alone. When the browser (with the bug) parses it, it might interpret the backtick as a quote, effectively ending the title attribute and starting a new onerror attribute.
Real-World Impact of mXSS
The impact of a successful mXSS attack is identical to traditional XSS, but it is often harder to detect and prevent. Because mXSS bypasses popular sanitization libraries, it can be used to:
- Steal Session Cookies: Attackers can access
document.cookie(ifHttpOnlyis not set) and hijack user sessions. - Perform Actions on Behalf of Users: By executing JavaScript in the user's context, an attacker can change passwords, post content, or delete data.
- Phishing and Credential Theft: An attacker can inject a fake login form into a legitimate page to steal usernames and passwords.
- Data Exfiltration: Sensitive information displayed on the page can be read by the malicious script and sent to an external server.
What makes mXSS particularly dangerous is its "zero-day" potential. When a new browser version updates its HTML parsing engine, it might inadvertently create a new mutation path that bypasses existing versions of sanitizers like Jsmon users might encounter in the wild.
How to Prevent Mutation XSS
Preventing mXSS requires a multi-layered approach that goes beyond simple blacklisting or regex-based filtering.
1. Use Modern, Actively Maintained Sanitizers
Libraries like DOMPurify are specifically designed to handle mXSS. They use a technique called "double-sanitization" or "DOM-based sanitization." They parse the input into a DOM fragment, clean it, and then serialize it. To combat mXSS, they often perform this process multiple times to ensure that the browser's own mutations don't introduce new threats. Always keep these libraries updated to the latest version.
2. Implement Trusted Types
Trusted Types is a modern browser API that helps prevent DOM-based XSS, including mXSS. It forces developers to use "Trusted Type" objects instead of raw strings when using "sink" functions like innerHTML. This ensures that all data entering the DOM has been processed by a central, secure policy.
// Example of using Trusted Types
const policy = window.trustedTypes.createPolicy('myPolicy', {
createHTML: (input) => DOMPurify.sanitize(input)
});
element.innerHTML = policy.createHTML(untrustedInput);
3. Prefer textContent Over innerHTML
If you only need to display text and don't need to render HTML tags, always use element.textContent or element.innerText. These properties do not trigger the HTML parser, making mXSS (and all other forms of XSS) impossible in that context.
4. Robust Content Security Policy (CSP)
A strong Content Security Policy acts as a final line of defense. By restricting where scripts can be loaded from and disabling the execution of inline scripts (using script-src 'self'), you can significantly mitigate the impact of an mXSS vulnerability even if a bypass is found in your sanitizer.
5. Context-Aware Encoding
When passing data between different contexts (e.g., from a JavaScript string to an HTML attribute), ensure you are using the correct encoding for that specific destination. However, remember that encoding alone is often insufficient for complex HTML structures where mXSS thrives.
Conclusion
Mutation XSS is a sophisticated vulnerability class that highlights the complexity of modern web browsers. By exploiting the very mechanisms intended to make the web more robust, attackers can bypass traditional security controls. For developers and security researchers, the key takeaway is that HTML is never just a string-it is a live, mutating structure that behaves differently across different browsers and contexts.
To effectively defend against mXSS, you must move away from manual filtering and embrace robust, DOM-aware sanitization libraries and modern browser security APIs like Trusted Types. Staying informed about browser parsing quirks and maintaining a defense-in-depth strategy is the only way to stay ahead of these "mutating" threats.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



