What is Mass Assignment? Ways to Exploit, Examples and Impact
Learn how Mass Assignment vulnerabilities allow attackers to escalate privileges. Explore technical examples and mitigation strategies for secure APIs.
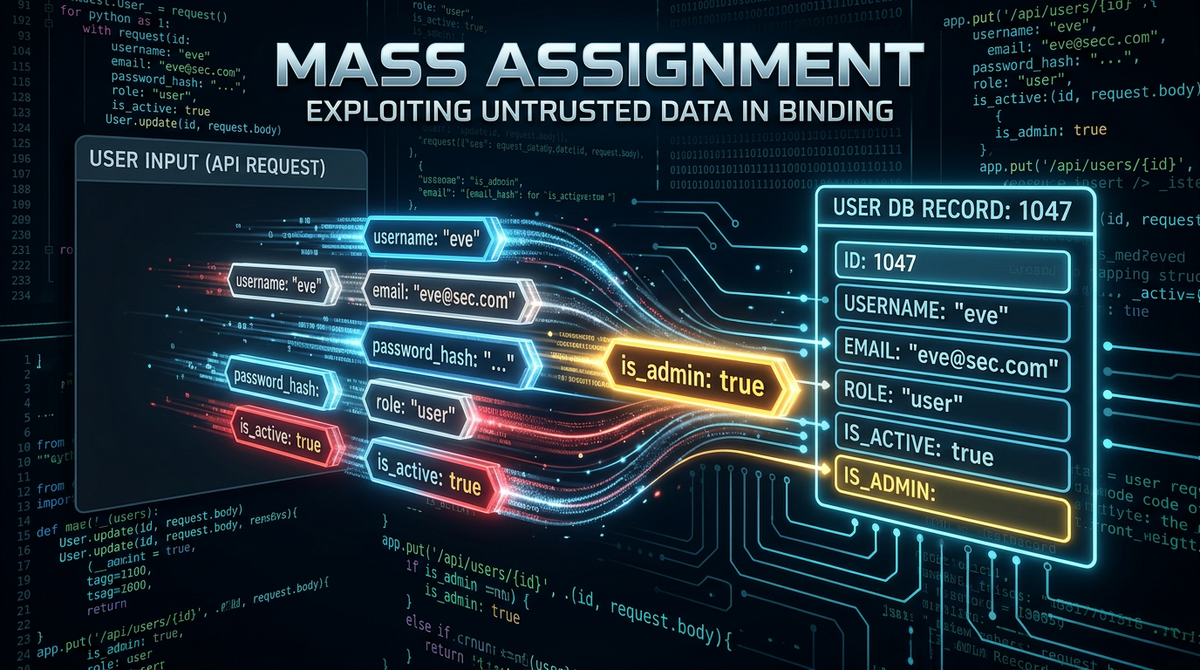
In the world of web application security, minor coding conveniences often lead to major security catastrophes. One of the most common yet overlooked vulnerabilities is Mass Assignment. This vulnerability occurs when an application takes user-provided data and binds it directly to internal software objects or database models without proper filtering. While this "auto-binding" feature saves developers time, it inadvertently gives attackers the power to modify sensitive fields they should never have access to, such as administrative privileges, account balances, or internal status flags.
What is Mass Assignment Vulnerability?
Mass Assignment is a vulnerability where an application automatically maps input parameters from an HTTP request directly into a database model or an internal object. Modern web frameworks like Ruby on Rails, Laravel, Django, and ASP.NET MVC promote this practice to speed up development. Instead of manually assigning every single field from a form to a database record, a developer might use a single line of code to update an entire object.
For example, in a typical user profile update, a developer might write code that looks like this in a conceptual framework:
// Vulnerable Code Example
app.post('/update-profile', (req, res) => {
const user = User.findById(req.session.userId);
user.update(req.body); // This line is the root of the problem
user.save();
res.send('Profile updated!');
});
In this scenario, the req.body contains whatever data the user sent in their POST request. If the user sends {"bio": "I love security"}, the code works as intended. However, if an attacker sends {"bio": "I love security", "is_admin": true}, and the User model has an is_admin field, the application will blindly update that field in the database, granting the attacker administrative access. This lack of an "allow-list" for input parameters is what defines a Mass Assignment vulnerability.
How Mass Assignment Works: The Technical Root Cause
To understand why this happens, we must look at Object-Relational Mapping (ORM) and Data Binding. ORMs are tools that allow developers to interact with a database using the programming language's native objects rather than writing raw SQL. To make development faster, these ORMs often include features that allow for "bulk updates."
When a request hits the server, the framework parses the incoming data (usually JSON or URL-encoded form data) and creates a dictionary or map. The mass assignment feature then iterates through this map and matches the keys to the attributes of the database model. If the key matches an attribute name, the value is assigned.
This process is inherently dangerous because it assumes that the client (the user's browser or API client) is trustworthy. In security, we must always assume that the client is malicious. By failing to distinguish between "user-controllable" fields and "protected" internal fields, the application exposes its internal data structure to the outside world.
How to Identify Mass Assignment Vulnerabilities
Finding Mass Assignment vulnerabilities requires a mix of reconnaissance and creative guessing. Since these vulnerabilities often exist on API endpoints, the first step is to map out the application's data models.
1. Analyzing API Responses
Start by looking at the JSON returned by the server during a GET request. If you fetch your own profile and see fields like "role": "user", "is_verified": false, or "account_level": 1, these are prime targets. Even if these fields aren't visible in the UI, their presence in the API response suggests they exist in the underlying model.
2. Parameter Guessing (Fuzzing)
Once you identify a potential field, try to include it in a PUT or POST request. If the application has a profile update page, intercept the request and add the hidden field. For instance, if the original request is:
POST /api/v1/user/update
Content-Type: application/json
{
"first_name": "John",
"last_name": "Doe"
}
You might try to modify it to:
POST /api/v1/user/update
Content-Type: application/json
{
"first_name": "John",
"last_name": "Doe",
"role": "admin",
"is_admin": true,
"permissions": ["*"],
"balance": 99999
}
3. Reviewing Documentation
Sometimes, API documentation (like Swagger or Redoc) lists all available fields for a model, even those that aren't meant to be updated by the user. If the documentation shows a created_at or owner_id field, try to overwrite them. Successfully changing a created_at timestamp is a strong indicator that the endpoint is vulnerable to mass assignment.
Exploitation Scenarios and Real-World Impact
The impact of Mass Assignment ranges from minor data corruption to full system compromise. Here are three common exploitation scenarios:
Scenario A: Privilege Escalation
This is the most common and dangerous outcome. An attacker changes their role from user to admin or super_user. Once they have administrative rights, they can access sensitive data, delete other users, or change system configurations. This is often as simple as adding "admin": true to a registration or profile update request.
Scenario B: Bypassing Business Logic
Imagine an e-commerce application where you can update your "cart." If the application uses mass assignment on the Order model, an attacker might try to change the status of an order from "pending_payment" to "paid" or "shipped" without actually providing a credit card. Alternatively, they might try to change the total_price of the items in their cart to $0.01 before checking out.
Scenario C: Account Takeover via Email Modification
In some poorly designed systems, changing a user's email address triggers a password reset or bypasses MFA. If an attacker can use mass assignment to change their email or secondary_email field to one they control, they might be able to initiate a password reset and take over the account. More critically, if they can change the owner_id of a resource, they can effectively steal ownership of data belonging to other users.
Real-World Example: The GitHub Incident (2012)
One of the most famous examples of Mass Assignment occurred in 2012 on GitHub. A researcher named Egor Homakov discovered that GitHub's public key upload feature was vulnerable. By adding a specific parameter to the request, he was able to associate his own SSH key with the "rails" organization (the developers of the Ruby on Rails framework itself).
Because the Rails framework encouraged mass assignment by default at the time, Homakov was able to modify the user_id or organization ownership fields of the SSH key object. This allowed him to gain commit access to the Rails repository. This incident was a wake-up call for the industry and led to significant changes in how modern frameworks handle mass assignment by default.
How to Prevent Mass Assignment Attacks
Securing your application against mass assignment requires a "deny-by-default" mindset. You should never allow the framework to automatically bind all incoming parameters. Here are the best practices for prevention:
1. Use Allow-listing (Strong Parameters)
Most modern frameworks now provide built-in tools to handle this. In Ruby on Rails, this is known as "Strong Parameters." Instead of passing the entire params object, you explicitly define which fields are allowed to be updated.
# Secure Rails Example
def update
@user = User.find(params[:id])
# Only permit the 'bio' and 'name' fields
permitted_params = params.require(:user).permit(:bio, :name)
@user.update(permitted_params)
end
2. Use Data Transfer Objects (DTOs)
In languages like Java (Spring) or C# (ASP.NET), it is best practice to use DTOs. A DTO is a simple class that contains only the fields that are intended to be received from the user. You map the incoming request to the DTO, and then manually copy the values from the DTO to your actual Database Entity. This creates a physical layer of separation between the user input and your database model.
3. Framework-Specific Protections
- Laravel: Use the
$fillableor$guardedproperties in your Eloquent models. The$fillablearray defines exactly which attributes can be mass-assigned. - Django: Use Django Forms or ModelForms, which require you to explicitly list the fields included in the form. Avoid using
request.POSTdirectly to update model instances. - Node.js (Sequelize/Mongoose): When calling
.create()or.update(), pass an explicit array of fields to thefieldsoption to restrict which columns are affected.
4. Read-Only Fields
At the database level or the ORM level, mark sensitive fields as read-only. For example, a created_at timestamp or a user_uuid should never be modifiable after the initial creation, regardless of what the application code attempts to do.
Conclusion
Mass Assignment is a classic example of how developer convenience can undermine security. While it is tempting to use auto-binding to write less code, the risks of privilege escalation and data tampering are too high to ignore. By implementing strict allow-listing, using DTOs, and performing regular security audits of your API endpoints, you can effectively neutralize this threat. Security is not just about stopping complex exploits; it starts with controlling how data flows into your system's most basic building blocks.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



