What is Jailbreak Detection Bypass? Ways to Exploit, Examples and Impact
Discover how jailbreak detection bypass works. Explore technical exploit methods like Frida scripts and binary patching to secure your mobile apps.
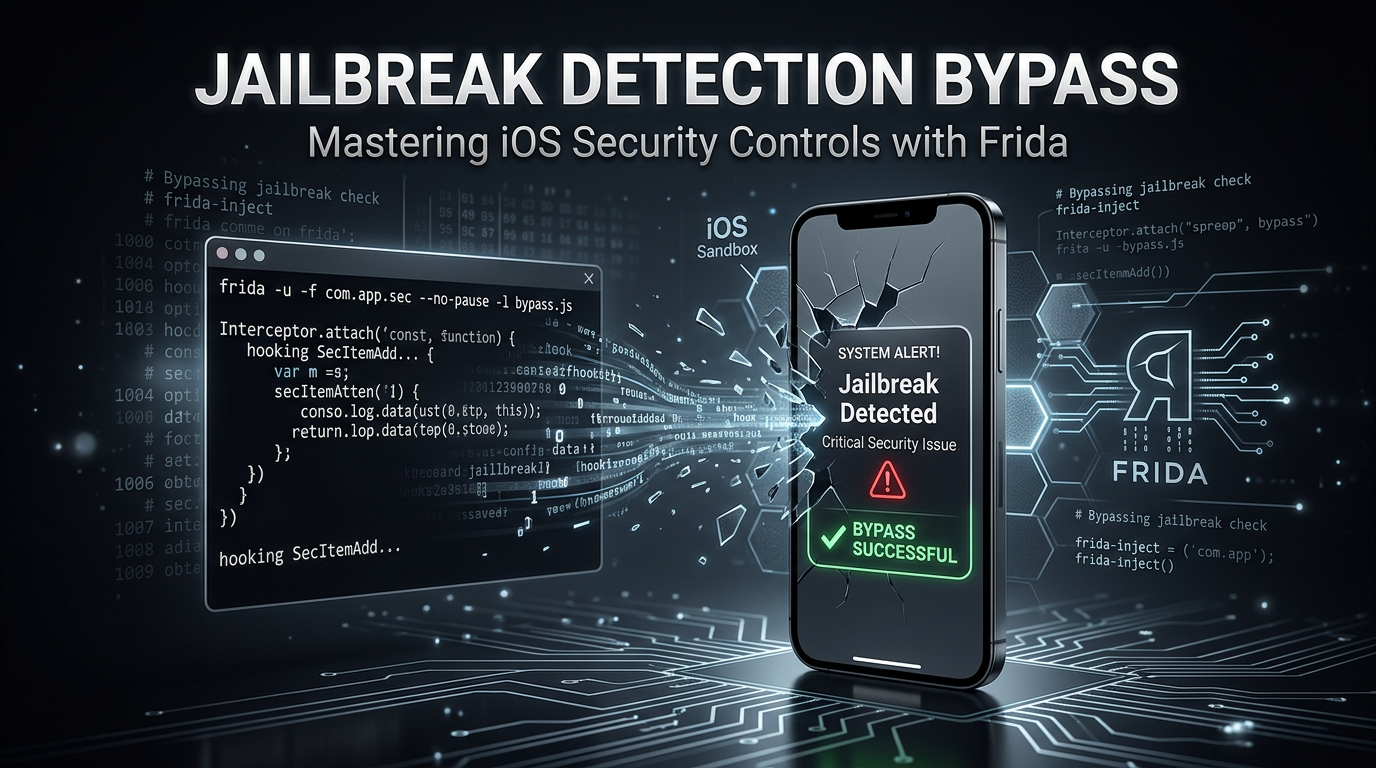
In the ever-evolving world of mobile security, the battle between app developers and security researchers often centers on the integrity of the operating system. For iOS, this battleground is defined by jailbreaking—the process of removing software restrictions imposed by Apple. To protect sensitive data, developers implement jailbreak detection mechanisms. However, these checks are rarely infallible. This guide explores what jailbreak detection bypass is, the technical methods used to circumvent these security controls, and the real-world implications for mobile application security.
Understanding Jailbreak Detection
Before diving into the bypass techniques, we must understand what we are trying to circumvent. Jailbreak detection is a set of security checks embedded within a mobile application to determine if the device's operating system has been modified. On iOS, the system is designed to run in a "sandbox," which limits an application's access to the file system and other apps. Jailbreaking breaks this sandbox, granting root access and allowing the installation of unsigned code.
From a developer's perspective, a jailbroken device is an untrusted environment. If a banking app or a corporate email client runs on a jailbroken phone, an attacker could potentially hook into the app’s process, steal credentials, or intercept encrypted traffic. To prevent this, developers use various heuristics to "fingerprint" a jailbroken state.
Common Jailbreak Detection Methods
Most detection logic relies on identifying artifacts that are only present on a modified system. These include:
- File Existence Checks: Searching for specific files or directories created during the jailbreak process. Examples include
/Applications/Cydia.app,/usr/sbin/sshd, and/bin/bash. - Directory Permissions: Attempting to write to a system directory (like
/private) that is normally read-only for sandboxed applications. - Symbolic Link Checks: Verifying if standard system directories have been replaced by symbolic links, a common tactic used by jailbreaks to move large system files to the data partition.
- System API Checks: Using C functions like
fork()or checking for the presence of dynamic libraries (dylibs) associated with hooking frameworks like Cydia Substrate or Substitute.
What is Jailbreak Detection Bypass?
Jailbreak detection bypass is the process of neutralizing or tricking these detection mechanisms so that an application continues to run on a modified device without restrictions. This is a classic example of a "Cat and Mouse" game. Developers implement a check; researchers find a way to hide the jailbreak; developers implement more sophisticated checks; and the cycle repeats.
For security professionals and penetration testers, bypassing these checks is often the first step in a mobile app assessment. Without a bypass, the app may crash or refuse to open, preventing any further analysis of its internal logic, API calls, or local storage security.
Ways to Exploit and Bypass Detection
There are several technical approaches to bypassing jailbreak detection, ranging from automated tweaks to manual runtime manipulation.
1. Automated Bypass Tweaks
For many users, the easiest way to bypass detection is through pre-built tweaks available on platforms like Sileo or Zebra. Tools like Liberty Lite, Shadow, and A-Bypass work by hooking into the system's file-checking APIs. When an application asks the system, "Does /Applications/Cydia.app exist?", the tweak intercepts the call and returns a "No," even if the file is present.
2. Runtime Manipulation with Frida
Jsmon users and security researchers often prefer more surgical tools like Frida. Frida is a dynamic instrumentation toolkit that allows you to inject scripts into a running process. Instead of modifying the app's binary, you modify its behavior in memory.
Consider a simple Objective-C method that checks for a jailbreak:
-(BOOL)isDeviceJailbroken {
if ([[NSFileManager defaultManager] fileExistsAtPath:@"/Applications/Cydia.app"]) {
return YES;
}
return NO;
}
An attacker can use a Frida script to "hook" this method and force it to always return false (0). Here is an example of what that script looks like:
if (ObjC.available) {
try {
var className = "JailbreakCheck";
var funcName = "- isDeviceJailbroken";
var hook = ObjC.classes[className][funcName];
Interceptor.attach(hook.implementation, {
onLeave: function(retval) {
console.log("[+] Original return value: " + retval);
retval.replace(0x0); // Force return value to false
console.log("[+] New return value: " + retval);
}
});
} catch (err) {
console.log("[-] Error: " + err.message);
}
} else {
console.log("Objective-C Runtime is not available!");
}
By running this script, the application is effectively blinded to the existence of the jailbreak because the logic gate that triggers the "Exit" or "Warning" state has been overridden.
3. Objective-C Method Swizzling
Method Swizzling is a technique unique to the Objective-C runtime where the implementation of an existing selector is swapped with another at runtime. This is similar to Frida but is often implemented via a custom dynamic library (dylib) injected into the app.
By using method_exchangeImplementations, a developer of a bypass tweak can swap a legitimate security check with a dummy function that always reports a secure state.
4. Patching the Binary
If runtime manipulation is not an option (due to anti-tampering protections), an attacker might resort to static analysis and binary patching. Using tools like Hopper Disassembler or IDA Pro, a researcher can locate the assembly instructions responsible for the jailbreak check.
Typically, this involves finding a conditional jump instruction (like CBZ or CBNZ in ARM64) and changing it to a NOP (No Operation) or reversing the logic so the jump always occurs. Once patched, the binary is resigned and reinstalled on the device.
Real-World Examples and Scenarios
Bypassing Banking App Security
Banking applications are notorious for aggressive jailbreak detection. They do this to prevent "Overlay Attacks" where a malicious app on a jailbroken device draws a fake login screen over the real banking app. A successful bypass allows a researcher to use tools like Burp Suite to intercept the app's HTTPS traffic. By bypassing the jailbreak check, the researcher can then bypass SSL Pinning, revealing the underlying API structure and potentially finding vulnerabilities like Insecure Direct Object References (IDOR).
Mobile Game Cheating
In the gaming industry, jailbreak detection is used as an anti-cheat measure. Many games check for jailbreaks to prevent users from using memory editors (like iGameGuardian) to modify currency values or player stats. Bypassing these checks is the first step for developers of game "mods."
The Technical Impact of Bypasses
The impact of a successful jailbreak detection bypass is significant because it invalidates the "Trusted Execution Environment" assumption.
- Data Theft: Once an app is running in a compromised state, an attacker can dump the contents of the Keychain, which might contain sensitive tokens or passwords.
- Intellectual Property Theft: By bypassing checks, attackers can more easily decompile the app and steal proprietary algorithms or hardcoded secrets.
- API Abuse: When detection is bypassed, the app's traffic is exposed. Attackers can analyze the backend communication and craft malicious requests that the server might not be prepared to handle.
How to Prevent and Mitigate Bypasses
While no client-side check is 100% secure, developers can make the bypass process significantly harder by following these best practices:
1. Layered Defense
Do not rely on a single check. Use a combination of file checks, C-based system calls, and tool-specific checks (e.g., looking for Frida's default port 27042). Scatter these checks throughout the application's lifecycle rather than running them all at startup.
2. Use Inline C Functions
Objective-C methods are easy to hook because of the dynamic nature of the runtime. Using inline C functions for security checks makes it much harder for tools like Frida to find and intercept the logic, as the code is compiled directly into the calling function rather than being a standalone symbol.
3. Obfuscation
Use code obfuscation to hide the strings associated with jailbreak detection. Instead of searching for the string "/Applications/Cydia.app", store it in an encrypted format and decrypt it only at the moment of the check. This prevents attackers from finding the detection logic simply by searching for keywords in the binary.
4. Server-Side Validation
Where possible, move the trust anchor to the server. Use DeviceCheck or App Attest (on iOS) to let Apple’s servers verify that the app is legitimate and running on an uncompromised device. This is much harder to bypass because the verification happens outside the local device's memory.
Conclusion
Jailbreak detection bypass is a fundamental technique in the mobile security landscape. For developers, it represents a risk that must be managed through layered defenses and obfuscation. For security professionals, it is a necessary skill for uncovering deeper vulnerabilities within an application. Understanding the mechanics of how these bypasses work—from simple file-system tweaks to complex Frida instrumentation—is essential for anyone involved in building or securing mobile software.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



