What is Insecure Direct Object References (IDOR)? Ways to Exploit, Examples and Impact
Learn what Insecure Direct Object Reference (IDOR) is, how to exploit it with technical examples, and best practices for prevention in our deep-dive guide.
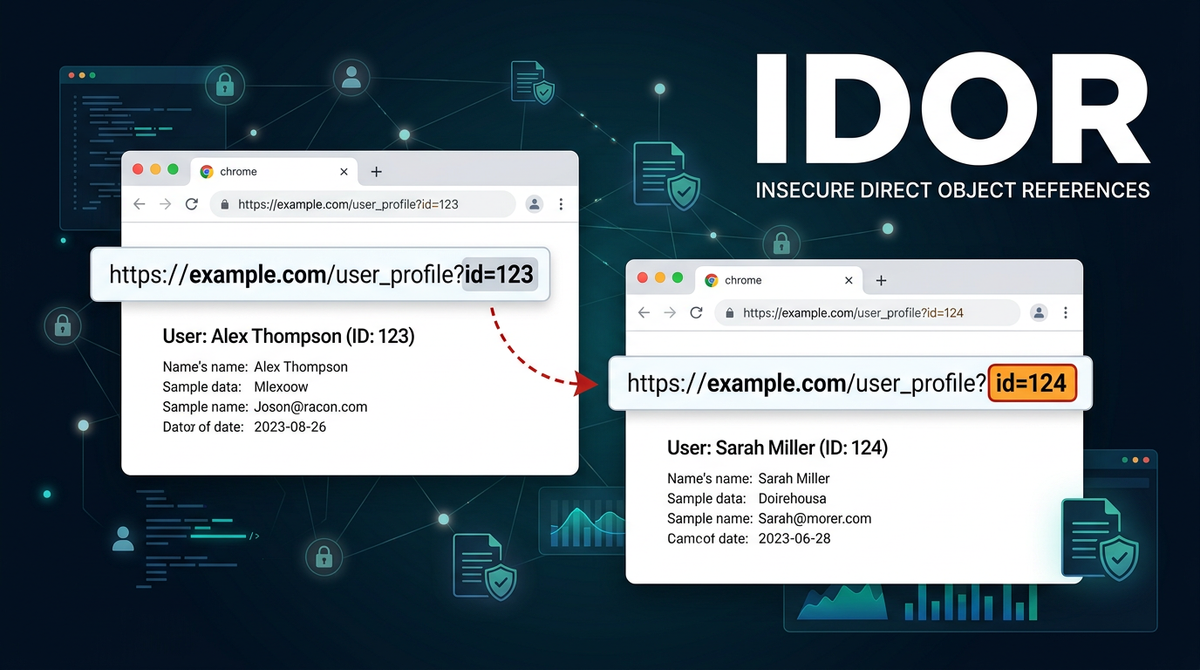
Imagine logging into a web application to view your profile settings. You notice the URL ends with user_id=1234. Out of curiosity, you change that number to 1235 and hit enter. Suddenly, you are looking at the private account details of a complete stranger. This scenario is the essence of an Insecure Direct Object Reference (IDOR), a type of access control vulnerability that remains one of the most common and damaging threats in modern web security. In this guide, we will explore the technical mechanics of IDOR, provide practical exploitation examples, and discuss how developers can build robust defenses against it.
What is an Insecure Direct Object Reference (IDOR)?
Insecure Direct Object Reference, or IDOR, occurs when an application provides direct access to objects based on user-supplied input. In technical terms, it is a subcategory of broken access control. When an application uses an identifier for an internal object (like a database key, a filename, or a server path) as a parameter in a request, and fails to validate whether the requesting user has the appropriate permissions to access that object, an IDOR vulnerability exists.
Traditionally, IDOR was listed as its own category in the OWASP Top 10 (A4:2013). In more recent iterations, it has been folded into the broader "Broken Access Control" category, which currently holds the number one spot on the list. This highlights just how critical it is for developers and security professionals to understand how these flaws manifest in the wild. While the concept is simple—requesting a resource you shouldn't see—the implementation of IDOR can be subtle, hiding within APIs, mobile backends, and complex cloud architectures.
The Core Mechanism: How IDOR Vulnerabilities Occur
To understand IDOR, you must understand how web applications handle data. Most applications rely on a database where every record has a Unique Identifier (UID), often a primary key. When you want to view a specific record, the application needs to know which one to fetch.
A vulnerable application logic usually follows this flow:
- The user authenticates (logs in).
- The user requests a resource (e.g.,
GET /api/view_invoice?id=500). - The server receives the request and extracts the ID
500. - The server executes a query:
SELECT * FROM invoices WHERE id = 500;. - The server sends the data back to the user.
The flaw here is that the server trusts the user's input implicitly. It checks if the user is logged in, but it does not check if the logged-in user actually owns invoice 500. If an attacker changes the ID to 501, the server will execute the query for that ID and return the data, regardless of ownership. This direct mapping from the user input to the database object without an intermediate authorization layer is what makes the reference "insecure."
Common Attack Vectors for IDOR
IDOR vulnerabilities are not limited to URL parameters. They can appear anywhere an application accepts input to identify a resource. Here are the most common places to look for them:
1. URL Parameters and Query Strings
This is the most visible form of IDOR. As seen in the previous example, identifiers are passed directly in the URL.
GET /edit_profile.php?user_id=8821 HTTP/1.1
Host: example.com
An attacker simply increments or decrements the user_id to access other accounts.
2. POST Body Parameters
Modern web applications, especially those using REST or GraphQL APIs, often pass identifiers in the body of a POST, PUT, or PATCH request.
POST /api/update_address HTTP/1.1
Content-Type: application/json
{
"account_id": "9920",
"new_address": "123 Hacker Way"
}
By changing the account_id in the JSON payload, an attacker might update the address of a different user.
3. HTTP Headers
Sometimes, applications use custom headers or cookies to track session-specific objects. If a header like X-User-ID or X-Organization-ID is used to determine which data to display, and the server doesn't verify this against the session token, it is a prime target for IDOR.
4. File System Paths
IDOR can also lead to Local File Inclusion (LFI) or unauthorized file downloads. If an application allows you to download a receipt using a filename parameter:
GET /download?file=receipt_441.pdf HTTP/1.1
An attacker might try file=../../etc/passwd or simply guess other filenames like receipt_442.pdf to steal data from other users.
Technical Examples and Payloads
Let’s look at a few practical scenarios to see how an attacker might exploit these flaws. Understanding these examples is key for security researchers using Jsmon to map out their infrastructure and find hidden endpoints.
Example 1: Horizontal IDOR (Accessing Peer Data)
Horizontal IDOR occurs when an attacker accesses data belonging to another user with the same level of privileges.
Vulnerable Code (PHP):
$invoice_id = $_GET['id'];
// The query only checks the ID, not the owner!
$query = "SELECT * FROM invoices WHERE id = '$invoice_id'";
$result = $db->query($query);
$data = $result->fetch_assoc();
echo json_encode($data);
Exploitation:
The attacker views their own invoice at /view_invoice.php?id=100. They then use a tool like Burp Suite Intruder to fuzz the id parameter from 1 to 1000. They find that they can read every invoice in the database, potentially exposing PII (Personally Identifiable Information) and financial records.
Example 2: Vertical IDOR (Privilege Escalation)
Vertical IDOR occurs when a user accesses a resource that should only be available to a higher-privileged user, such as an administrator.
Request:
GET /admin/user_details?id=1 HTTP/1.1
Cookie: session=regular_user_session_token
If the server only checks if the user is logged in but fails to check if the user has the ROLE_ADMIN permission for that specific endpoint, the regular user can view administrative details.
Example 3: IDOR in API Endpoints
APIs are often more susceptible to IDOR because they are designed for programmatic access and sometimes lack the robust middleware found in traditional web frameworks.
Request:
DELETE /api/v1/posts/554 HTTP/1.1
Authorization: Bearer <token>
If the API logic for the DELETE method doesn't verify that the user associated with the Bearer token is the author of post 554, any authenticated user could delete any post on the platform by simply knowing the post ID.
Advanced IDOR Scenarios: UUIDs and Beyond
A common misconception is that using Universally Unique Identifiers (UUIDs) like 550e8400-e29b-41d4-a716-446655440000 instead of sequential integers (1, 2, 3...) prevents IDOR. While UUIDs make it impossible for an attacker to "guess" or iterate through IDs, they do not fix the underlying vulnerability.
If an attacker can discover a UUID through other means—such as a public profile page, a leaked log, or a previous API response—they can still use that UUID to exploit the insecure reference. Security through obscurity is not a substitute for proper authorization. Furthermore, in some cases, UUIDs are generated predictably based on time or MAC addresses, allowing sophisticated attackers to reverse-engineer them.
The Real-World Impact of IDOR
The impact of an IDOR vulnerability can range from minor information disclosure to catastrophic data breaches. Some of the most common consequences include:
- Data Exfiltration: Attackers can scrape entire databases of user information, including emails, addresses, and credit card fragments.
- Account Takeover: If an IDOR exists on a password reset or email update functionality, an attacker can change the credentials of any user account.
- Data Manipulation: Attackers can modify or delete records, leading to data loss or integrity issues for the business.
- Reputational Damage: Large-scale data leaks resulting from simple IDOR flaws often lead to loss of customer trust and heavy legal fines under regulations like GDPR.
How to Prevent IDOR Vulnerabilities
Preventing IDOR requires a defense-in-depth approach. You cannot rely on a single "fix." Instead, you must implement authorization checks at every level of your application.
1. Implement Strict Access Control Checks
Every time a user requests an object, the server must verify that the user has the right to access that specific instance. This is often done using an Access Control List (ACL) or Role-Based Access Control (RBAC).
Secure Code Example (Node.js/Express):
app.get('/api/invoice/:id', async (req, res) => {
const invoiceId = req.params.id;
const userId = req.user.id; // From authenticated session
const invoice = await db.Invoices.findOne({ where: { id: invoiceId } });
if (!invoice) {
return res.status(404).send('Invoice not found');
}
// CRITICAL: Check ownership
if (invoice.ownerId !== userId) {
return res.status(403).send('Unauthorized access');
}
res.json(invoice);
});
2. Use Indirect Object References
Instead of exposing the database ID directly, use a temporary, session-specific mapping. For example, instead of id=500, the UI might show id=A. The server maintains a map in the user's session: A => 500. When the user requests A, the server translates it. Since the map is unique to that user's session, an attacker cannot guess the mapping for another user.
3. Avoid Predictable Identifiers
While UUIDs aren't a complete fix, they are still better than sequential integers. They prevent basic "ID walking" attacks and make mass scraping significantly harder. Always use version 4 (random) UUIDs.
4. Validate All User Input
Never trust data coming from the client. Treat every parameter, header, and cookie as potentially malicious. Implement centralized authorization middleware that runs before your business logic to ensure consistency across the application.
Conclusion
Insecure Direct Object References are a deceptive vulnerability. They are technically simple to understand but remarkably easy to overlook during the development process. As applications grow in complexity and move toward microservices and sprawling API ecosystems, the surface area for IDOR only increases. By moving away from direct object mapping and enforcing rigorous, ownership-based authorization checks, developers can effectively neutralize this threat.
For security teams, identifying these flaws requires a deep understanding of the application's infrastructure and how data flows between endpoints. To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



