What is HTTP/2 Request Smuggling? Ways to Exploit, Examples and Impact
As the web evolved, the limitations of the aging HTTP/1.1 protocol became apparent. To address latency and performance issues, HTTP/2 was introduced, bringing features like binary framing, multiplexing, and header compression. However, with new features come new security challenges. HTTP/2 Request Smuggling has emerged as a critical vulnerability that allows attackers to interfere with the way a website processes sequences of HTTP requests received from one or more users. In this guide, we will dive deep into the technical mechanics of this vulnerability, how it differs from its HTTP/1.1 predecessor, and how you can identify and mitigate it in modern environments.
Understanding the Basics: From HTTP/1.1 to HTTP/2
To understand HTTP/2 Request Smuggling, we first need to understand the fundamental shift in how data is transmitted. HTTP/1.1 is a text-based protocol. Requests are sent as plain text blocks, and the boundaries between requests are defined by the Content-Length header or the Transfer-Encoding: chunked mechanism.
In contrast, HTTP/2 is a binary protocol. It breaks communication down into smaller units called "frames," which are then interleaved within "streams." This allows for multiplexing—sending multiple requests and responses over a single TCP connection simultaneously without waiting for one to finish before starting the next. While this is great for performance, it creates a significant complexity gap when an infrastructure uses a mix of both protocols.
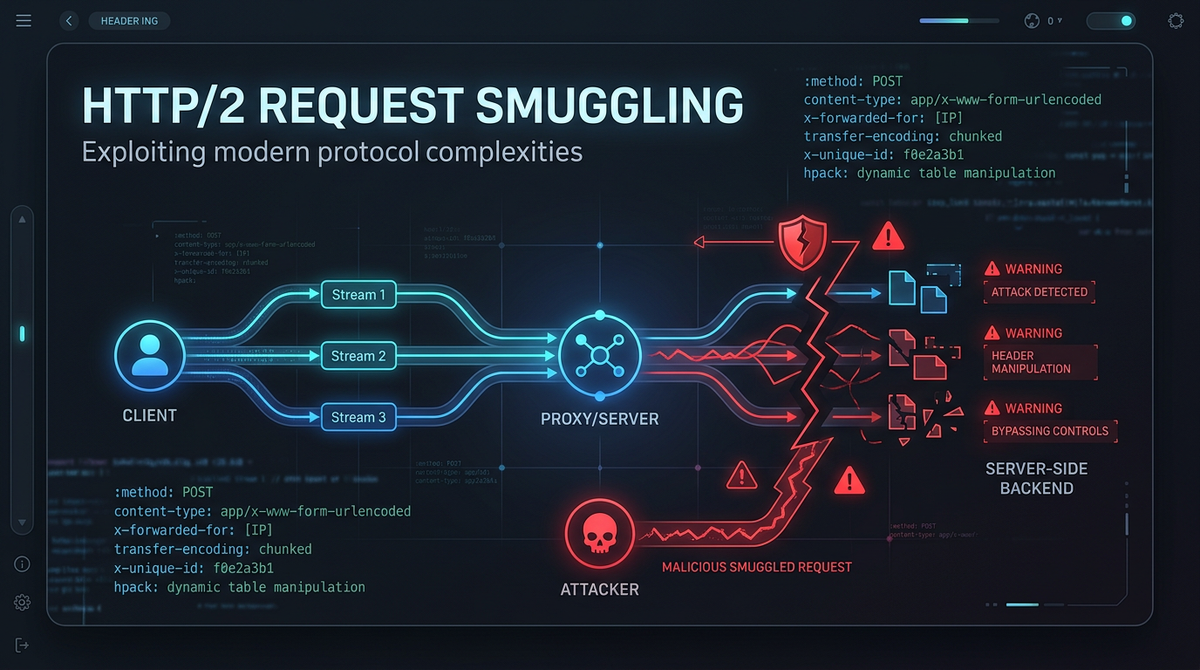
Most modern web architectures involve a front-end server (like a load balancer, reverse proxy, or CDN) that speaks HTTP/2 to the client but "downgrades" the communication to HTTP/1.1 when talking to the back-end application server. This translation process is where the primary risk of HTTP/2 Request Smuggling resides.
What is HTTP/2 Request Smuggling?
HTTP/2 Request Smuggling occurs when an attacker exploits inconsistencies in how the front-end (HTTP/2) and the back-end (HTTP/1.1) interpret the boundaries of a request. Because the front-end sees the request as a series of binary frames and the back-end sees it as a text stream, an attacker can craft a request that looks like one request to the front-end but is interpreted as two (or more) requests by the back-end.
The "smuggled" portion of the request hangs out in the back-end server's connection buffer, waiting to be prepended to the next legitimate request that arrives. This allows an attacker to bypass security controls, hijack user sessions, or poison web caches.
How the Exploit Works: The Downgrading Vulnerability
The most common scenario involves a front-end proxy that supports HTTP/2 and a back-end server that only supports HTTP/1.1. When the front-end receives an HTTP/2 request, it must rewrite it into an HTTP/1.1 format to forward it.
The Role of Content-Length and Transfer-Encoding
In HTTP/1.1, there are two main ways to specify where a request ends:
- Content-Length (CL): Specifies the size of the message body in bytes.
- Transfer-Encoding (TE): Specifies that the message body uses chunked encoding.
If a request contains both, the Transfer-Encoding header usually takes precedence. Request smuggling happens when the front-end and back-end disagree on which header to follow. In the context of HTTP/2, the front-end uses its internal frame lengths to determine request boundaries, but when it converts the request to HTTP/1.1 for the back-end, it might inject a Content-Length or Transfer-Encoding header that contradicts the actual data sent.
Common HTTP/2 Smuggling Vectors
There are several ways to achieve request smuggling when HTTP/2 is involved. Let's look at the most prominent technical methods.
1. H2.CL (HTTP/2 over Content-Length)
In this scenario, the attacker sends an HTTP/2 request that includes a content-length header. According to the HTTP/2 specification, the content-length header is not required for determining the end of a request because the protocol uses the END_STREAM flag. However, many front-end servers permit the header to pass through to the back-end.
If the front-end doesn't validate that the content-length matches the actual size of the HTTP/2 data frames, the back-end (expecting HTTP/1.1) will use that header to decide where the request ends.
Example Payload:
:method: POST
:path: /
:authority: example.com
content-length: 5
0
GET /admin HTTP/1.1
Host: example.com
Foo: x
In this example, the front-end sees one HTTP/2 request. It forwards it to the back-end as HTTP/1.1. The back-end sees content-length: 5, reads only the first 5 bytes (the 0 and some newlines), and considers the first request finished. The remaining part (GET /admin...) stays in the buffer and is treated as the start of the next request that comes into the server.
2. H2.TE (HTTP/2 over Transfer-Encoding)
Similar to H2.CL, this involves the transfer-encoding header. The attacker sends an HTTP/2 request with transfer-encoding: chunked.
Example Payload:
:method: POST
:path: /
:authority: example.com
transfer-encoding: chunked
0
GET /admin HTTP/1.1
Host: example.com
Foo: x
If the front-end ignores the transfer-encoding header (because it relies on HTTP/2 framing) but the back-end honors it, the back-end will stop processing the first request at the 0 (the end-of-chunk marker). The smuggled GET /admin request will then be processed as if it were sent by the next innocent user.
3. CRLF Injection in HTTP/2 Headers
HTTP/2 headers are binary, which means they can technically contain characters that are illegal in HTTP/1.1 headers, such as Carriage Return (\r) and Line Feed (\n). If a front-end server doesn't sanitize these characters before downgrading the request to HTTP/1.1, an attacker can inject entirely new headers or even a new request body.
Example Payload (Logical Representation):
:method: POST
:path: /
:authority: example.com
foo: bar\r\n
content-length: 50\r\n
\r\n
smuggled=data
When the front-end converts this to HTTP/1.1, the \r\n characters are interpreted as newlines, effectively creating a new content-length header that the back-end will follow, leading to a smuggling condition.
Real-World Impact of Request Smuggling
The consequences of a successful HTTP/2 Request Smuggling attack can be devastating for an organization. Because the attacker is essentially "splicing" their request into another user's connection, the following impacts are common:
Session Hijacking and Account Takeover
If an attacker smuggles a request that starts with POST /update-email HTTP/1.1, and a legitimate user's request (containing their session cookies) is appended to it, the back-end might process the email update using the victim's session. The attacker can then reset the password and take over the account.
Bypassing Front-End Security Controls
Many organizations use a front-end proxy (WAF) to block access to sensitive paths like /admin or /internal. However, the WAF only sees the outer HTTP/2 request. It doesn't see the smuggled HTTP/1.1 request hidden inside the body. This allows attackers to reach restricted endpoints that should be inaccessible from the public internet.
Web Cache Poisoning
If the environment uses a web cache, an attacker can smuggle a request that causes the back-end to return a response meant for the attacker, but the cache associates it with a legitimate URL. Every user who visits that URL afterwards will receive the attacker's cached response, which could contain malicious JavaScript (XSS).
How to Detect HTTP/2 Request Smuggling
Detecting this vulnerability manually is difficult because it requires precise timing and specific protocol handling. However, there are several approaches:
- Differential Timing Analysis: Send a request that, if smuggled, will cause the back-end to wait for more data (causing a timeout). If the response is delayed only when the smuggled payload is present, a vulnerability likely exists.
- Protocol Fuzzing: Use tools to send malformed HTTP/2 headers containing
\r\nor duplicatecontent-lengthheaders to see how the server responds. - Infrastructure Auditing: Check if your load balancers are performing HTTP/2 to HTTP/1.1 downgrading. If they are, they are potentially at risk.
To proactively monitor your organization's external attack surface and catch exposures like misconfigured proxies or protocol downgrading before attackers do, try Jsmon.
Mitigation and Prevention Strategies
Securing your infrastructure against HTTP/2 Request Smuggling requires a defense-in-depth approach. Here are the most effective strategies:
1. Use HTTP/2 End-to-End
The most effective way to eliminate the vulnerability is to avoid protocol downgrading entirely. If both your front-end and back-end servers communicate via HTTP/2, the ambiguity of the HTTP/1.1 translation layer disappears. This ensures that binary framing is preserved throughout the request lifecycle.
2. Strict Header Validation
Ensure that your front-end server strictly validates HTTP/2 headers. It should reject any requests containing \r, \n, or : in header names (other than pseudo-headers). Furthermore, it should reject requests that contain both a content-length header and are sent via HTTP/2, or at least ensure the header matches the frame length.
3. Disable Request Multiplexing on the Back-end
While this may impact performance, forcing the back-end to use a fresh TCP connection for every request received from the proxy prevents an attacker from "poisoning" a shared connection. This effectively isolates requests from one another.
4. Use Modern Web Servers
Ensure that your Nginx, Apache, or HAProxy versions are up to date. Many early implementations of HTTP/2 support had bugs that made smuggling easier. Modern versions have implemented stricter parsing rules to mitigate these risks.
Conclusion
HTTP/2 Request Smuggling is a sophisticated attack that highlights the dangers of protocol complexity and architectural translation. As more organizations adopt HTTP/2 for its performance benefits, the surface area for these attacks grows. By understanding the mechanics of H2.CL and H2.TE vectors and ensuring that your front-end and back-end servers are tightly synchronized, you can protect your users and your data from this invisible threat.
Continuous monitoring of your infrastructure is essential in a landscape where configurations change daily. To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



