What is Hash Collision DoS? Ways to Exploit, Examples and Impact
Learn how Hash Collision DoS attacks work, their technical impact on web applications, and how to prevent algorithmic complexity vulnerabilities.
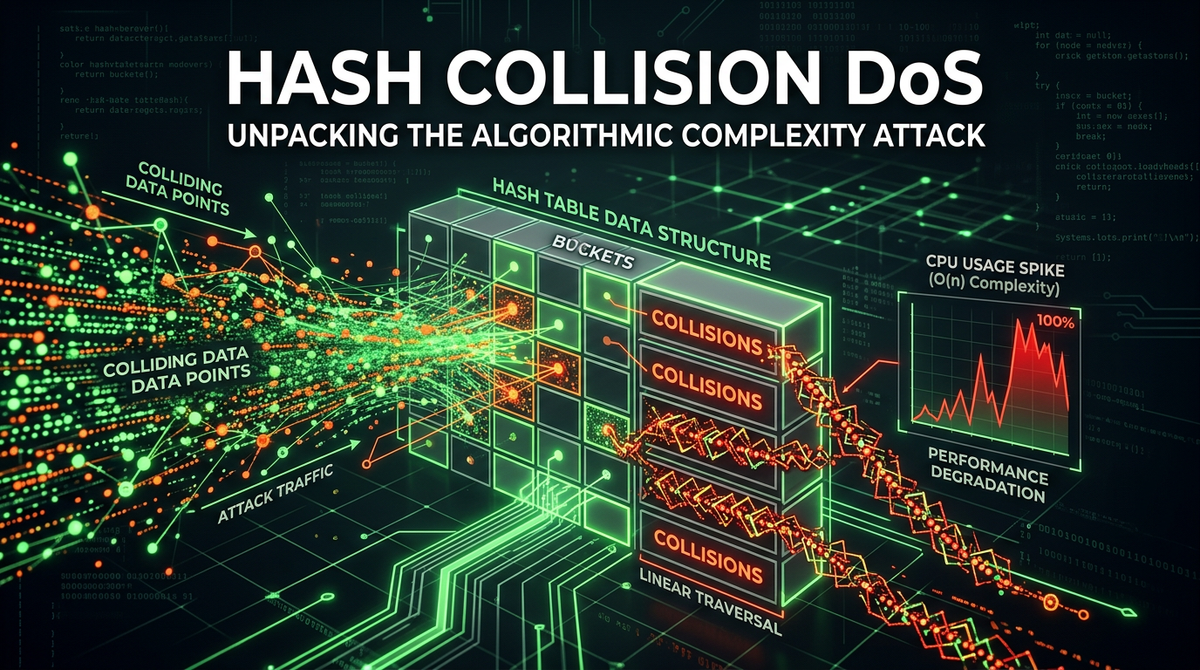
In the realm of cybersecurity, many Denial of Service (DoS) attacks rely on brute force, such as flooding a network with massive amounts of traffic. However, one of the most elegant and devastating forms of resource exhaustion is the Hash Collision DoS attack. Instead of overwhelming a pipe with bandwidth, this attack targets the very logic of how software handles data, turning efficient algorithms into slow, CPU-consuming nightmares. By understanding how hash tables function and where they fail, developers and security professionals can better defend their infrastructure from these sophisticated algorithmic complexity attacks.
Understanding Hash Tables and Efficiency
To understand a Hash Collision DoS, we must first understand the data structure it targets: the Hash Table (or Hash Map). In computer science, a hash table is used to store key-value pairs. It is prized for its efficiency, offering an average time complexity of O(1) for insertions, deletions, and lookups. This means that regardless of whether you have 10 items or 10 million items, finding a specific piece of data takes roughly the same amount of time.
How Hash Functions Work
A hash table relies on a "hash function." This function takes an input (like a string) and converts it into a numerical index (a hash). This index determines where in an internal array the data should be stored. For example, if you provide the key "Username," the hash function might return the index 5. The value associated with "Username" is then stored at position 5 in the array.
In an ideal world, every unique input would produce a unique index. However, because the range of possible inputs (infinite) is much larger than the size of the internal array (finite), two different inputs will eventually produce the same index. This event is known as a hash collision.
The Mechanics of a Hash Collision
When a collision occurs, the hash table must have a strategy to handle it. The most common method is called Separate Chaining. In this model, each "bucket" in the array is not just a single slot, but a linked list. If two keys hash to the same index, they are both stored in that linked list.
Under normal operating conditions, these linked lists are very short (usually 0 or 1 item). However, if an attacker can find thousands of different keys that all hash to the exact same index, the linked list grows significantly.
Algorithmic Complexity Attacks Explained
When a linked list in a hash table becomes very long, the time complexity of looking up or inserting an item shifts from O(1) (constant time) to O(n) (linear time), where 'n' is the number of colliding keys.
If an attacker sends a POST request to a web application containing 50,000 parameters that all collide, the server will spend an enormous amount of CPU cycles processing that single request. While a normal request might take a few milliseconds, a collision-heavy request could take minutes of 100% CPU usage. By sending just a handful of these requests, an attacker can completely freeze a multi-core server.
How to Exploit Hash Collision DoS
Exploiting this vulnerability requires the attacker to know (or guess) which hash function the target application is using. Historically, many programming languages used predictable, non-randomized hash functions, making them easy targets.
Crafting the Payload
To craft a payload, an attacker identifies strings that produce the same hash value. In older versions of Java, for example, the hashCode() function for strings was very simple. It used a mathematical formula where certain characters could be swapped to maintain the same result.
Consider the strings "Aa" and "BB". In many simple hash implementations, these might collide. An attacker can then use combinations of these to generate thousands of collisions:
- "AaAa"
- "AaBB"
- "BBAa"
- "BBBB"
By generating a massive list of these strings, the attacker creates a payload. Here is a conceptual example of what a malicious HTTP POST request might look like:
POST /submit-form HTTP/1.1
Host: target-app.com
Content-Type: application/x-www-form-urlencoded
Content-Length: [Large Value]
AaAa=1&AaBB=2&BBAa=3&BBBB=4&... [repeated 50,000 times]
Exploiting Web Frameworks
Most modern web frameworks automatically parse incoming form data or JSON into a dictionary or hash map. This happens before the application logic even runs. If the framework's underlying language (like PHP, Python, or Ruby) is vulnerable to hash collisions, the mere act of receiving the request is enough to trigger the DoS. The server will hang while trying to build the internal data structure for the parameters.
Real-World Examples and Historical Context
The most famous instance of this attack occurred in 2011, when researchers demonstrated "hashdos" at the 28C3 conference. They showed that platforms including PHP, ASP.NET, Java, Python, and Ruby were all vulnerable.
For instance, in PHP 5, an attacker could send a request with 65,536 parameters. Because PHP used a simple hashing algorithm for its associative arrays, this single request could tie up a server core for approximately 30 seconds. A small botnet could easily take down large-scale web clusters with minimal bandwidth.
In response, most language maintainers introduced "Hash Flooding" protections. For example, PHP introduced the max_input_vars configuration setting, which limits the number of GET/POST variables accepted in a single request (defaulting to 1000).
Impact on Infrastructure
The impact of a successful Hash Collision DoS is primarily Resource Exhaustion. Unlike a volumetric DDoS that targets the network, this targets the CPU and Memory.
- CPU Spikes: The primary symptom is 100% CPU utilization on the web or application server. This happens because the CPU is stuck in a loop traversing long linked lists.
- Service Unavailability: Legitimate users cannot get a response from the server because the worker processes are busy processing the malicious payload.
- Cost: For organizations using auto-scaling cloud infrastructure, a Hash Collision DoS can lead to an "Economic Denial of Sustainability" (EDoS), where the system keeps spinning up new expensive instances to handle the perceived load, resulting in massive bills.
- Bypassing WAFs: Because the payload looks like a standard (albeit large) form submission, many traditional Web Application Firewalls (WAFs) that only look for signatures (like SQLi or XSS) may let it through.
Mitigation and Prevention Strategies
Protecting against Hash Collision DoS requires a defense-in-depth approach, starting from the application code up to the infrastructure level.
1. Randomized Hashing (SipHash)
Most modern programming languages have switched to randomized hash functions like SipHash. These functions use a secret "seed" or "key" that is generated when the process starts. Because the attacker does not know the seed, they cannot predict which strings will collide. Even if they find collisions for their local machine, those same strings will not collide on the target server.
If you are using an older version of a language (e.g., Python 2.7 or PHP 5), it is critical to upgrade to a version where hash randomization is enabled by default.
2. Limit Input Complexity
You should always limit the amount of data a user can send. This includes:
- Max Parameter Count: Limit the number of keys allowed in a POST body or JSON object (e.g.,
max_input_varsin PHP). - Max Request Size: Limit the total size of the HTTP request body at the web server level (e.g.,
client_max_body_sizein Nginx).
3. Use Better Data Structures
In some high-performance scenarios, developers replace standard hash tables with structures that have better worst-case performance. For example, a Balanced Binary Search Tree (like a Red-Black Tree) has a worst-case lookup time of O(log n). While slower than O(1) on average, it is immune to the O(n) degradation that enables Hash Collision DoS.
4. Infrastructure Monitoring
Monitoring your external attack surface is vital. If you notice unusual CPU spikes that coincide with large POST requests, you may be under attack. Tools that analyze the complexity of incoming requests can help identify these patterns before they cause a full outage.
Conclusion
Hash Collision DoS is a powerful reminder that security is not just about blocking malicious strings; it is about understanding the mathematical foundations of our software. By exploiting the gap between average-case and worst-case algorithmic performance, attackers can cause significant disruption with very little effort. Ensuring your environment uses randomized hashing and enforces strict limits on input variables is the best way to stay protected.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



