What is GraphQL N+1 Problem? Ways to Exploit, Examples and Impact
Understand the GraphQL N+1 problem, its security impact, and how to prevent Denial of Service attacks with DataLoaders and query complexity analysis.
GraphQL has revolutionized the way developers build APIs by allowing clients to request exactly the data they need and nothing more. However, this flexibility comes with a significant performance and security trade-off known as the N+1 problem. While often discussed as a performance bottleneck, the N+1 problem is a critical vulnerability that can be exploited to launch Denial of Service (DoS) attacks, potentially crippling an organization's infrastructure. Understanding how this issue arises and how to mitigate it is essential for any modern cybersecurity professional or developer.
What is the GraphQL N+1 Problem?
To understand the N+1 problem, we first need to look at how Jsmon and other modern applications handle data fetching. In a traditional REST API, fetching a list of users and their respective posts might require two distinct endpoints: /users and /posts?userId=123. The client controls the flow, but the server defines the structure.
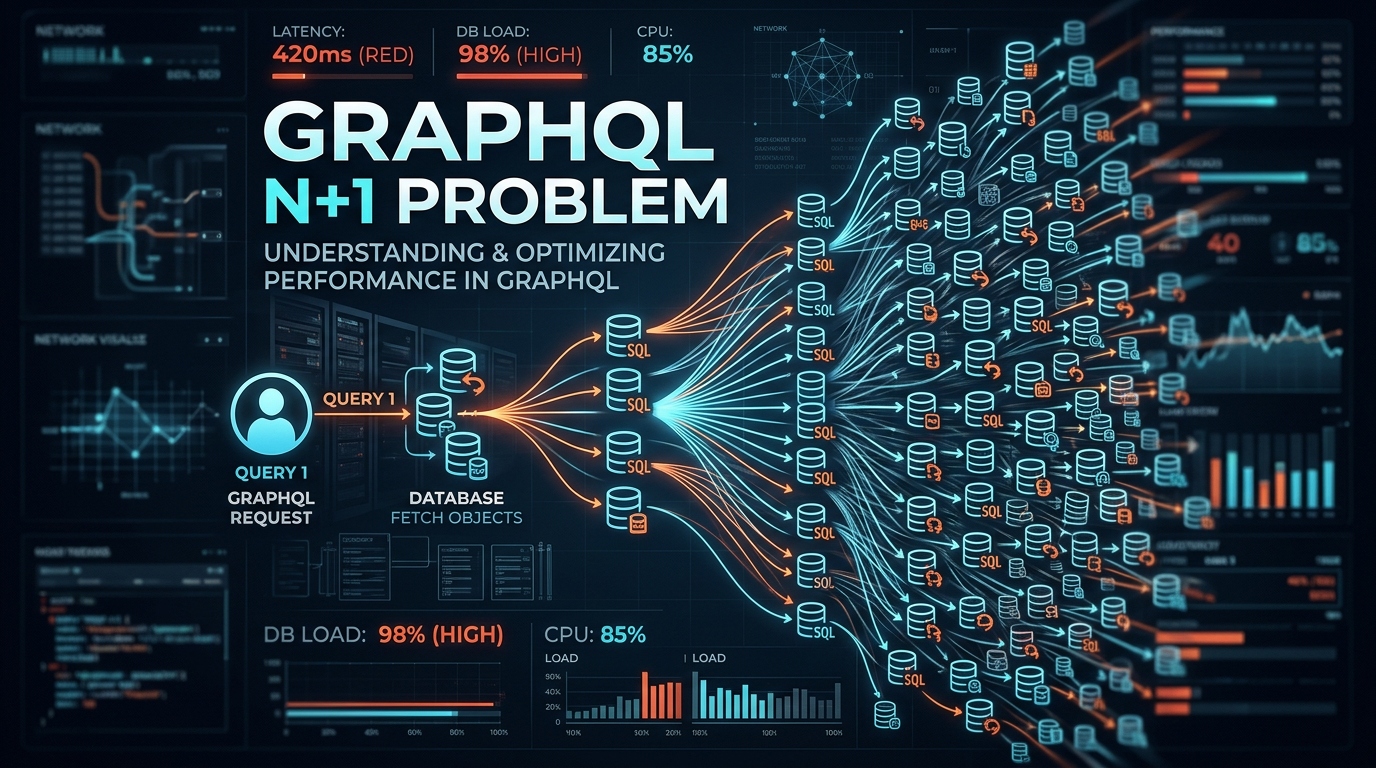
In GraphQL, the client sends a single query that describes a nested relationship. For example, a client might ask for a list of all users and the titles of all posts written by each user. The N+1 problem occurs when the server-side implementation executes one database query to fetch the list of users (the "1"), and then executes a separate database query for each individual user to fetch their posts (the "N").
If you have 100 users, a single GraphQL query results in 101 database queries (1 for the users + 100 for the posts). As the number of records grows, the load on the database increases exponentially, leading to severe latency and eventual system failure.
Technical Deep Dive: Why Does It Happen?
The root cause of the N+1 problem lies in how GraphQL resolvers function. A resolver is a function responsible for fetching the data for a specific field in the schema. GraphQL executes these resolvers independently and recursively.
Consider this simplified schema:
type User {
id: ID!
username: String!
posts: [Post]
}
type Post {
id: ID!
title: String!
content: String!
}
type Query {
allUsers: [User]
}
A naive implementation of the posts resolver in a Node.js environment might look like this:
const resolvers = {
Query: {
allUsers: async (parent, args, context) => {
// 1 Query: SELECT * FROM users;
return await context.db.Users.findAll();
},
},
User: {
posts: async (user, args, context) => {
// N Queries: SELECT * FROM posts WHERE userId = user.id;
return await context.db.Posts.findAll({ where: { userId: user.id } });
},
},
};
When the engine processes allUsers, it calls the allUsers resolver once. It then iterates through every user returned and calls the User.posts resolver for each one. This "atomic" nature of resolvers is what makes GraphQL powerful but also what introduces the N+1 vulnerability if not handled with batching logic.
How to Exploit the N+1 Problem
From a security perspective, the N+1 problem is a gift to attackers looking to perform resource exhaustion. Because GraphQL allows for deeply nested queries, an attacker can craft a payload that forces the server to execute thousands, or even millions, of database queries in a single HTTP request.
1. Nested Resource Exhaustion
If the schema allows for bidirectional relationships (e.g., Users have Posts, and Posts have Authors), an attacker can create a circular or deeply nested query.
query {
allUsers {
posts {
author {
posts {
author {
username
}
}
}
}
}
}
In this scenario, if there are 50 users and each has 10 posts, the number of database calls explodes. The server will spend all its CPU cycles and database connections trying to resolve this single request, effectively denying service to legitimate users.
2. Batching Exploitation
Many GraphQL implementations support "Query Batching," where a client sends an array of queries in a single POST request. If the server does not have global rate limiting or complexity analysis, an attacker can send 100 identical N+1-heavy queries in one request, multiplying the impact of the resource exhaustion.
[
{ "query": "{ allUsers { posts { title } } }" },
{ "query": "{ allUsers { posts { title } } }" },
{ "query": "{ allUsers { posts { title } } }" }
]
3. Alias Overloading
Attackers can use GraphQL aliases to bypass simple field-counting protections. By aliasing the same expensive field multiple times, they can trigger the N+1 logic repeatedly within the same query block.
query {
u1: allUsers { posts { title } }
u2: allUsers { posts { title } }
u3: allUsers { posts { title } }
# ... repeated 50 times
}
The Impact of N+1 Vulnerabilities
The impact of an unmitigated N+1 problem ranges from minor performance degradation to total infrastructure collapse:
- Database Bottlenecks: The database becomes the primary point of failure. High connection counts and CPU usage can lead to deadlocks or slow queries for all applications sharing that database.
- Increased Latency: Even if the server doesn't crash, the Time to First Byte (TTFB) increases significantly, leading to a poor user experience and potential timeouts in downstream microservices.
- Financial Costs: In cloud environments (AWS, GCP, Azure), auto-scaling groups might spin up dozens of new instances to handle the perceived load, leading to massive unexpected bills.
- Application DoS: The most severe impact is a complete Denial of Service. If an attacker can keep the server busy with expensive queries, legitimate traffic cannot be processed.
How to Detect N+1 Issues
Before you can fix the problem, you must identify where it occurs. Technical teams can use several methods to spot N+1 vulnerabilities:
- Database Logging: Enable query logging in your development environment. If you see a flurry of identical
SELECTstatements with different IDs following a single GraphQL request, you have an N+1 problem. - Performance Monitoring (APM): Tools like New Relic or Datadog can visualize the trace of a request. A "waterfall" pattern in the trace is a classic sign of sequential N+1 resolving.
- Static Analysis: Use linting tools for GraphQL that flag fields without defined batching logic.
- Infrastructure Reconnaissance: Using Jsmon allows security teams to map out their external attack surface and identify exposed GraphQL endpoints that might be susceptible to these types of resource exhaustion attacks.
How to Prevent and Mitigate N+1 Problems
Fortunately, there are well-established patterns to solve the N+1 problem. The most common solution is batching and caching using a pattern called DataLoader.
1. Using DataLoaders
DataLoader is a utility (originally developed by Facebook) that collects all the IDs requested during a single tick of the event loop and fetches them in a single batch query.
Here is how the previous resolver would look with a DataLoader:
const postLoader = new DataLoader(async (userIds) => {
// 1 Query: SELECT * FROM posts WHERE userId IN (1, 2, 3...);
const posts = await db.Posts.findAll({ where: { userId: userIds } });
// Map posts back to the correct user ID
return userIds.map(id => posts.filter(p => p.userId === id));
});
const resolvers = {
User: {
posts: (user) => postLoader.load(user.id),
},
};
By using load(), the resolver schedules the ID for fetching. DataLoader then executes the batch function once, reducing N+1 queries back to 2 queries total.
2. Query Depth Limiting
To prevent attackers from sending deeply nested queries, implement depth limiting. This involves analyzing the AST (Abstract Syntax Tree) of the incoming query and rejecting it if the nesting exceeds a certain threshold (e.g., 5 levels).
import depthLimit from 'graphql-depth-limit';
const server = new ApolloServer({
schema,
validationRules: [depthLimit(5)],
});
3. Query Complexity Analysis
Depth alone isn't always enough. A shallow query can still be expensive if it requests many fields with N+1 issues. Complexity analysis assigns a "cost" to each field. If the total cost of a query exceeds a predefined limit, the server rejects it.
4. Persisted Queries
For high-security environments, you can use Persisted Queries. Instead of allowing clients to send arbitrary GraphQL strings, the server only executes pre-approved queries stored in a database. The client simply sends a hash of the query. This completely eliminates the possibility of an attacker crafting a malicious N+1 payload.
Conclusion
The GraphQL N+1 problem is more than just a performance quirk; it is a fundamental architectural challenge that can lead to significant security vulnerabilities. By understanding the recursive nature of GraphQL resolvers, developers can proactively implement DataLoaders and query complexity limits to safeguard their infrastructure. As organizations continue to adopt GraphQL, the ability to identify and mitigate these risks becomes a core competency for maintaining resilient and secure applications.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.