What is Business Logic Vulnerability? Ways to Exploit, Examples and Impact
Discover common business logic flaws, real-world exploit examples, and prevention strategies to secure your web applications against logical attacks.
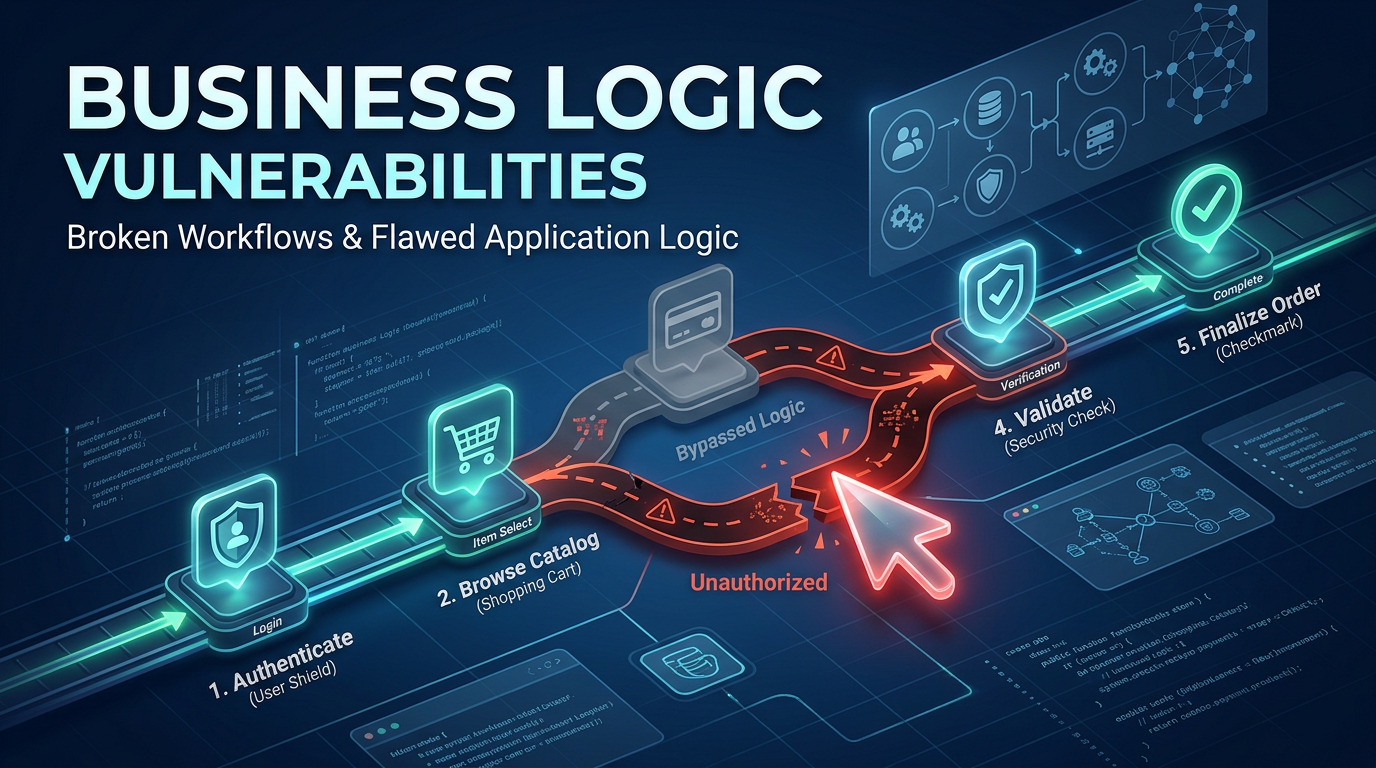
In the world of cybersecurity, we often focus on technical vulnerabilities like SQL injection, Cross-Site Scripting (XSS), or Buffer Overflows. However, there is a class of vulnerabilities that doesn't rely on malformed code or syntax errors, but rather on flaws in the very design and implementation of an application's processes. These are known as Business Logic Vulnerabilities. Unlike traditional bugs, these flaws occur when an application behaves in an unexpected way because the developers didn't account for specific user behaviors or edge cases in the business workflow.
What is a Business Logic Vulnerability?
A Business Logic Vulnerability (BLV) is a flaw in the design and implementation of an application that allows an attacker to manipulate the intended workflow of the business. These vulnerabilities are unique because they are often "valid" from a technical standpoint—the code executes perfectly, the database queries are sanitized, and the server doesn't crash. However, the result of the action is something the business never intended, such as purchasing an item for free, accessing another user's private data, or bypassing a mandatory payment step.
Because these flaws are deeply rooted in the specific logic of an application, they are notoriously difficult for automated scanners to detect. A vulnerability scanner knows what a SQL injection payload looks like, but it doesn't understand that your specific application shouldn't allow a user to apply a "100% off" coupon code twice. Identifying these issues requires a deep understanding of the business domain and manual testing by security professionals.
The Difference Between Technical and Logical Flaws
To understand business logic flaws, it helps to contrast them with technical flaws.
Technical Flaws
Technical flaws, such as a missing mysql_real_escape_string() call, occur because of a failure in secure coding practices. They are universal across different applications. A SQL injection in a banking app looks very similar to a SQL injection in a blog. Tools like Jsmon can help map the attack surface where these technical entry points might exist.
Logical Flaws
Logical flaws are application-specific. They occur when the code does exactly what it was told to do, but the instructions themselves were flawed. For example, if a developer writes a function that subtracts a discount from a total but forgets to check if the resulting total is negative, the code is technically sound but logically broken. An attacker could potentially receive money back from the store by applying enough discounts.
Common Categories of Business Logic Vulnerabilities
While every application has unique logic, most business logic vulnerabilities fall into several common categories. Understanding these patterns is the first step toward better security.
1. Trusting Client-Side Input
This is perhaps the most common logic flaw. Developers sometimes assume that because a value is set in a hidden field, a dropdown menu, or a read-only input, the user cannot change it. Attackers can use proxy tools like Burp Suite to intercept the HTTP request and modify these values before they reach the server.
2. Broken Workflow or State Machine Bypass
Many applications require users to complete steps in a specific order (e.g., Step 1: Provide Info, Step 2: Payment, Step 3: Confirmation). A logic vulnerability exists if the server doesn't verify that Step 2 was successfully completed before allowing the user to access Step 3. By simply navigating directly to the URL for Step 3, an attacker might bypass the payment gateway entirely.
3. Numerical Integrity Flaws
These occur when an application fails to perform sanity checks on mathematical operations. Examples include allowing negative quantities in a shopping cart, which might subtract the price from the total, or failing to cap the number of times a referral code can be used.
4. Privilege Escalation through Logic
This happens when the application makes assumptions about a user's role based on logical triggers rather than strict session management. For instance, an application might allow any user to access an admin panel if they simply add a parameter like ?admin=true to the URL.
Detailed Exploitation Scenarios and Examples
Let’s dive into some technical examples of how these vulnerabilities look in the real world.
Example 1: Price Manipulation via Parameter Tampering
Imagine an e-commerce site where the checkout process involves a POST request to /checkout/process. The request looks like this:
POST /checkout/process HTTP/1.1
Host: example-store.com
Content-Type: application/x-www-form-urlencoded
product_id=102&quantity=1&price=499.00&shipping=10.00
In this scenario, the developer has mistakenly included the price parameter in the client-side request. An attacker can intercept this request and modify the price to a lower value, or even a negative value:
POST /checkout/process HTTP/1.1
Host: example-store.com
Content-Type: application/x-www-form-urlencoded
product_id=102&quantity=1&price=0.01&shipping=0.00
If the server-side code trusts the price sent by the client instead of fetching the authoritative price from the database, the attacker successfully purchases a $499 item for one cent. This is a classic business logic failure involving excessive trust in client-side data.
Example 2: Bypassing the 2FA Logic
Consider a login process that requires Two-Factor Authentication (2FA). The flow is:
- User enters username and password.
- Server validates credentials and redirects to
/login/otp. - User enters OTP code.
- Server validates OTP and redirects to
/dashboard.
A logic flaw might exist if the server sets the authenticated session cookie immediately after step 1, but simply relies on the UI to prevent the user from seeing the dashboard until step 3 is finished. An attacker could log in with a password and then manually navigate to /dashboard, bypassing the OTP requirement entirely.
Alternatively, consider an application that uses a boolean flag in the session to track 2FA status:
// Vulnerable server-side logic (Pseudocode)
if (user.checkPassword(pass)) {
session.user_id = user.id;
session.needs_2fa = true;
res.redirect('/otp-page');
}
// Dashboard check
if (session.user_id) {
// Missing check for session.needs_2fa == false
res.render('dashboard');
}
In this case, the developer forgot to check the needs_2fa flag on the dashboard route. Jsmon can help you identify all the subdomains and endpoints that might be missing these critical checks during your reconnaissance phase.
Example 3: Infinite Discount Loop
Some applications allow users to apply multiple coupon codes. A logic flaw occurs if the system doesn't check if the total discount exceeds the total price.
Suppose an attacker finds a coupon code WELCOME10 for $10 off. If the application logic allows the same code to be applied multiple times by repeatedly sending the request, or if it allows different codes to stack until the price becomes negative, the attacker can drain the store's balance or get items for free.
POST /cart/apply-coupon HTTP/1.1
Host: example-store.com
coupon_code=WELCOME10&coupon_code=WELCOME10&coupon_code=WELCOME10...
If the backend logic is Total = Total - (CouponValue * Count), and Count is not restricted to 1, the logic is broken.
The Impact of Business Logic Vulnerabilities
The impact of these vulnerabilities is often more direct and severe than technical bugs because they target the core revenue and data of a company.
- Financial Loss: Direct theft of funds, unauthorized discounts, or bypassing payment gateways.
- Data Breaches: Unauthorized access to sensitive user data (PII) by manipulating identifiers in logical workflows.
- Reputational Damage: Loss of customer trust when users realize the platform's rules can be easily circumvented.
- Operational Disruption: Attackers might use logic flaws to exhaust resources, such as creating thousands of fake accounts or locking out legitimate users through flawed account recovery processes.
Why Automated Scanners Often Fail to Detect Logic Flaws
Most DAST (Dynamic Application Security Testing) and SAST (Static Application Security Testing) tools operate on a set of known signatures. They look for patterns that indicate common vulnerabilities. However, business logic is inherently custom.
An automated tool cannot know that:
- A user should not be able to cancel an order that has already been shipped.
- A "Points Transfer" feature should not allow a user to transfer more points than they own.
- A password reset token should be invalidated immediately after use.
Detecting these requires context. You must understand what the application is supposed to do before you can identify what it shouldn't do. This is why manual penetration testing and threat modeling are essential components of a robust security posture.
How to Prevent Business Logic Vulnerabilities
Preventing these flaws requires a shift in how we approach software design and development. Here are some actionable strategies:
1. Never Trust the Client
Assume all data coming from the user's browser is malicious. Always re-validate prices, quantities, and permissions on the server side using authoritative data from your database.
2. Maintain a Strict State Machine
For multi-step processes, the server must keep track of the user's current state. If a user tries to access Step 3, the server should check its own records to ensure Step 2 was successfully completed and validated. Do not rely on the client to tell you which step it is on.
3. Use Clear and Consistent Authorization Checks
Every single endpoint—including API endpoints used by mobile apps or AJAX calls—must perform an authorization check. Never assume that because a link is hidden in the UI, an attacker cannot find and call the underlying API.
4. Implement Sanity Checks and Limits
Apply limits to all numerical inputs. Can a quantity be negative? Can it be zero? Can a user apply more than one discount? By defining these constraints early in the development process, you can prevent many common logic flaws.
5. Threat Modeling During Design
Before writing code, walk through the business process and ask "What if?" What if a user skips this step? What if they provide a negative value? What if they submit this request twice? Identifying these possibilities during the design phase is much cheaper than fixing them after a breach.
Conclusion
Business logic vulnerabilities represent a significant risk because they bypass traditional security defenses by exploiting the very rules the application was built to follow. While technical vulnerabilities are being increasingly mitigated by secure frameworks and automated tools, logical flaws remain a fertile ground for attackers. By adopting a "trust nothing" approach to client input and rigorously enforcing state and authorization on the server, organizations can defend against these subtle but devastating attacks.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



