What is Broken Object Level Authorization (BOLA)? Ways to Exploit, Examples and Impact
Master Broken Object Level Authorization (BOLA). Learn technical exploitation methods and how to secure your APIs against the #1 OWASP threat.
In the modern landscape of web applications and microservices, APIs are the connective tissue that allows data to flow between clients and servers. However, this architectural shift has introduced significant security challenges. At the top of the list is Broken Object Level Authorization (BOLA). Formerly known as Insecure Direct Object Reference (IDOR), BOLA consistently ranks as the number one threat in the OWASP API Security Top 10. Understanding BOLA is not just a matter of compliance; it is a critical necessity for any developer or security professional aiming to protect sensitive user data.
What is Broken Object Level Authorization (BOLA)?
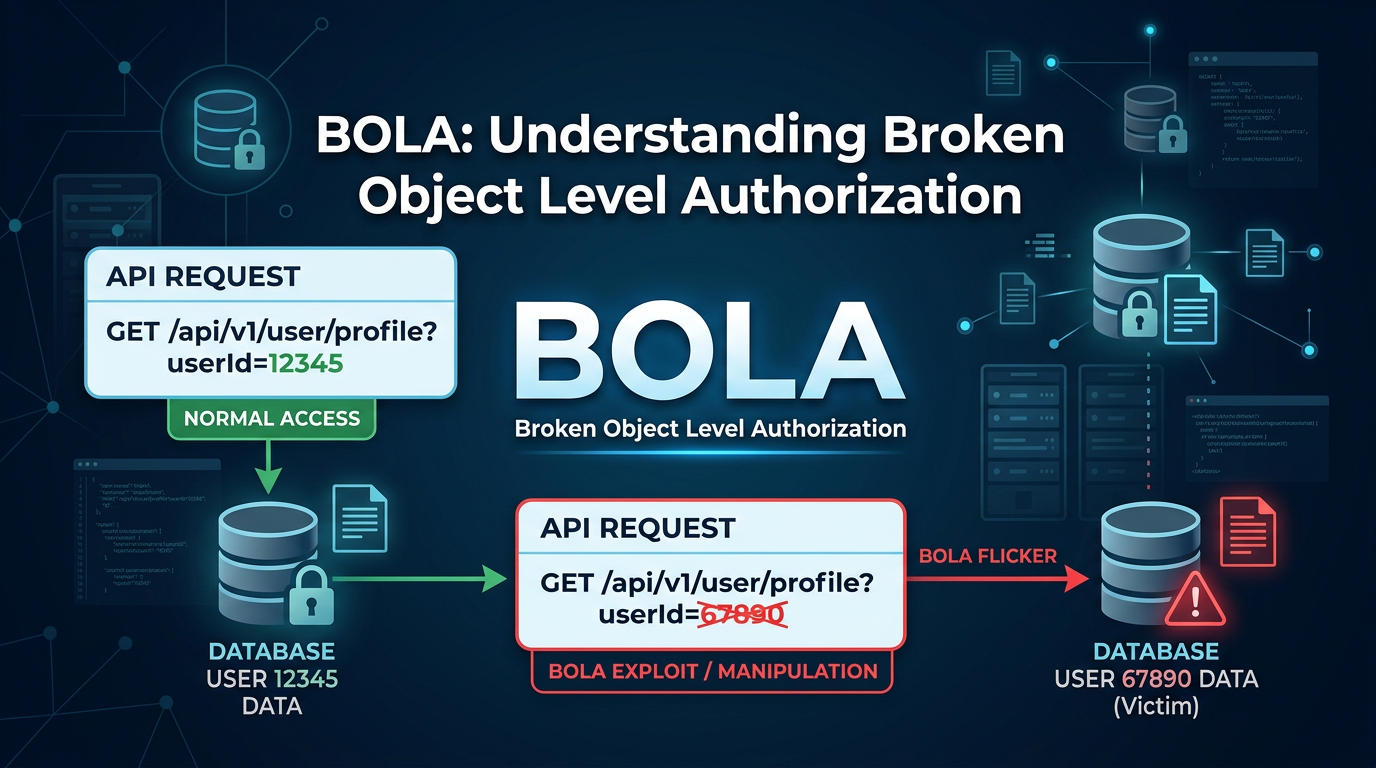
Broken Object Level Authorization occurs when an application does not properly validate whether a user has the necessary permissions to access a specific object or resource via its unique identifier. In a typical BOLA scenario, an attacker manipulates the ID of an object in an API request to access data belonging to another user.
To understand BOLA, we must distinguish between authentication and authorization. Authentication is the process of verifying who a user is (e.g., logging in with a password). Authorization is the process of verifying what that user is allowed to do. BOLA is a failure of authorization. Even if a user is legitimately logged in, the system fails to check if that specific user should be allowed to interact with the specific resource ID they are requesting.
The Mechanics of an Object Reference
Every time you view your profile, check an order status, or delete a comment, the frontend application makes a request to a backend API. This request usually includes a unique identifier (ID) for the object in question. These IDs are often visible in the URL or the body of an HTTP request. For example:
GET /api/v1/messages/4501POST /api/v1/billing/invoice/INV-9928/downloadPUT /api/v1/users/882/settings
If the server only checks if the user is logged in but fails to check if user 882 is actually the person making the request to /api/v1/users/882/settings, a BOLA vulnerability exists.
Why BOLA is a Critical Security Risk
BOLA is particularly dangerous because it is incredibly easy to exploit but can lead to massive data breaches. Unlike complex memory corruption bugs or cryptographic failures, BOLA exploitation often requires nothing more than a web browser or a basic command-line tool like curl. Because many modern applications rely on sequential integers or predictable strings for database primary keys, an attacker can simply "fuzz" or iterate through IDs to scrape entire databases.
How to Identify BOLA Vulnerabilities
Identifying BOLA requires a mix of manual testing and automated scanning. Because the vulnerability lies in the business logic of the application, traditional automated vulnerability scanners often miss it. They see a 200 OK response and assume the request was valid, without knowing that the data returned should have been private.
1. Mapping API Endpoints
The first step in a security audit is mapping out all API endpoints that handle object IDs. Look for parameters in the URL path, query strings, or JSON bodies that look like database keys or resource identifiers.
2. Testing with Multiple Accounts
The most effective way to find BOLA is to use two different user accounts (User A and User B).
- Capture a request from User A that accesses a private resource (e.g.,
GET /api/v1/user/A_ID/profile). - Attempt to replay that request while logged in as User B, but keep User A's ID in the request.
- If the server returns User A’s private data to User B, you have confirmed a BOLA vulnerability.
Technical Examples of BOLA Exploitation
Let’s look at some concrete technical scenarios to illustrate how these attacks manifest in the real world.
Example 1: Sequential ID Manipulation
Imagine a fitness tracking application where users can view their workout history. When a user clicks on a specific workout, the app sends the following request:
GET /api/v1/workouts/5501 HTTP/1.1
Host: fitness-app.com
Authorization: Bearer <User_A_Token>
The server responds with:
{
"id": 5501,
"user_id": "user_99",
"date": "2023-10-01",
"route_data": "[GPS coordinates...]",
"heart_rate": 165
}
An attacker notices the ID 5501. They suspect the IDs are sequential. They use a simple script to iterate through IDs:
for id in {5500..5600}; do
curl -H "Authorization: Bearer <Attacker_Token>" \
https://fitness-app.com/api/v1/workouts/$id
done
If the server returns workout data for IDs 5502, 5503, etc., the attacker has successfully exploited BOLA to harvest the private GPS and health data of hundreds of other users.
Example 2: BOLA in POST/PUT Requests
BOLA is not limited to GET requests. It can also be used to modify or delete data. Consider an e-commerce platform where users can update their shipping address:
PUT /api/v1/address/update HTTP/1.1
Host: shop.jsmon.sh
Content-Type: application/json
Authorization: Bearer <User_A_Token>
{
"address_id": "addr_7721",
"street": "123 Secure Lane",
"city": "Cyber City"
}
If the backend code looks like this (in a pseudo-Node.js environment):
app.put('/api/v1/address/update', async (req, res) => {
const { address_id, street, city } = req.body;
// VULNERABLE CODE: Only checks if user is logged in
if (!req.user) return res.status(401).send();
// Updates the address regardless of who owns it
await db.addresses.update({ id: address_id }, { street, city });
res.status(200).send("Address updated");
});
An attacker can change address_id to addr_7722 (belonging to User B) and redirect User B's packages to the attacker's house. This is a high-impact BOLA exploit affecting data integrity.
Example 3: Exploiting UUIDs and Non-Predictable IDs
Many developers believe that using UUIDs (Universally Unique Identifiers) like f47ac10b-58cc-4372-a567-0e02b2c3d479 mitigates BOLA because they are impossible to guess. While UUIDs prevent "ID scraping" via brute force, they do not fix the underlying authorization flaw.
If a UUID is leaked elsewhere—perhaps in a public comment section, a support ticket, or a different API endpoint—the attacker can still use it. For instance, a public API might reveal a user's UUID:
GET /api/v1/posts/public/1
Response: { "author_id": "f47ac10b...", "content": "Hello world" }
The attacker then uses that author_id in a private endpoint:
GET /api/v1/users/f47ac10b.../private-messages
If the server responds with messages, the use of UUIDs provided zero protection against the BOLA vulnerability.
The Impact of BOLA on Organizations
The consequences of a BOLA vulnerability can be devastating:
- Mass Data Exfiltration: Attackers can automate the collection of millions of records, including PII (Personally Identifiable Information), leading to GDPR or CCPA violations.
- Account Takeover: If an attacker can modify object IDs related to password resets or email settings, they can take full control of user accounts.
- Financial Loss: In fintech applications, BOLA can allow attackers to view transaction histories, download invoices, or even initiate unauthorized transfers.
- Reputational Damage: Once a BOLA-driven breach is made public, customer trust evaporates, often leading to a significant drop in stock price or user base.
BOLA vs. IDOR: What is the Difference?
In many security circles, BOLA and IDOR are used interchangeably. Historically, IDOR (Insecure Direct Object Reference) was the term used in the OWASP Top 10 for web applications. However, as the industry shifted toward API-centric architectures, OWASP introduced a specific list for APIs.
BOLA is essentially the modern, API-focused evolution of IDOR. While IDOR often referred to manipulating URL parameters in traditional web pages (like profile.php?id=10), BOLA encompasses the broader scope of object access across REST, GraphQL, and other API protocols where objects are manipulated through various HTTP methods and complex JSON structures.
How to Prevent Broken Object Level Authorization
Securing an application against BOLA requires a defense-in-depth approach. You cannot rely on a single "fix"; instead, you must build authorization into the very fabric of your data access layer.
1. Implement Strict Authorization Checks
Every single endpoint that accepts an ID from the client must verify that the logged-in user has permission to access that specific ID.
Correct Implementation (Node.js/Express example):
app.get('/api/v1/orders/:orderId', async (req, res) => {
const { orderId } = req.params;
const userId = req.user.id; // From authenticated session/token
const order = await db.orders.findOne({ id: orderId });
if (!order) {
return res.status(404).send("Order not found");
}
// SECURE CHECK: Compare the owner of the resource to the current user
if (order.ownerId !== userId) {
return res.status(403).send("You do not have permission to view this order");
}
res.json(order);
});
2. Use Random, Non-Predictable IDs
While UUIDs are not a complete fix, they should still be used. They make it significantly harder for attackers to discover other valid IDs. Use Version 4 UUIDs or similar cryptographically secure identifiers for all public-facing resources.
3. Adopt a "Least Privilege" Policy
Ensure that users and services only have access to the data they absolutely need. If a mobile app only needs to show the last 5 transactions, the API should not provide an endpoint that returns the entire transaction history unless explicitly authorized.
4. Continuous Monitoring and Auditing
Security is not a one-time event. As your codebase grows, new BOLA vulnerabilities can be introduced. Use automated tools to monitor your external attack surface. Platforms like Jsmon can help you keep track of your infrastructure and identify changes that might expose new API endpoints to the public internet.
5. Centralized Authorization Logic
Avoid writing authorization checks manually in every controller. Instead, use a centralized middleware or an authorization library (like Casbin or Oso) that enforces policies consistently across the entire application. This reduces the chance of a developer forgetting to add a check to a new endpoint.
Conclusion
Broken Object Level Authorization remains the most prevalent and impactful vulnerability in the API world. Its simplicity for attackers and its potential for massive data exposure make it a top priority for security teams. By moving beyond simple authentication and implementing robust, object-level authorization checks, developers can protect their users and their organization's integrity.
Testing for BOLA should be a standard part of your Development Lifecycle (SDLC). Always assume that any ID provided by a client is untrusted and must be validated against the current user's session on the server side.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



