What is Birthday Attack? Ways to Exploit, Examples and Impact
In the realm of cryptography, the security of digital communication often rests on the assumption that specific mathematical functions are impossible to reverse or duplicate. However, the Birthday Attack—a cryptographic phenomenon based on probability theory—proves that finding collisions in data is much easier than most people intuitively believe. Understanding this attack is critical for any security professional looking to protect data integrity and ensure the robustness of digital signatures.
The Foundation: Understanding the Birthday Paradox
To understand the Birthday Attack, we must first explore the mathematical curiosity known as the Birthday Paradox. The paradox asks a simple question: How many people do you need in a room to have a 50% chance that at least two of them share the same birthday?
Most people, thinking linearly, assume the answer is around 183 (half of 365). However, the actual answer is only 23. This happens because the probability is based on the number of possible pairs of people, not just the number of individuals. With 23 people, there are 253 possible pairs to check for a match. As the group size increases, the number of pairs grows exponentially, making a match statistically likely much sooner than expected.
In cybersecurity, Jsmon emphasizes that these mathematical shortcuts are exactly what attackers use to bypass security controls. In the context of hashing, the Birthday Paradox suggests that finding two different inputs that produce the same hash output (a collision) requires significantly fewer attempts than a brute-force search for a specific hash.
What is a Birthday Attack in Cryptography?
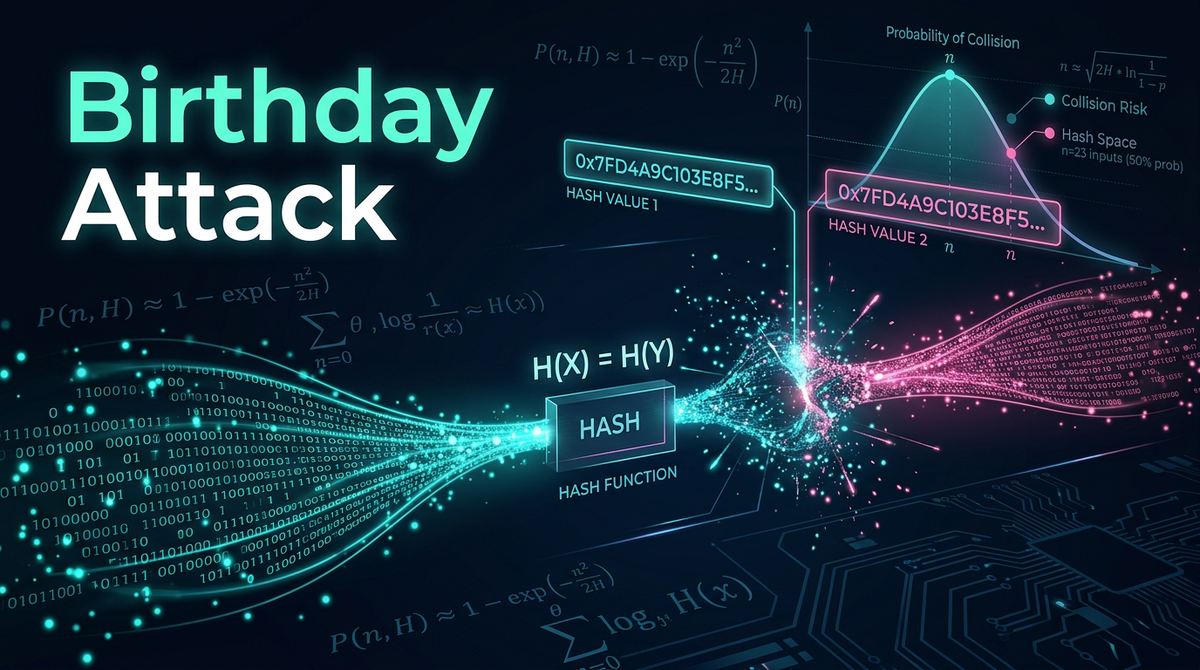
A Birthday Attack is a type of cryptographic attack that exploits the mathematics behind the Birthday Paradox to find collisions in hash functions. A hash function takes an input of any length and produces a fixed-size string of characters, typically a hexadecimal representation. A secure hash function should be "collision-resistant," meaning it should be computationally infeasible to find two different inputs that result in the same output hash.
However, the Birthday Attack proves that for a hash function with an output size of $n$ bits, an attacker only needs to compute approximately $2^{n/2}$ hashes to have a 50% chance of finding a collision. This is a massive reduction from the $2^n$ attempts required for a pre-image attack, where the attacker tries to find an input that matches a specific target hash.
Collision Resistance vs. Pre-image Resistance
To grasp the impact, we must distinguish between two properties of hash functions:
- Pre-image Resistance: Given a hash $H$, it is hard to find any input $x$ such that $Hash(x) = H$. This requires $2^n$ attempts.
- Collision Resistance: It is hard to find any two different inputs $x$ and $y$ such that $Hash(x) = Hash(y)$. This only requires $2^{n/2}$ attempts due to the Birthday Attack.
The Mathematical Probability of a Collision
If we have a hash function with $H$ possible outputs, and we generate $N$ random inputs, the probability $P$ that at least one collision occurs can be approximated using the formula:
$$P(n; H) \approx 1 - e^{-n(n-1)/2H}$$
When $n = \sqrt{H}$, the probability of a collision is roughly 50%. In binary terms, if your hash length is 64 bits ($2^{64}$ possible values), you don't need $2^{64}$ attempts to find a collision; you only need $2^{32}$ (about 4.3 billion) attempts. While 4.3 billion sounds like a lot, modern hardware can compute this in seconds, rendering 64-bit hashes completely insecure against Birthday Attacks.
How a Birthday Attack is Executed
An attacker typically uses a Birthday Attack to commit fraud, particularly in digital signatures. Let's look at a step-by-step scenario involving a malicious contract:
- Preparation: The attacker creates two versions of a document. Document A is a legitimate contract (e.g., "I owe you $100"). Document B is a fraudulent contract (e.g., "I owe you $1,000,000").
- Variation Generation: The attacker makes subtle, invisible changes to both documents. These could include adding trailing spaces, changing font kerning, or adding null characters. By creating $2^{n/2}$ variations of Document A and $2^{n/2}$ variations of Document B, the attacker generates a massive pool of hashes for both.
- Collision Search: The attacker compares the hashes of all variations of Document A against all variations of Document B. Due to the Birthday Paradox, a collision (where a variation of A and a variation of B have the identical hash) is statistically likely to be found quickly.
- Execution: The attacker presents the legitimate Document A to the victim for a digital signature. The victim's software hashes the document and signs it. Because the hash of the fraudulent Document B is identical, the victim's digital signature is now technically valid for the fraudulent document as well.
Practical Python Example: Simulating a Birthday Attack
To see this in action, we can write a simple Python script that simulates a collision search on a truncated hash (to make it run fast). We will use a 24-bit hash space.
import hashlib
import os
def find_collision(bit_length):
num_possible_hashes = 2**bit_length
hashes_seen = {}
attempts = 0
print(f"Searching for a collision in a {bit_length}-bit hash space...")
while True:
attempts += 1
# Generate random data
data = os.urandom(16)
# Create a SHA-256 hash and truncate it to our bit_length
full_hash = hashlib.sha256(data).hexdigest()
# Take only the first few characters to simulate a small hash
truncated_hash = int(full_hash, 16) % num_possible_hashes
if truncated_hash in hashes_seen:
print(f"Collision Found!")
print(f"Attempts: {attempts}")
print(f"Hash: {hex(truncated_hash)}")
print(f"Input 1: {hashes_seen[truncated_hash].hex()}")
print(f"Input 2: {data.hex()}")
break
hashes_seen[truncated_hash] = data
if __name__ == "__main__":
find_collision(24) # 24-bit hash
In this example, $2^{24}$ is roughly 16.7 million. According to the Birthday Paradox, we should find a collision in roughly $\sqrt{2^{24}} = 2^{12} = 4096$ attempts. When you run this, you will notice the collision is found almost instantly, demonstrating why small hash sizes are dangerous.
Real-World Examples and Impact
1. The MD5 Collision (Flame Malware)
MD5 was once the industry standard for hashing. However, researchers demonstrated that Birthday Attacks could produce collisions efficiently. In 2012, the Flame malware used a sophisticated MD5 collision attack to forge a Microsoft digital certificate, allowing it to spread via Windows Update as a "legitimate" patch. This remains one of the most famous examples of a Birthday Attack in the wild.
2. SHA-1 and the SHAttered Attack
In 2017, Google announced the first practical collision for SHA-1, known as "SHAttered." They produced two different PDF files with the same SHA-1 hash. While this required significant computing power (equivalent to 110 GPUs running for a year), it was still $100,000$ times faster than a brute-force attack. This effectively ended the use of SHA-1 for secure digital signatures.
3. Digital Certificate Forgery
Attackers can use Birthday Attacks to generate a Rogue Certificate Authority (CA). By finding a collision between a legitimate certificate request and a malicious one, an attacker can get a trusted CA to sign a certificate that allows the attacker to impersonate any website on the internet, facilitating massive Man-in-the-Middle (MitM) attacks.
Impact on Cybersecurity
The implications of Birthday Attacks are far-reaching:
- Data Integrity Loss: If an attacker can create two different files with the same hash, the hash can no longer be trusted to verify that a file hasn't been tampered with.
- Broken Authentication: Many systems store session tokens or passwords using hashes. If collisions are easy to find, authentication mechanisms can be bypassed.
- Financial Fraud: As seen in the document variation example, Birthday Attacks can be used to swap legitimate financial contracts for fraudulent ones without changing the digital signature.
How to Prevent Birthday Attacks
Preventing a Birthday Attack is primarily about increasing the "cost" of finding a collision. Here are the most effective strategies:
1. Increase Hash Output Length
This is the most direct defense. Since the attack complexity is $2^{n/2}$, doubling the hash length squares the difficulty for the attacker. Moving from a 128-bit hash (MD5) to a 256-bit hash (SHA-256) increases the collision search space from $2^{64}$ to $2^{128}$. Even with the world's most powerful supercomputers, $2^{128}$ remains computationally impossible to crack.
2. Use Modern Hashing Algorithms
Avoid legacy algorithms like MD5 and SHA-1. Use SHA-256, SHA-3, or BLAKE3. These algorithms are designed with collision resistance as a primary requirement and have undergone years of public scrutiny.
3. Salting and Keyed Hashes
In some contexts, using a "Salt" (random data added to the input) or a Message Authentication Code (MAC) like HMAC can mitigate certain types of collision attacks. By requiring a secret key to generate the hash, the attacker cannot easily pre-compute a pool of hashes to find a collision.
4. Monitoring and Attack Surface Management
Organizations often fall victim to Birthday Attacks because they continue to use legacy systems that rely on outdated cryptography. Tools like Jsmon help security teams identify these weak points by mapping the external attack surface and flagging outdated protocols or certificates that might be vulnerable to collision-based exploits.
Conclusion
The Birthday Attack is a powerful reminder that human intuition often fails when dealing with exponential growth and probability. What seems like an impossible task—finding two random inputs with the same hash—becomes trivial when the mathematical shortcut of the Birthday Paradox is applied. As computing power continues to grow, the transition to longer, more secure hashing algorithms is not just a recommendation; it is a necessity for maintaining trust in our digital infrastructure.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



