What is API Injection? Ways to Exploit, Examples and Impact
Master the fundamentals of API Injection. Explore technical examples of SQLi, NoSQLi, and Command Injection, and learn how to secure your API endpoints.
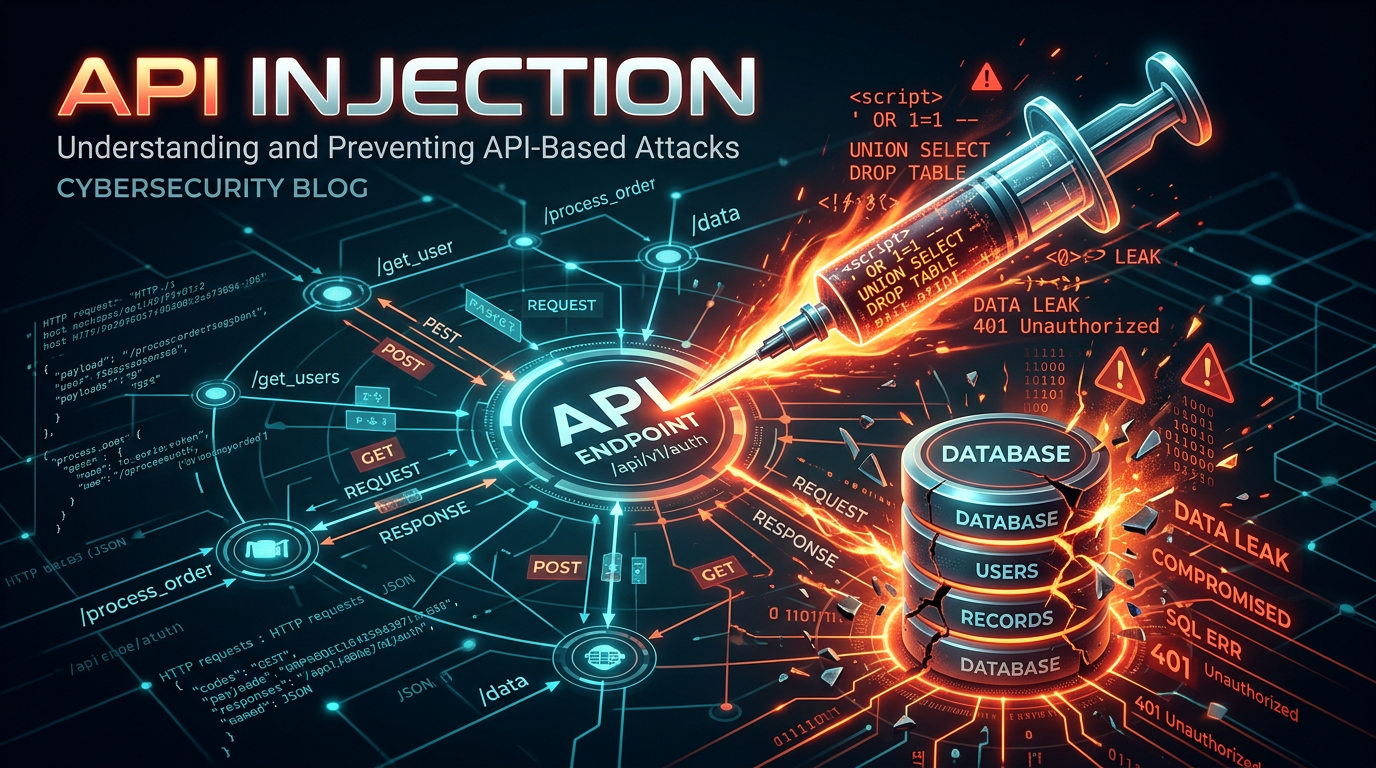
Application Programming Interfaces (APIs) are the connective tissue of the modern internet, enabling seamless communication between disparate software systems. However, this connectivity comes with significant risk; as APIs become more prevalent, they also become primary targets for attackers. API Injection occurs when untrusted data is sent to an interpreter as part of a command or query, leading to unauthorized data access or malicious code execution. Understanding the nuances of these vulnerabilities is critical for any security professional or developer looking to harden their infrastructure.
Understanding the Mechanics of API Injection
At its core, an API injection vulnerability exists because the application fails to properly distinguish between user-supplied data and the instructions intended for the backend system. When an API endpoint accepts input—whether through URI parameters, headers, or the request body—and passes that input directly into a database query, a system command, or a file system call without sufficient sanitization, the "injection" occurs.
In a typical scenario, an API might expect a simple string like a username. An attacker, however, provides a specially crafted string containing syntax characters specific to the language or protocol used by the backend. If the backend interpreter treats these characters as executable code rather than literal data, the attacker gains control over the logic of the operation.
Common Types of API Injection Attacks
API injection is not a single vulnerability but a category that encompasses several distinct attack vectors. Below, we explore the most common types encountered in modern web environments.
1. SQL Injection (SQLi) via API
SQL Injection remains one of the most prevalent threats. In the context of an API, this often happens when a RESTful endpoint uses a GET parameter to filter database results.
Vulnerable Code Example (Node.js/Express):
app.get('/api/users', (req, res) => {
const userId = req.query.id;
const query = "SELECT * FROM users WHERE id = " + userId;
db.execute(query, (err, results) => {
res.json(results);
});
});
In this example, the userId is concatenated directly into the SQL string. An attacker could send a request like:GET /api/users?id=1 OR 1=1
The resulting query becomes SELECT * FROM users WHERE id = 1 OR 1=1, which returns every user in the database, bypassing any intended access controls.
2. NoSQL Injection
With the rise of document-based databases like MongoDB, NoSQL injection has become a major concern. Unlike SQLi, which manipulates string syntax, NoSQL injection often involves manipulating JSON objects to alter query logic.
Vulnerable API Payload:
Consider an API endpoint for authentication that expects:
{ "username": "admin", "password": "secret" }
An attacker can use MongoDB query operators like $gt (greater than) to bypass authentication:
{ "username": "admin", "password": { "$gt": "" } }
If the API does not validate that the password field is a string, the database will look for a user where the username is "admin" and the password is greater than an empty string—which is true for almost any password, effectively logging the attacker in as the administrator.
3. OS Command Injection
Command injection occurs when an API passes user input to a system shell. This is often found in APIs that perform utility functions, such as image processing, network diagnostics, or file conversions.
Example Scenario:
An API endpoint allows users to check the latency of a remote server:POST /api/utils/ping
Payload: { "host": "8.8.8.8" }
If the backend executes exec("ping -c 4 " + body.host), an attacker can send:{ "host": "8.8.8.8; cat /etc/passwd" }
The semicolon terminates the ping command and starts a new one, allowing the attacker to read sensitive system files and potentially gain full remote code execution (RCE).
4. GraphQL Injection
GraphQL APIs are often perceived as more secure, but they introduce unique injection risks. Attackers can use "Alias" or "Circular Fragments" to cause Denial of Service (DoS) or use poorly implemented resolvers to perform unauthorized data extraction.
Because GraphQL allows users to define the shape of the response, an attacker can craft a complex query that forces the server to perform massive joins or recursive lookups, exhausting CPU and memory resources.
Why Modern APIs are Prime Targets
Several factors make APIs particularly vulnerable to injection compared to traditional web applications:
- Headless Nature: APIs are designed for machine-to-machine communication, often leading developers to assume that only "trusted" clients will interact with them. This leads to a lack of robust input validation.
- Complex Data Structures: Modern APIs handle nested JSON and XML, which are harder to sanitize than simple form fields. Each nested layer provides a new potential injection point.
- Expanded Attack Surface: A single web application might be backed by dozens of microservices, each with its own API. If even one microservice is vulnerable, the entire ecosystem may be at risk.
- Inadequate Tooling: Traditional vulnerability scanners often struggle to map API endpoints correctly, especially those requiring complex authentication or specific state sequences.
Real-World Impact of Successful Injection
The consequences of an API injection attack can be devastating for an organization:
- Data Exfiltration: Sensitive customer data, intellectual property, and financial records can be stolen in bulk.
- Account Takeover: By injecting logic into authentication or password reset APIs, attackers can gain control of user accounts.
- Service Disruption: Command injection or resource-heavy GraphQL queries can take down critical services, leading to downtime and loss of revenue.
- Compliance Violations: Breaches resulting from injection often lead to heavy fines under regulations like GDPR, HIPAA, or PCI-DSS.
How to Detect API Injection Vulnerabilities
Detecting these flaws requires a combination of automated scanning and manual testing.
Fuzzing and Dynamic Analysis
Security researchers use "fuzzing" to send unexpected characters (like ', ", ;, {{, and $) to API parameters. If the API returns a database error or a change in response time (Time-based SQLi), it indicates a potential vulnerability.
Reconnaissance is Key
You cannot protect what you do not know exists. Attackers often look for "Shadow APIs"—undocumented endpoints that lack the security controls of the main production API. Using Jsmon allows organizations to continuously discover their external attack surface, ensuring that every endpoint is accounted for and monitored for changes that could introduce injection risks.
Prevention and Mitigation Best Practices
Securing APIs against injection requires a defense-in-depth approach. Relying on a single security measure is rarely enough.
1. Use Parameterized Queries (Prepared Statements)
This is the most effective defense against SQLi. By using prepared statements, the database is told exactly what the query structure is beforehand, ensuring that user input is treated strictly as data and never as executable code.
2. Implement Strict Input Validation
Never trust user input. Use a "whitelist" approach where only expected characters and formats are allowed. For example, if an API expects a UUID, validate the input against a regex for UUIDs. If it expects a number, ensure the data type is an integer before processing it.
3. Use Safe APIs and Libraries
Avoid using functions that invoke the system shell (like eval() in JavaScript or os.system() in Python). Use built-in library functions that handle data safely. For example, instead of using a shell command to resize an image, use a native library like Sharp or Pillow.
4. Implement the Principle of Least Privilege
The database user or service account used by the API should only have the minimum permissions necessary. An API that only needs to read user profiles should not have permission to drop tables or access the system configuration.
5. Deploy a Web Application Firewall (WAF)
A modern WAF can identify and block common injection patterns in real-time. While not a replacement for secure coding, it provides a crucial layer of protection against known exploit payloads.
Conclusion
API injection remains a top threat in the OWASP API Security Top 10 for a reason: it is relatively easy to execute and offers high rewards for attackers. As organizations continue to migrate toward microservices and cloud-native architectures, the importance of securing these communication channels cannot be overstated. By implementing rigorous input validation, using prepared statements, and maintaining constant visibility over your infrastructure, you can significantly reduce your risk profile.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



