cybersecurity
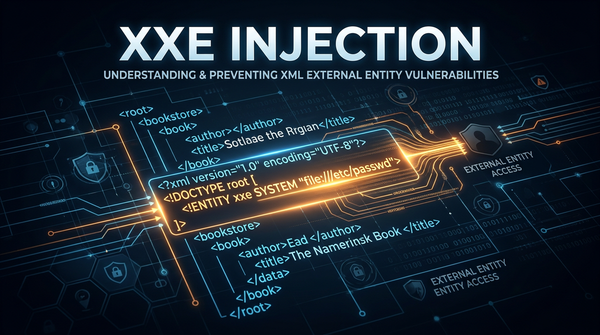
What is XML External Entity (XXE) Injection? Ways to Exploit, Examples and Impact
Learn what XXE injection is, how to exploit it with payloads, and how to prevent it. A comprehensive guide for cybersecurity beginners and professionals.
cybersecurity
Learn what XXE injection is, how to exploit it with payloads, and how to prevent it. A comprehensive guide for cybersecurity beginners and professionals.

403 bypass
Learn how BLE spoofing works, technical exploit methods, and real-world impacts on IoT security. Discover how to protect your organization's attack surface.
api security
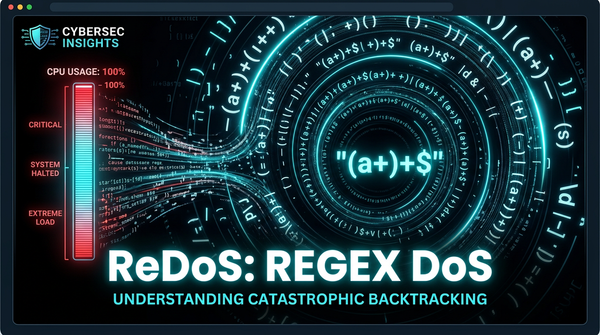
Discover how ReDoS attacks exploit catastrophic backtracking in regex engines. Learn to identify, exploit, and prevent ReDoS with practical examples.