cybersecurity
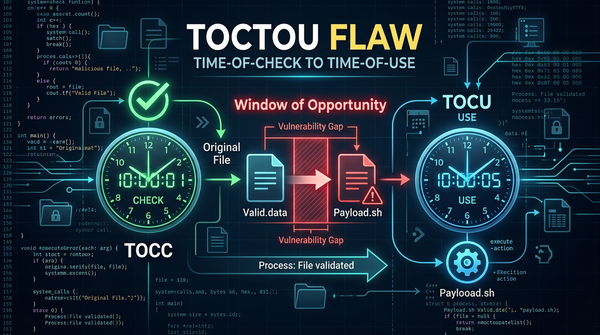
What is Time-of-Check to Time-of-Use (TOCTOU) Flaw? Ways to Exploit, Examples and Impact
Discover how Time-of-Check to Time-of-Use (TOCTOU) flaws create race conditions. Learn to identify, exploit, and mitigate these vulnerabilities in your code.