cybersecurity
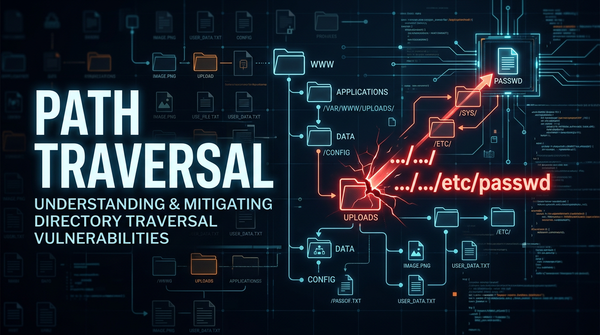
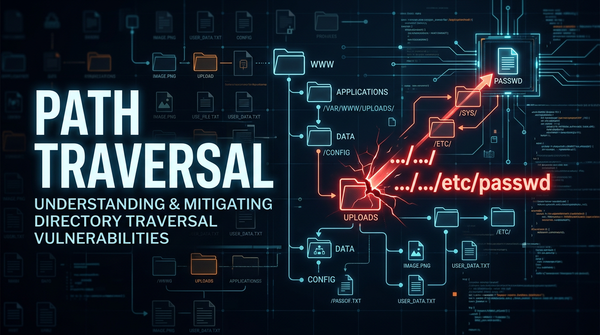
What is Path Traversal (Directory Traversal)? Ways to Exploit, Examples and Impact
Discover how Path Traversal vulnerabilities work, see real-world exploitation examples, and learn best practices for prevention and mitigation.
cybersecurity
Discover how Path Traversal vulnerabilities work, see real-world exploitation examples, and learn best practices for prevention and mitigation.

403 bypass
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.
403 bypass
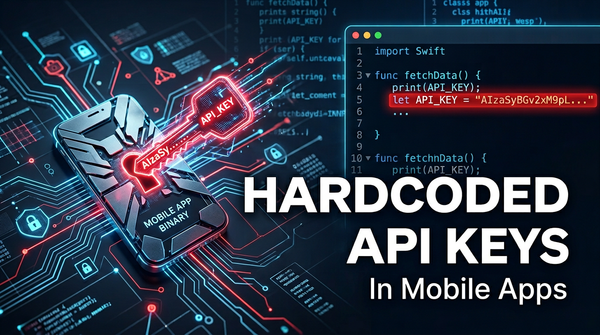
Discover the dangers of hardcoded API keys in mobile apps. Learn how attackers exploit them and how to secure your infrastructure with Jsmon.
403 bypass
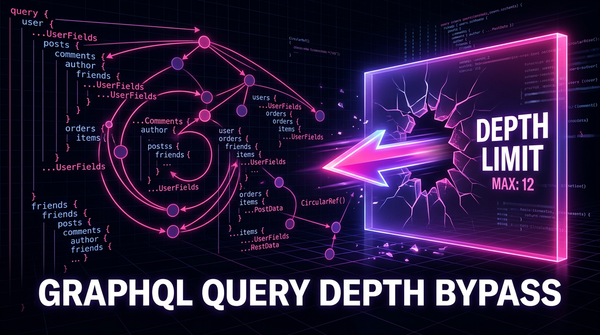
Learn how to identify and exploit GraphQL Query Depth Limit Bypasses. Discover technical payloads, mitigation strategies, and how to protect your APIs.
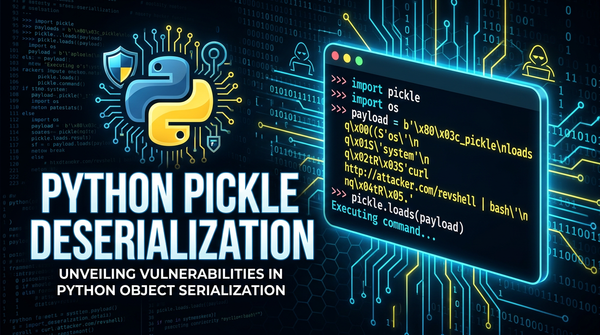
python
Discover how Python Pickle deserialization causes RCE. Learn exploit methods like __reduce__ and see real-world examples to secure your Python code.