api security
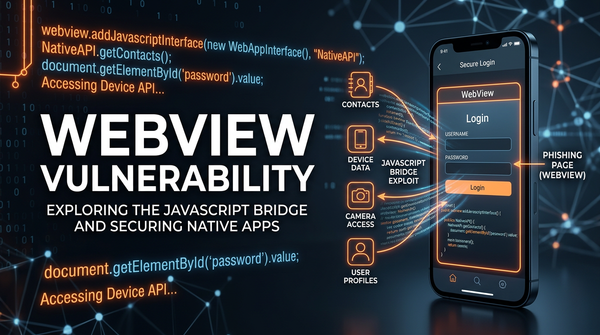
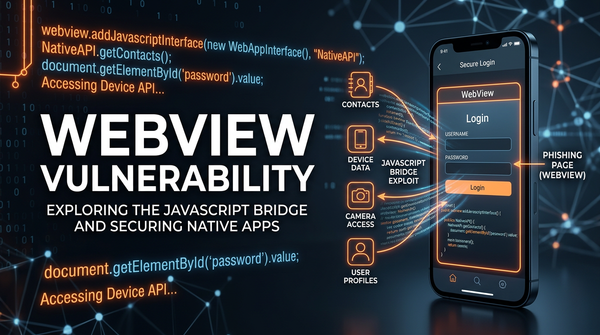
What is WebView Vulnerability? Ways to Exploit, Examples and Impact
Learn how WebView vulnerabilities like JS Bridge injection and file access work. Explore technical examples, security risks, and mitigation tips for mobile apps.
api security
Learn how WebView vulnerabilities like JS Bridge injection and file access work. Explore technical examples, security risks, and mitigation tips for mobile apps.
403 bypass
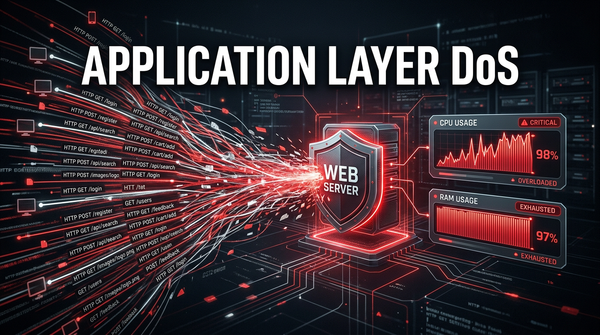
Learn how Application Layer DoS attacks work, explore common exploitation techniques like Slowloris, and discover how to mitigate Layer 7 threats effectively.

403 bypass
Learn how BLE spoofing works, technical exploit methods, and real-world impacts on IoT security. Discover how to protect your organization's attack surface.
403 bypass
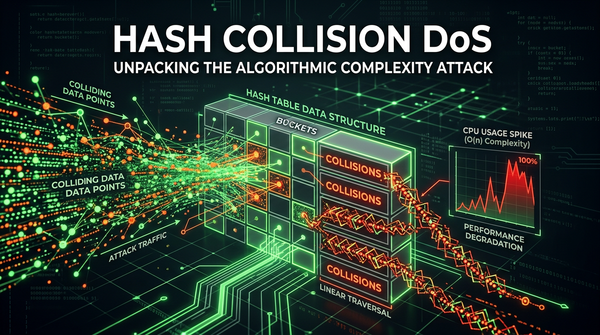
Learn how Hash Collision DoS attacks work, their technical impact on web applications, and how to prevent algorithmic complexity vulnerabilities.

apache
Learn how Apache Struts vulnerabilities like OGNL injection work. Explore technical exploit examples, RCE impact, and essential remediation steps for security.
cybersecurity
Learn common MFA bypass techniques like session hijacking and AiTM phishing. Explore technical examples and prevention tips to secure your attack surface.