
cybersecurity
What is Local File Inclusion (LFI)? Ways to Exploit, Examples and Impact
Explore Local File Inclusion (LFI) mechanics, exploitation techniques like path traversal, and practical mitigation strategies for developers.

cybersecurity
Explore Local File Inclusion (LFI) mechanics, exploitation techniques like path traversal, and practical mitigation strategies for developers.
403 bypass
Learn how the XML Bomb (Billion Laughs) attack works, explore exploitation examples, and find technical ways to prevent this resource exhaustion vulnerability.
403 bypass
Learn how Application Layer DoS attacks work, explore common exploitation techniques like Slowloris, and discover how to mitigate Layer 7 threats effectively.
403 bypass
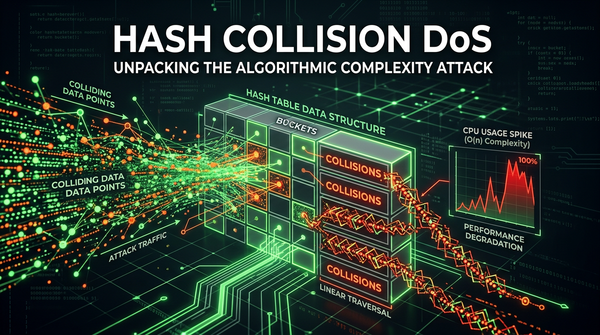
Learn how Hash Collision DoS attacks work, their technical impact on web applications, and how to prevent algorithmic complexity vulnerabilities.