cybersecurity
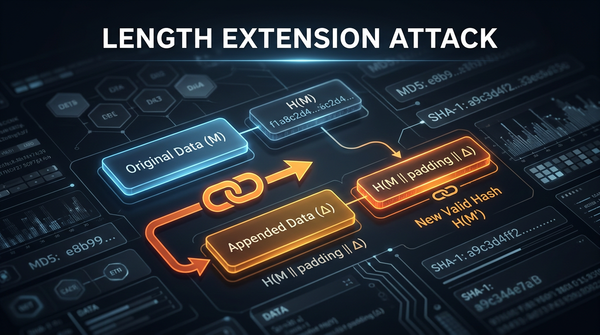
What is Length Extension Attack? Ways to Exploit, Examples and Impact
In the realm of cryptography, hash functions are often viewed as digital signatures that provide data integrity. However, many developers unknowingly implement hashing in a way that leaves their applications wide open to a sophisticated yet often overlooked technique called a Length Extension Attack. If you have ever used a