
403 bypass
What is Insecure Data Storage in Mobile? Ways to Exploit, Examples and Impact
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.

403 bypass
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.
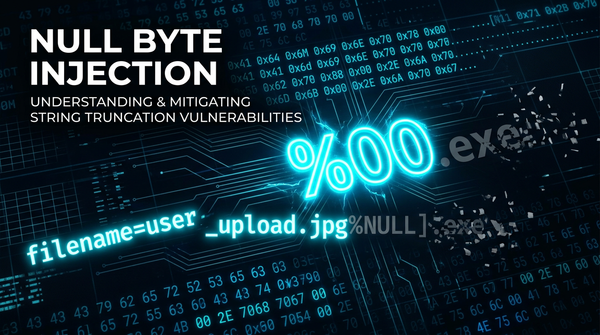
nullByte
Learn how Null Byte Injection exploits file upload vulnerabilities. Discover technical examples, bypass techniques, and how to secure your infrastructure.
second order domain takeover
Second-order domain takeovers target forgotten domains still referenced in live JavaScript files. This overlooked threat can lead to serious security risks. Learn how to detect them manually—or automate the entire process with jsmon.sh.
katana
When mapping out the attack surface of an application, JS files often contain a wealth of valuable information, API endpoints, keys, hidden paths, and more. One powerful tool that helps automate the discovery of these files is Katana, a fast and extensible web crawling framework by ProjectDiscovery.
bugbounty
When performing reconnaissance or source code reviews, JavaScript files are a goldmine of leaked credentials, secrets, tokens, and other sensitive artifacts. This blog post is a curated resource library of 100 regex patterns designed to help security researchers and engineers.
bugbounty
APIs are the backbone of modern applications, but they often leak sensitive information through JavaScript files, misconfigurations, and weak security measures. This checklist focuses on API hacking techniques, with special attention to JavaScript file analysis.
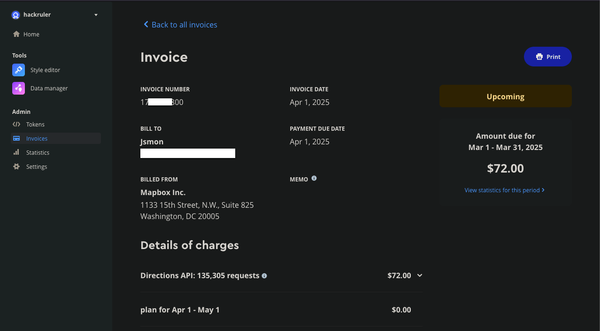
bug bounty
Mapbox is a powerful mapping platform that offers customizable maps, geocoding, and location-based services through its APIs and SDKs. However, when API tokens lack proper URL restrictions, they become a prime target for abuse. In this research, we