
403 bypass
What is Insecure Data Storage in Mobile? Ways to Exploit, Examples and Impact
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.

403 bypass
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.
403 bypass
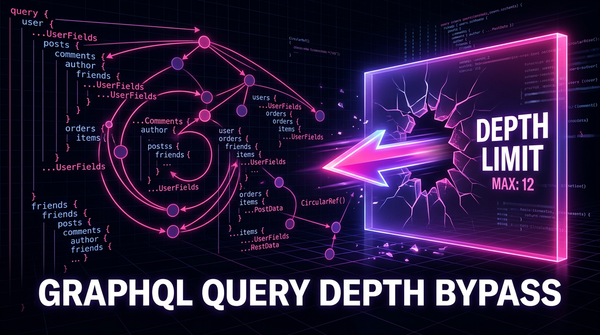
Learn how to identify and exploit GraphQL Query Depth Limit Bypasses. Discover technical payloads, mitigation strategies, and how to protect your APIs.
bug bounty
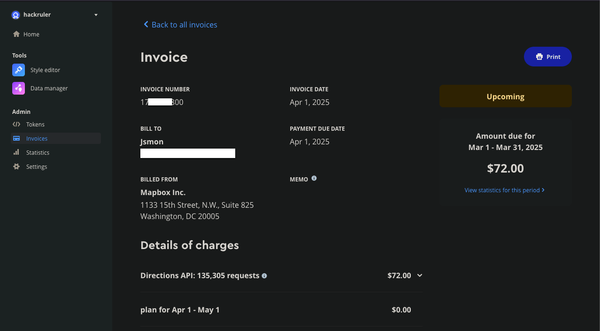
Mapbox is a powerful mapping platform that offers customizable maps, geocoding, and location-based services through its APIs and SDKs. However, when API tokens lack proper URL restrictions, they become a prime target for abuse. In this research, we

jsmon.sh
I was sitting on the last day of the H1702 Epic Games event. I've submitted a few bugs to Epic Games and it was the last day, I was not getting any idea on what else to submit. I decided to use my own product jsmon.sh. Collecting