
403 bypass
What is Insecure Data Storage in Mobile? Ways to Exploit, Examples and Impact
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.

403 bypass
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.
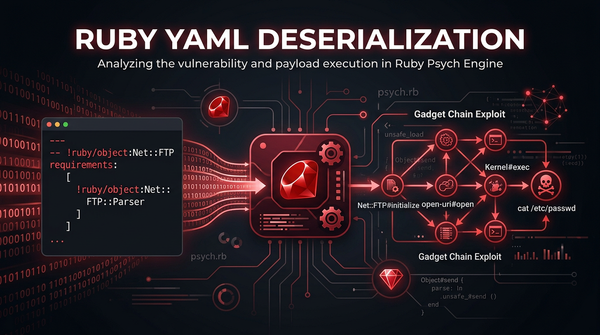
YAML Deserialization
Master Ruby YAML deserialization security. Explore technical exploit examples, gadget chains, and actionable mitigation strategies to protect your apps.
bugbounty
When performing reconnaissance or source code reviews, JavaScript files are a goldmine of leaked credentials, secrets, tokens, and other sensitive artifacts. This blog post is a curated resource library of 100 regex patterns designed to help security researchers and engineers.
bugbounty
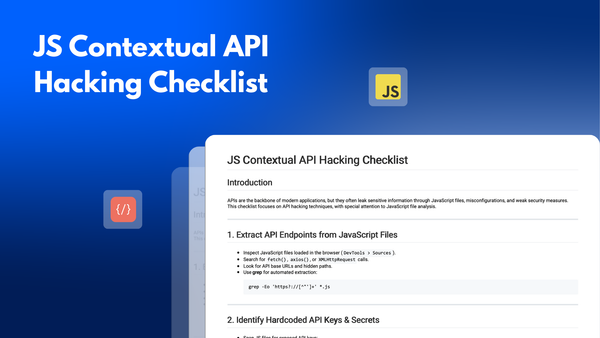
APIs are the backbone of modern applications, but they often leak sensitive information through JavaScript files, misconfigurations, and weak security measures. This checklist focuses on API hacking techniques, with special attention to JavaScript file analysis.
bugbounty
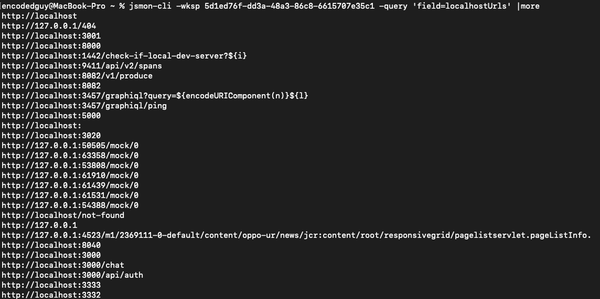
jsmon-cli is a fast and convenient tool (API client) for your JS hacking powered by jsmon.sh. jsmon.sh is a JS security framework made for security enthusiasts, bugbounty hunters, penetration testers