api security
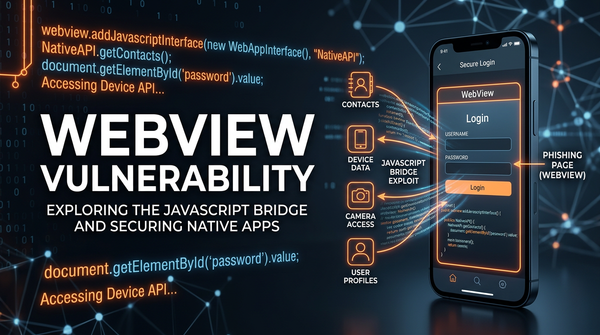
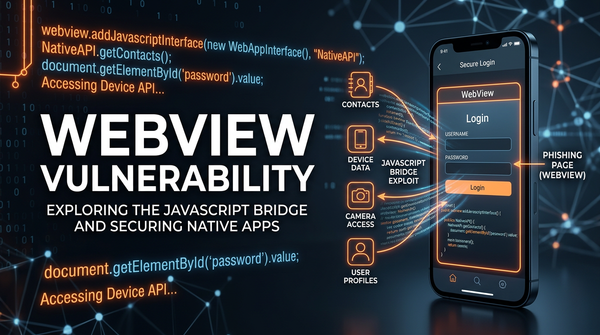
What is WebView Vulnerability? Ways to Exploit, Examples and Impact
Learn how WebView vulnerabilities like JS Bridge injection and file access work. Explore technical examples, security risks, and mitigation tips for mobile apps.
api security
Learn how WebView vulnerabilities like JS Bridge injection and file access work. Explore technical examples, security risks, and mitigation tips for mobile apps.
api security
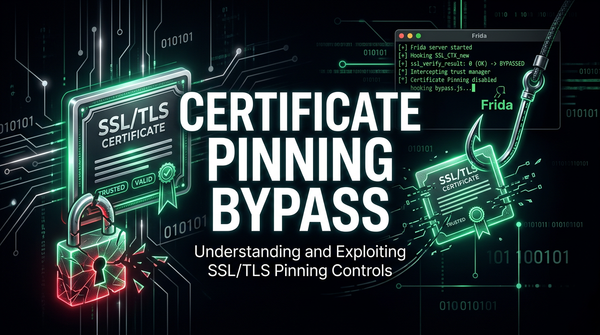
Discover how certificate pinning bypass works, common exploitation tools like Frida, and the impact of broken SSL pinning on mobile application security.
403 bypass
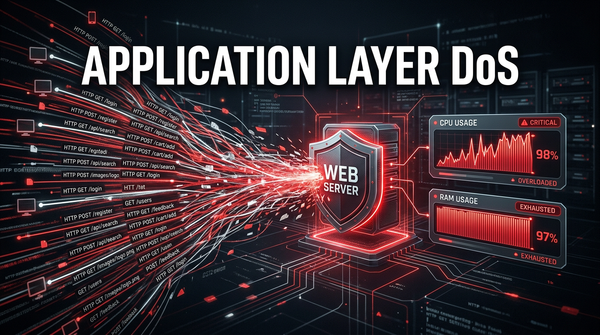
Learn how Application Layer DoS attacks work, explore common exploitation techniques like Slowloris, and discover how to mitigate Layer 7 threats effectively.

cybersecurity
Discover how insecure password reset mechanisms work, common exploitation methods like Host Header Injection, and technical mitigation strategies.