cybersecurity
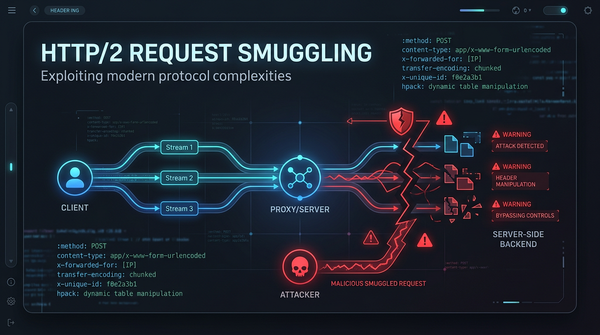
What is HTTP/2 Request Smuggling? Ways to Exploit, Examples and Impact
As the web evolved, the limitations of the aging HTTP/1.1 protocol became apparent. To address latency and performance issues, HTTP/2 was introduced, bringing features like binary framing, multiplexing, and header compression. However, with new features come new security challenges. HTTP/2 Request Smuggling has emerged as a