cybersecurity
What is JSON Hijacking? Ways to Exploit, Examples and Impact
Discover how JSON Hijacking works, explore real-world exploit examples, and learn how to secure your APIs against this data theft technique.
cybersecurity
Discover how JSON Hijacking works, explore real-world exploit examples, and learn how to secure your APIs against this data theft technique.
cybersecurity
In the world of concurrent programming, timing is everything. A race condition occurs when the behavior of a software system depends on the sequence or timing of uncontrollable events, such as the exact moment a process is scheduled by the operating system. When these timing issues involve the file system,

cybersecurity
In the high-stakes world of exploit development, attackers are constantly seeking ways to make their payloads more reliable. One of the most historically significant and technically fascinating techniques used to achieve this is known as heap spraying. While it is not a vulnerability in itself, heap spraying is a powerful
cybersecurity
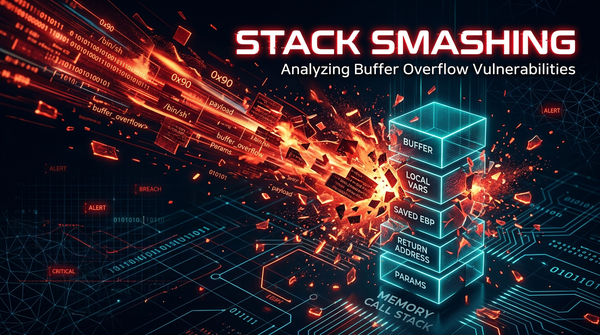
Stack smashing remains one of the most foundational concepts in software security and exploit development. Despite decades of research and the implementation of numerous hardware and software defenses, buffer overflows that lead to stack smashing continue to surface in modern applications, particularly those written in low-level languages like C and
cybersecurity
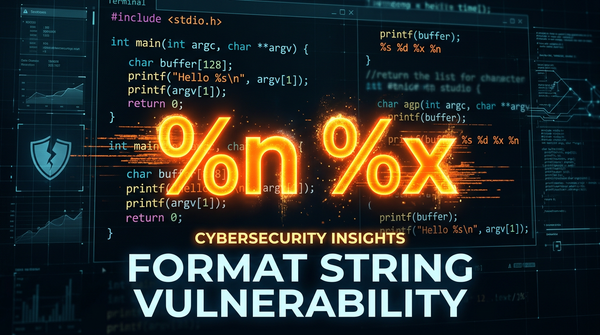
Memory corruption vulnerabilities have long been the cornerstone of low-level exploitation. Among these, the format string vulnerability stands out as a classic yet devastating class of bug that occurs when an application improperly filters user input passed into functions like printf(). In this guide, we will explore the mechanics of

cybersecurity
In the realm of cybersecurity, few vulnerabilities have stood the test of time as prominently as the buffer overflow. Despite being one of the oldest known software flaws, it remains a critical threat to modern infrastructure, often leading to full system compromise. A buffer overflow occurs when a program attempts
ethical hacking
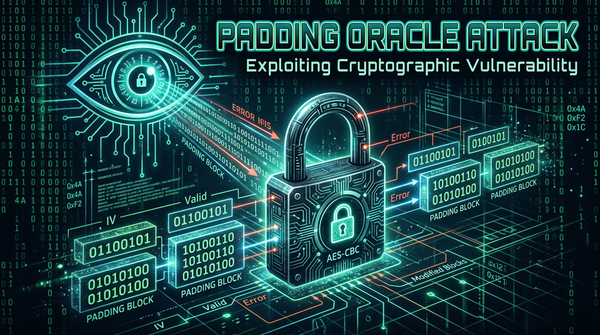
Cryptography is the bedrock of modern digital security, ensuring that sensitive data remains confidential even if intercepted by unauthorized parties. However, the implementation of cryptographic standards is often where vulnerabilities emerge. One of the most classic and devastating examples of implementation flaws is the Padding Oracle Attack. This side-channel attack

cybersecurity
Electron has revolutionized desktop application development by allowing developers to build cross-platform apps using web technologies like HTML, CSS, and JavaScript. However, this convenience comes with a unique set of security challenges. In this post, we will explore what Electron security misconfigurations are, how they can be exploited by attackers
ethical hacking
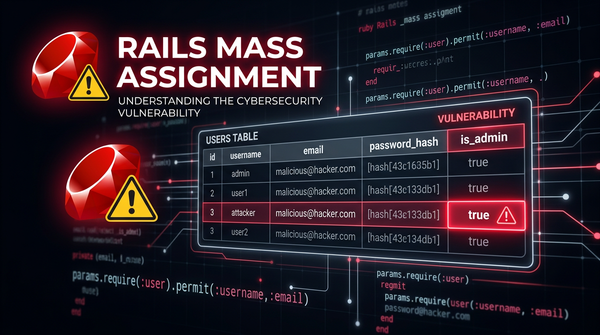
Ruby on Rails is a powerful web framework known for its "convention over configuration" philosophy, which allows developers to build complex applications rapidly. However, this same convenience can sometimes introduce significant security risks if not handled carefully. One of the most famous vulnerabilities in the Rails ecosystem is
ethical hacking
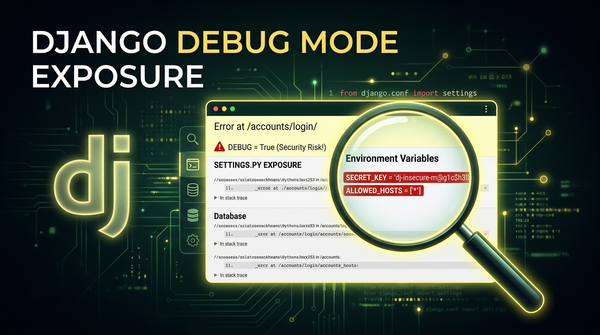
When a developer builds a web application using the Django framework, one of the most useful tools at their disposal is the built-in debug mode. It provides detailed error reports, stack traces, and local variable states that make troubleshooting a breeze. However, if this feature is accidentally left active in

ethical hacking
In the world of cybersecurity, legacy protocols are often the weakest link in an organization's defense. The POODLE attack, which stands for Padding Oracle On Downgraded Legacy Encryption, is a classic example of how an old, supposedly secure protocol can be manipulated to leak sensitive information. Discovered in

cybersecurity
In 2014, the cybersecurity world was rocked by the discovery of a critical flaw in OpenSSL, one of the most widely used encryption libraries on the internet. Known as Heartbleed (CVE-2014-0160), this vulnerability allowed attackers to read sensitive data from the memory of affected servers without leaving a trace. Understanding