
cybersecurity
What is Blind SSRF? Ways to Exploit, Examples and Impact
Learn how Blind SSRF works, how to detect it using OAST, and ways to prevent this critical vulnerability from exposing your internal network.

cybersecurity
Learn how Blind SSRF works, how to detect it using OAST, and ways to prevent this critical vulnerability from exposing your internal network.

cybersecurity
Discover how Firebase database misconfigurations lead to data leaks. Learn to identify insecure rules, exploit scenarios, and prevention tips.
cybersecurity
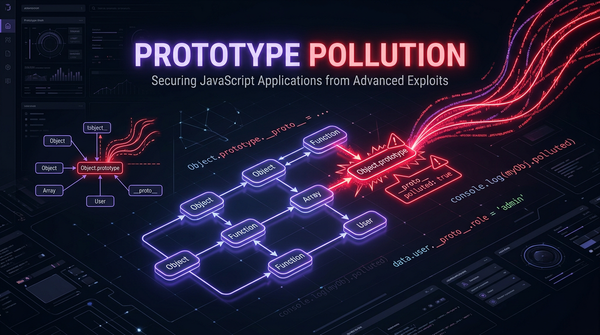
JavaScript is a language built on the foundation of prototypes. While this provides incredible flexibility and efficiency in memory management, it also introduces a unique class of vulnerabilities known as Prototype Pollution. This vulnerability becomes particularly dangerous when combined with "gadgets"—pre-existing code snippets within an application that,

cybersecurity
Master Server-Side Request Forgery (SSRF). Learn how attackers bypass filters, access cloud metadata, and secure your infrastructure against SSRF attacks.
cybersecurity
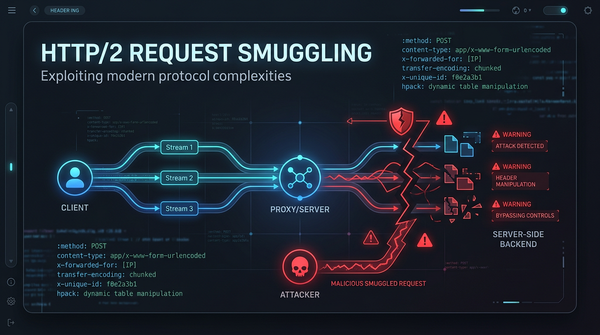
As the web evolved, the limitations of the aging HTTP/1.1 protocol became apparent. To address latency and performance issues, HTTP/2 was introduced, bringing features like binary framing, multiplexing, and header compression. However, with new features come new security challenges. HTTP/2 Request Smuggling has emerged as a
cybersecurity
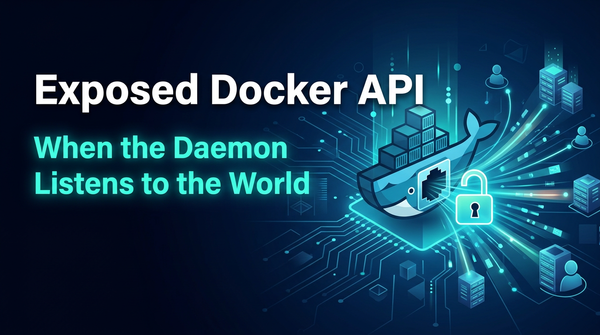
Learn how exposed Docker APIs lead to host compromise. Explore exploitation examples, RCE techniques, and security best practices to protect your servers.
ethical hacking
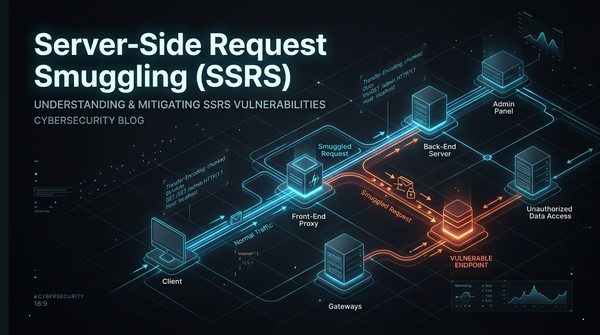
In the modern landscape of web architecture, applications are rarely standalone entities. They typically sit behind a chain of servers, including load balancers, reverse proxies, and content delivery networks (CDNs). While this multi-tiered approach improves performance and scalability, it introduces a dangerous class of vulnerability known as Server-Side Request Smuggling
cybersecurity
Internet Message Access Protocol (IMAP) is a foundational technology that allows email clients to communicate with mail servers. While it has been around for decades, it remains a critical part of our digital infrastructure. However, like many protocols that rely on text-based commands, it is susceptible to a specific class

cybersecurity
Docker has revolutionized the way we develop, ship, and run applications by providing a lightweight, portable environment called a container. However, the very nature of containers—sharing the host machine's OS kernel—introduces unique security challenges. A Docker container breakout, also known as a container escape, occurs when
cybersecurity
Explore common Kubernetes misconfigurations, technical exploit examples, and how to protect your infrastructure. Learn to secure your K8s clusters today.
cybersecurity
Understand Cross-Site Request Forgery (CSRF) with technical examples and payloads. Learn how to defend your web applications using modern security practices.

cybersecurity
Explore AWS IAM privilege escalation techniques, payloads, and impacts. Learn how to secure your AWS environment against identity-based attacks.