
cybersecurity
What is Local File Inclusion (LFI)? Ways to Exploit, Examples and Impact
Explore Local File Inclusion (LFI) mechanics, exploitation techniques like path traversal, and practical mitigation strategies for developers.

cybersecurity
Explore Local File Inclusion (LFI) mechanics, exploitation techniques like path traversal, and practical mitigation strategies for developers.

cybersecurity
Digital advertising is a multi-billion dollar industry, but where there is massive cash flow, there is inevitable exploitation. Ad fraud traffic refers to the practice of deceiving advertisers into paying for fake interactions, such as clicks, impressions, or app installs that never actually occurred or were generated by non-human actors.
exposed jenkins instance
Learn how exposed Jenkins instances lead to full system compromise. Explore exploitation techniques and security best practices for your CI/CD pipeline.
cybersecurity
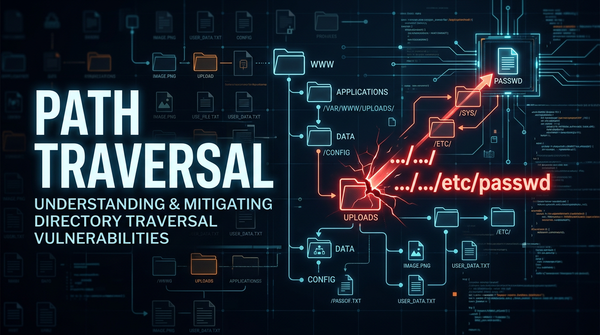
Discover how Path Traversal vulnerabilities work, see real-world exploitation examples, and learn best practices for prevention and mitigation.

cybersecurity
Digital advertising is the lifeblood of the modern internet, providing the revenue necessary for creators and platforms to offer free services. However, where there is money, there is inevitably fraud. One of the most persistent and costly threats in the cybersecurity landscape today is click fraud, largely driven by sophisticated

backup file exposure
Learn how backup file exposure leads to source code leaks. Explore exploitation techniques, real-world examples, and prevention strategies for .bak files.

cybersecurity
Discover how insecure deserialization leads to RCE. Explore technical examples in PHP and Python, and learn how to secure your infrastructure today.

ds store file exposure
Learn how .DS_Store file exposure leads to information disclosure. Discover exploitation methods, tools, and how to prevent these leaks on your server.
cybersecurity
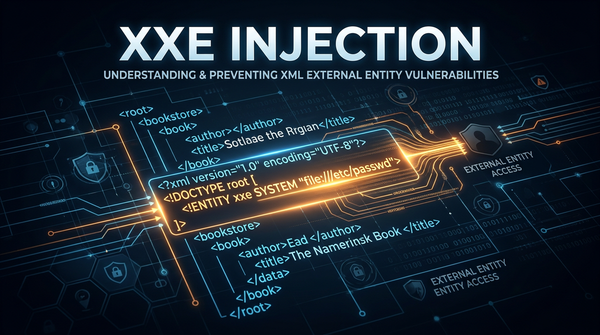
Learn what XXE injection is, how to exploit it with payloads, and how to prevent it. A comprehensive guide for cybersecurity beginners and professionals.
cybersecurity
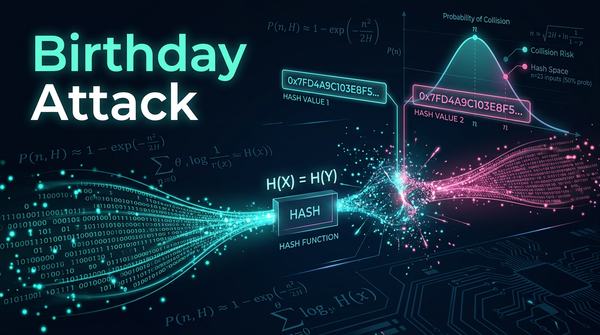
In the realm of cryptography, the security of digital communication often rests on the assumption that specific mathematical functions are impossible to reverse or duplicate. However, the Birthday Attack—a cryptographic phenomenon based on probability theory—proves that finding collisions in data is much easier than most people intuitively believe.

git directory exposure
Discover how exposed .git folders leak source code and secrets. Learn manual and automated exploitation methods and how to secure your web server today.
cybersecurity
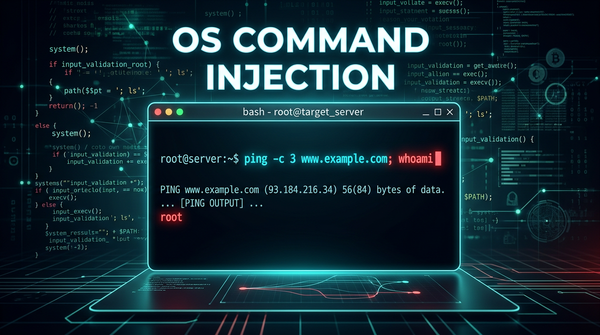
Master the fundamentals of OS Command Injection. Learn how attackers exploit shell vulnerabilities and how to secure your infrastructure with Jsmon.