403 bypass
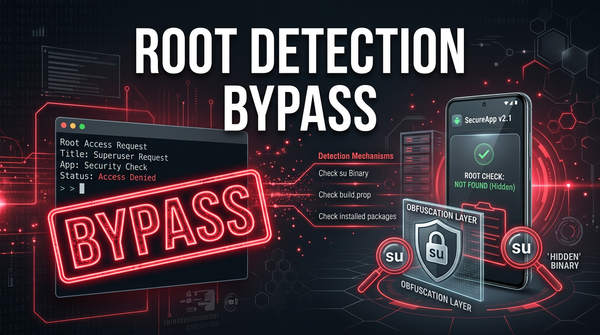
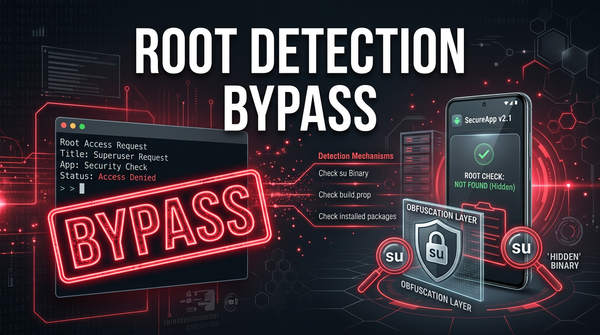
What is Root Detection Bypass? Ways to Exploit, Examples and Impact
Learn what root detection bypass is, how it works, and common exploitation methods like Frida and Smali patching in this technical cybersecurity guide.
403 bypass
Learn what root detection bypass is, how it works, and common exploitation methods like Frida and Smali patching in this technical cybersecurity guide.
dependency confusion
A Dependency Confusion attack, also known as a substitution attack, occurs when a malicious actor uploads a package with the same name as an internal or private dependency to a public package registry. If the development