ethical hacking
What is Referer Leakage? Ways to Exploit, Examples and Impact
Deep dive into Referer Leakage: technical exploitation examples, security impact, and how to use Referrer-Policy to prevent sensitive data exposure.
ethical hacking
Deep dive into Referer Leakage: technical exploitation examples, security impact, and how to use Referrer-Policy to prevent sensitive data exposure.
ethical hacking
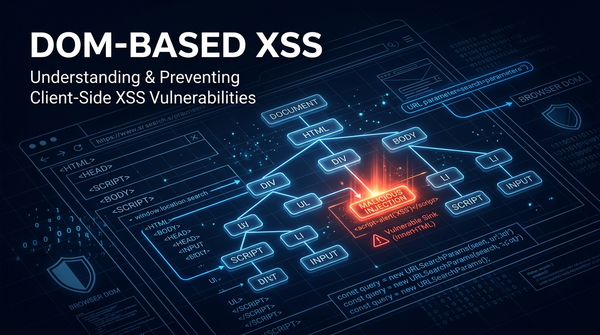
Learn how DOM-based XSS works, explore technical exploitation examples, and find actionable mitigation strategies to secure your client-side JavaScript.
cybersecurity
Discover the mechanics of DOM Clobbering. This guide covers exploitation techniques, real-world examples, and prevention strategies for security pros.

Cross-Site Scripting
Master Stored Cross-Site Scripting (XSS). Learn technical exploitation techniques, see real-world payloads, and discover how to secure your web applications.

cybersecurity
As artificial intelligence (AI) and Large Language Models (LLMs) become central to modern software ecosystems, a new frontier of cybersecurity threats has emerged. Among the most concerning is Training Data Extraction (TDE)—a class of attacks where an adversary queries a machine learning model to retrieve specific pieces of information
cybersecurity
Understand Reflected Cross-Site Scripting (XSS) with technical examples and payloads. Learn how to detect and mitigate XSS to secure your web applications.
cybersecurity
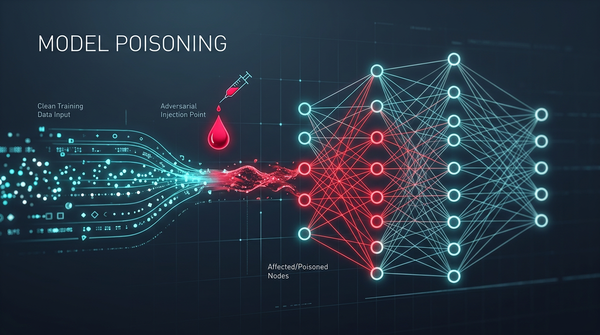
Artificial Intelligence (AI) and Machine Learning (ML) have transitioned from experimental laboratory projects to the backbone of modern enterprise infrastructure. From automated threat detection to financial forecasting, these models make critical decisions every second. However, as our reliance on AI grows, so does the incentive for attackers to subvert these
cybersecurity
Master Boolean-based Blind SQL Injection. Learn how attackers use logic to exfiltrate data and how to prevent it with prepared statements.
cybersecurity
As Large Language Models (LLMs) like GPT-4, Claude, and Llama become the backbone of modern AI applications, a new class of cybersecurity threats has emerged. Prompt Injection is arguably the most critical vulnerability in the AI space today, representing a fundamental shift in how we think about input validation. Unlike
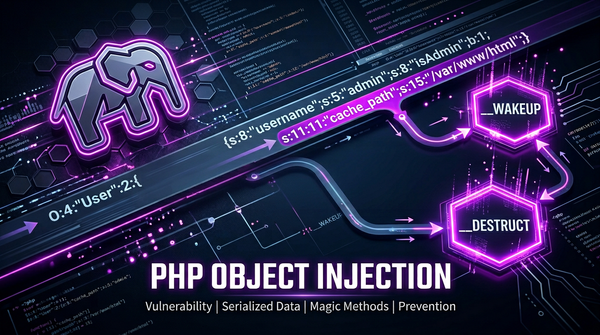
403 bypass
Learn how PHP Object Injection works, the danger of unserialize(), and how to prevent RCE and POP chains in your PHP applications.
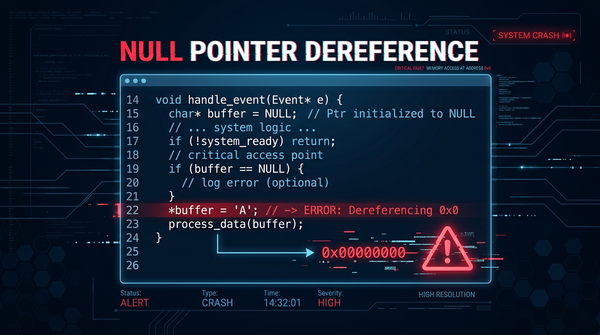
cybersecurity
Memory safety remains one of the most significant challenges in modern software development. Among the various types of memory-related vulnerabilities, the Null Pointer Dereference (CWE-476) is perhaps the most well-known and frequently encountered. While it often results in a simple application crash, in certain environments—particularly within operating system kernels

ethical hacking
Understand the risks of missing Secure cookie flags. Learn how attackers hijack sessions and how to prevent it with code examples and best practices.