403 bypass
What is XML Bomb (Billion Laughs Attack)? Ways to Exploit, Examples and Impact
Learn how the XML Bomb (Billion Laughs) attack works, explore exploitation examples, and find technical ways to prevent this resource exhaustion vulnerability.
403 bypass
Learn how the XML Bomb (Billion Laughs) attack works, explore exploitation examples, and find technical ways to prevent this resource exhaustion vulnerability.
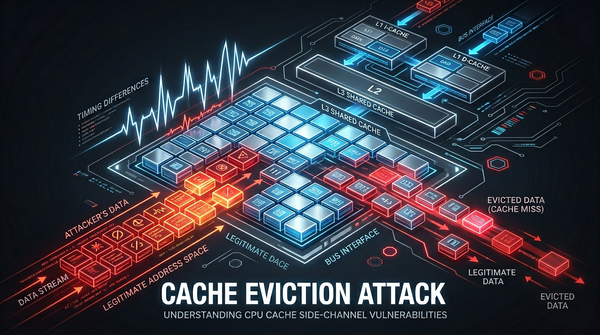
cache eviction
Discover how cache eviction attacks like Prime+Probe work. Learn to identify, exploit, and prevent these side-channel vulnerabilities in modern hardware.
cybersecurity
Understand Cross-Site Request Forgery (CSRF) with technical examples and payloads. Learn how to defend your web applications using modern security practices.
api security
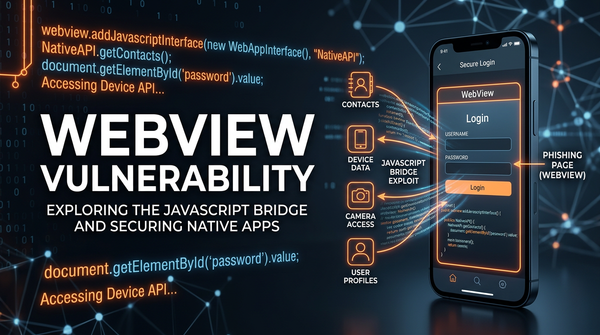
Learn how WebView vulnerabilities like JS Bridge injection and file access work. Explore technical examples, security risks, and mitigation tips for mobile apps.
api security
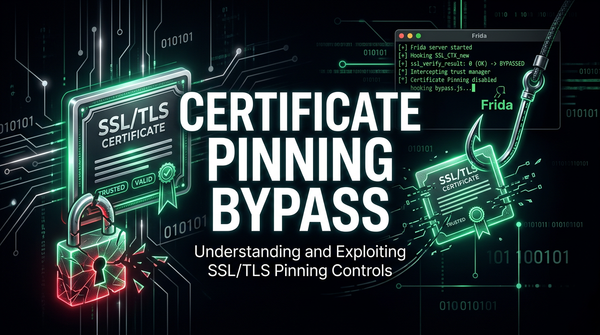
Discover how certificate pinning bypass works, common exploitation tools like Frida, and the impact of broken SSL pinning on mobile application security.
403 bypass
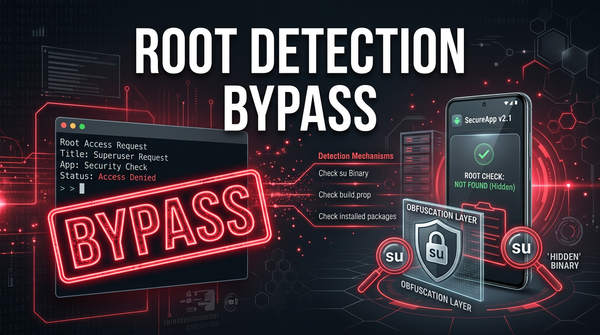
Learn what root detection bypass is, how it works, and common exploitation methods like Frida and Smali patching in this technical cybersecurity guide.
403 bypass
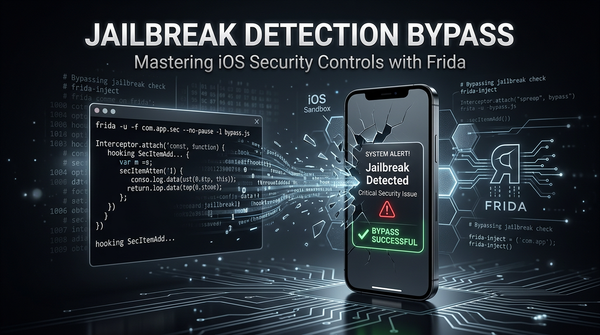
Discover how jailbreak detection bypass works. Explore technical exploit methods like Frida scripts and binary patching to secure your mobile apps.