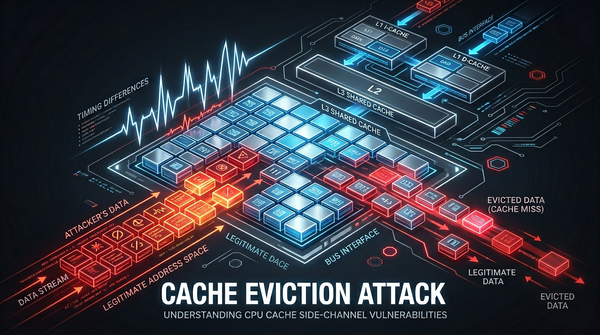
cache eviction
What is Cache Eviction Attack? Ways to Exploit, Examples and Impact
Discover how cache eviction attacks like Prime+Probe work. Learn to identify, exploit, and prevent these side-channel vulnerabilities in modern hardware.
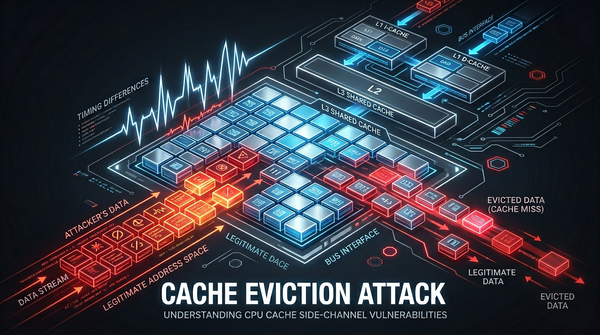
cache eviction
Discover how cache eviction attacks like Prime+Probe work. Learn to identify, exploit, and prevent these side-channel vulnerabilities in modern hardware.
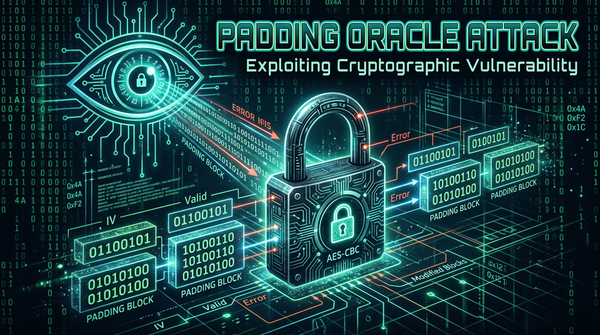
ethical hacking
Cryptography is the bedrock of modern digital security, ensuring that sensitive data remains confidential even if intercepted by unauthorized parties. However, the implementation of cryptographic standards is often where vulnerabilities emerge. One of the most classic and devastating examples of implementation flaws is the Padding Oracle Attack. This side-channel attack