api security
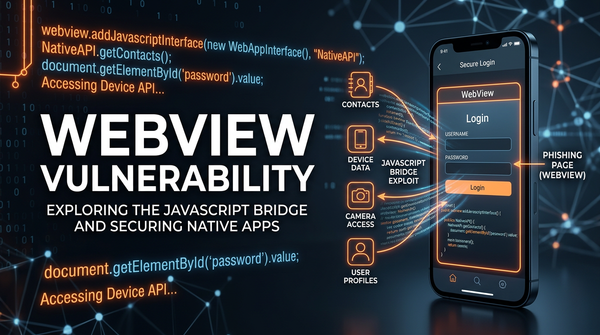
What is WebView Vulnerability? Ways to Exploit, Examples and Impact
Learn how WebView vulnerabilities like JS Bridge injection and file access work. Explore technical examples, security risks, and mitigation tips for mobile apps.
api security
Learn how WebView vulnerabilities like JS Bridge injection and file access work. Explore technical examples, security risks, and mitigation tips for mobile apps.
api security
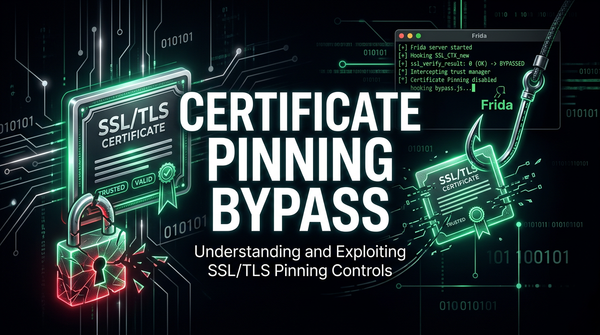
Discover how certificate pinning bypass works, common exploitation tools like Frida, and the impact of broken SSL pinning on mobile application security.

bug bounty
Amazon S3 bucket takeovers are a common and impactful vulnerability in web applications. When a JavaScript file references an S3 bucket that no longer exists (but is still expected to serve assets), attackers can claim ownership of that bucket and serve malicious content in its place.

bugbounty
When hunting for vulnerabilities or hidden endpoints in web applications, archived JavaScript files can be a goldmine. These scripts often contain forgotten or deprecated URLs, API endpoints, and internal services that might still be alive but are no longer linked from the main website. In this post, we’ll walk
bugbounty
When performing reconnaissance or source code reviews, JavaScript files are a goldmine of leaked credentials, secrets, tokens, and other sensitive artifacts. This blog post is a curated resource library of 100 regex patterns designed to help security researchers and engineers.