403 bypass
What is Jailbreak Detection Bypass? Ways to Exploit, Examples and Impact
Discover how jailbreak detection bypass works. Explore technical exploit methods like Frida scripts and binary patching to secure your mobile apps.
403 bypass
Discover how jailbreak detection bypass works. Explore technical exploit methods like Frida scripts and binary patching to secure your mobile apps.

bug bounty
Amazon S3 bucket takeovers are a common and impactful vulnerability in web applications. When a JavaScript file references an S3 bucket that no longer exists (but is still expected to serve assets), attackers can claim ownership of that bucket and serve malicious content in its place.
dependency confusion
A Dependency Confusion attack, also known as a substitution attack, occurs when a malicious actor uploads a package with the same name as an internal or private dependency to a public package registry. If the development

bugbounty
When hunting for vulnerabilities or hidden endpoints in web applications, archived JavaScript files can be a goldmine. These scripts often contain forgotten or deprecated URLs, API endpoints, and internal services that might still be alive but are no longer linked from the main website. In this post, we’ll walk
bugbounty
When performing reconnaissance or source code reviews, JavaScript files are a goldmine of leaked credentials, secrets, tokens, and other sensitive artifacts. This blog post is a curated resource library of 100 regex patterns designed to help security researchers and engineers.
bugbounty
APIs are the backbone of modern applications, but they often leak sensitive information through JavaScript files, misconfigurations, and weak security measures. This checklist focuses on API hacking techniques, with special attention to JavaScript file analysis.
bugbounty
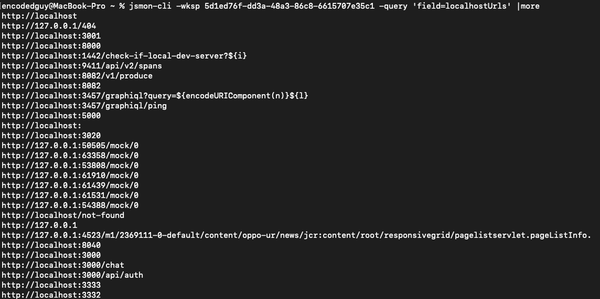
jsmon-cli is a fast and convenient tool (API client) for your JS hacking powered by jsmon.sh. jsmon.sh is a JS security framework made for security enthusiasts, bugbounty hunters, penetration testers
bug bounty
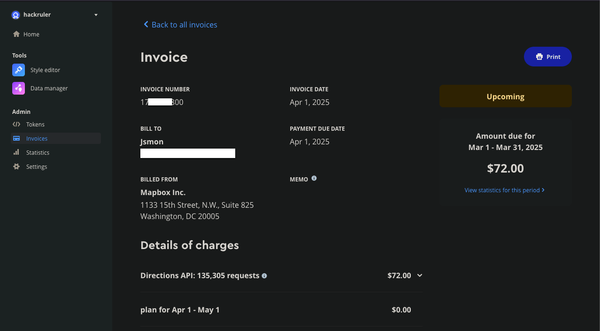
Mapbox is a powerful mapping platform that offers customizable maps, geocoding, and location-based services through its APIs and SDKs. However, when API tokens lack proper URL restrictions, they become a prime target for abuse. In this research, we

jsmon.sh
I was sitting on the last day of the H1702 Epic Games event. I've submitted a few bugs to Epic Games and it was the last day, I was not getting any idea on what else to submit. I decided to use my own product jsmon.sh. Collecting