
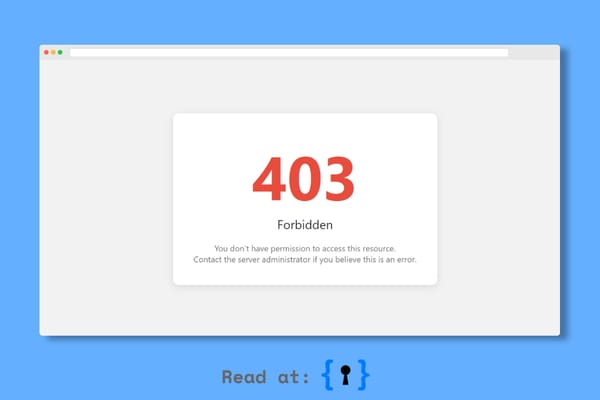
403 bypass
What is Intent Injection (Android)? Ways to Exploit, Examples and Impact
Learn what Intent Injection is in Android, how to exploit it with code examples, and how to secure your mobile applications against these vulnerabilities.

403 bypass
Learn what Intent Injection is in Android, how to exploit it with code examples, and how to secure your mobile applications against these vulnerabilities.

api security
Master the technical details of deeplink hijacking. Learn how attackers exploit mobile URI schemes and how to protect your app's data from exposure.
bug bounty
403 errors are crucial during bug hunting and penetration testing. When bypassed, they can reveal sensitive information that leads to substantial bounties. Understanding and bypassing these errors is essential for earning good bounties and avoiding duplicate submissions.