
403 bypass
What is Intent Injection (Android)? Ways to Exploit, Examples and Impact
Learn what Intent Injection is in Android, how to exploit it with code examples, and how to secure your mobile applications against these vulnerabilities.

403 bypass
Learn what Intent Injection is in Android, how to exploit it with code examples, and how to secure your mobile applications against these vulnerabilities.
403 bypass
Discover the dangers of hardcoded API keys in mobile apps. Learn how attackers exploit them and how to secure your infrastructure with Jsmon.
api security
Discover how certificate pinning bypass works, common exploitation tools like Frida, and the impact of broken SSL pinning on mobile application security.
403 bypass
Learn what root detection bypass is, how it works, and common exploitation methods like Frida and Smali patching in this technical cybersecurity guide.

403 bypass
Learn how BLE spoofing works, technical exploit methods, and real-world impacts on IoT security. Discover how to protect your organization's attack surface.
403 bypass
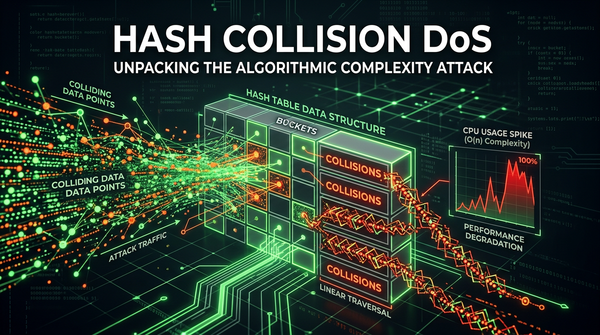
Learn how Hash Collision DoS attacks work, their technical impact on web applications, and how to prevent algorithmic complexity vulnerabilities.

403 bypass
Discover how Java deserialization leads to RCE. Learn to identify gadget chains, use ysoserial, and implement secure coding practices to protect your apps.
403 bypass
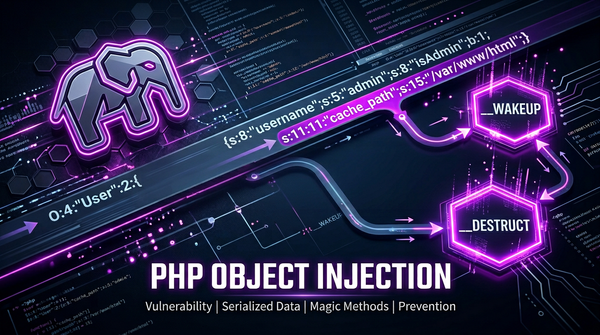
Learn how PHP Object Injection works, the danger of unserialize(), and how to prevent RCE and POP chains in your PHP applications.
bug bounty
403 errors are crucial during bug hunting and penetration testing. When bypassed, they can reveal sensitive information that leads to substantial bounties. Understanding and bypassing these errors is essential for earning good bounties and avoiding duplicate submissions.

bug bounty
Amazon S3 bucket takeovers are a common and impactful vulnerability in web applications. When a JavaScript file references an S3 bucket that no longer exists (but is still expected to serve assets), attackers can claim ownership of that bucket and serve malicious content in its place.
katana
When mapping out the attack surface of an application, JS files often contain a wealth of valuable information, API endpoints, keys, hidden paths, and more. One powerful tool that helps automate the discovery of these files is Katana, a fast and extensible web crawling framework by ProjectDiscovery.
bugbounty
When performing reconnaissance or source code reviews, JavaScript files are a goldmine of leaked credentials, secrets, tokens, and other sensitive artifacts. This blog post is a curated resource library of 100 regex patterns designed to help security researchers and engineers.