
403 bypass
What is a Side-Channel Attack? Ways to Exploit, Examples and Impact
Discover how side-channel attacks exploit physical leakage to steal data. Learn about timing attacks, power analysis, and mitigation strategies.

403 bypass
Discover how side-channel attacks exploit physical leakage to steal data. Learn about timing attacks, power analysis, and mitigation strategies.
403 bypass
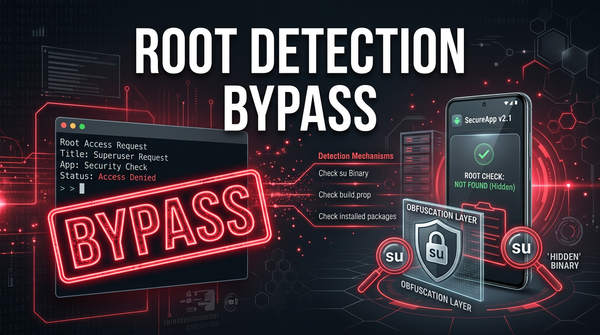
Learn what root detection bypass is, how it works, and common exploitation methods like Frida and Smali patching in this technical cybersecurity guide.
403 bypass
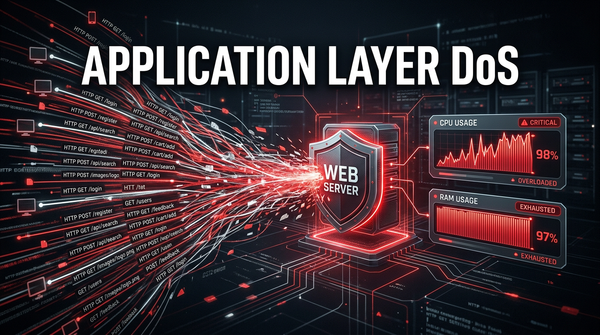
Learn how Application Layer DoS attacks work, explore common exploitation techniques like Slowloris, and discover how to mitigate Layer 7 threats effectively.
403 bypass
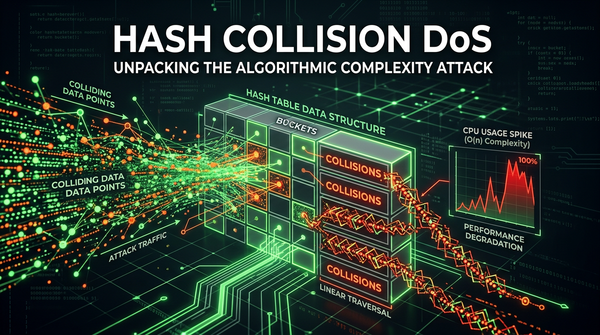
Learn how Hash Collision DoS attacks work, their technical impact on web applications, and how to prevent algorithmic complexity vulnerabilities.
403 bypass
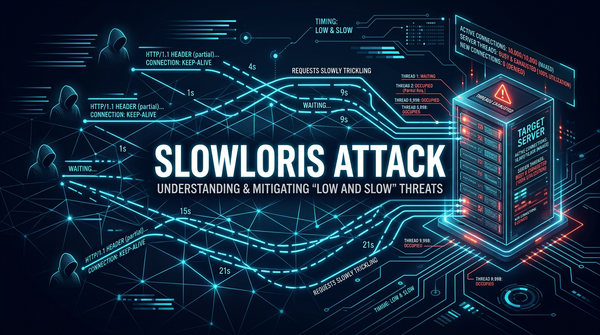
Learn how Slowloris attacks exploit web servers using low-bandwidth HTTP requests. Discover exploitation methods, real-world examples, and mitigation tips.

403 bypass
Discover how Java deserialization leads to RCE. Learn to identify gadget chains, use ysoserial, and implement secure coding practices to protect your apps.

apache
Learn how Apache Struts vulnerabilities like OGNL injection work. Explore technical exploit examples, RCE impact, and essential remediation steps for security.
403 bypass
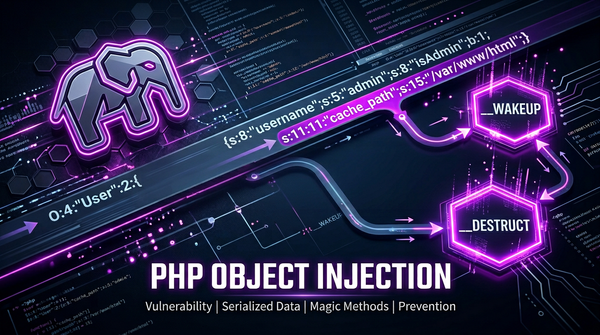
Learn how PHP Object Injection works, the danger of unserialize(), and how to prevent RCE and POP chains in your PHP applications.
python
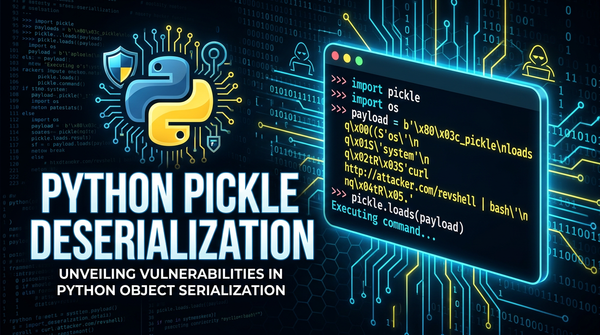
Discover how Python Pickle deserialization causes RCE. Learn exploit methods like __reduce__ and see real-world examples to secure your Python code.
bruteforce attack
Explore how brute force attacks exploit weak passwords. Learn about dictionary attacks, tools like Hydra, and how to prevent them with Jsmon.