
cybersecurity
What is Broken Access Control? Ways to Exploit, Examples and Impact
Explore Broken Access Control, IDOR, and privilege escalation. Learn how to exploit and prevent the #1 OWASP vulnerability with technical code examples.

cybersecurity
Explore Broken Access Control, IDOR, and privilege escalation. Learn how to exploit and prevent the #1 OWASP vulnerability with technical code examples.

apache
Learn how Apache Struts vulnerabilities like OGNL injection work. Explore technical exploit examples, RCE impact, and essential remediation steps for security.
403 bypass
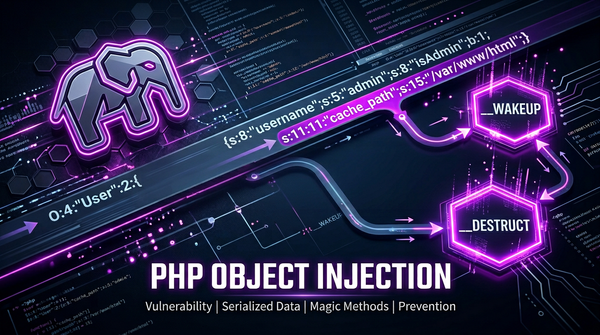
Learn how PHP Object Injection works, the danger of unserialize(), and how to prevent RCE and POP chains in your PHP applications.