cybersecurity
What is Birthday Attack? Ways to Exploit, Examples and Impact
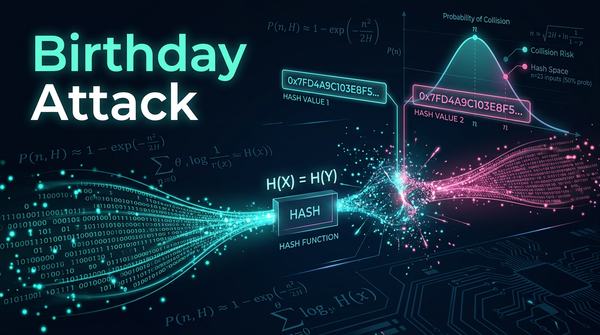
In the realm of cryptography, the security of digital communication often rests on the assumption that specific mathematical functions are impossible to reverse or duplicate. However, the Birthday Attack—a cryptographic phenomenon based on probability theory—proves that finding collisions in data is much easier than most people intuitively believe.