
403 bypass
What is a Side-Channel Attack? Ways to Exploit, Examples and Impact
Discover how side-channel attacks exploit physical leakage to steal data. Learn about timing attacks, power analysis, and mitigation strategies.

403 bypass
Discover how side-channel attacks exploit physical leakage to steal data. Learn about timing attacks, power analysis, and mitigation strategies.
403 bypass
Learn how the XML Bomb (Billion Laughs) attack works, explore exploitation examples, and find technical ways to prevent this resource exhaustion vulnerability.

403 bypass
Learn what Intent Injection is in Android, how to exploit it with code examples, and how to secure your mobile applications against these vulnerabilities.

403 bypass
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.

api security
Master the technical details of deeplink hijacking. Learn how attackers exploit mobile URI schemes and how to protect your app's data from exposure.
nullByte
Learn how Null Byte Injection exploits file upload vulnerabilities. Discover technical examples, bypass techniques, and how to secure your infrastructure.
403 bypass
Learn how Application Layer DoS attacks work, explore common exploitation techniques like Slowloris, and discover how to mitigate Layer 7 threats effectively.
403 bypass
Discover how jailbreak detection bypass works. Explore technical exploit methods like Frida scripts and binary patching to secure your mobile apps.

apache
Learn how Apache Struts vulnerabilities like OGNL injection work. Explore technical exploit examples, RCE impact, and essential remediation steps for security.

403 bypass
Discover how Cookie Bomb attacks cause Denial of Service by bloating HTTP headers. Learn technical payloads, real-world impacts, and how to stay protected.
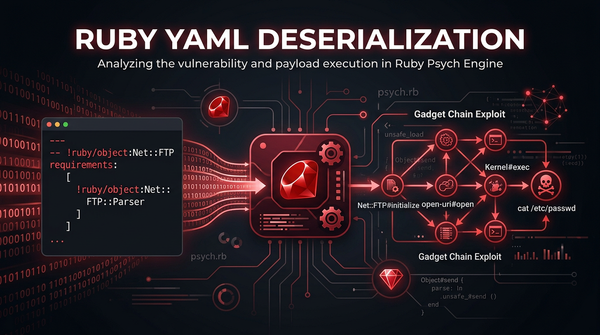
YAML Deserialization
Master Ruby YAML deserialization security. Explore technical exploit examples, gadget chains, and actionable mitigation strategies to protect your apps.
attack surface
A Deep Dive into Enterprise Deployments, DevOps Reality, and External Attack Surfaces. Subdomains - most consistently exploited attack surfaces.