403 bypass
What is Jailbreak Detection Bypass? Ways to Exploit, Examples and Impact
Discover how jailbreak detection bypass works. Explore technical exploit methods like Frida scripts and binary patching to secure your mobile apps.
403 bypass
Discover how jailbreak detection bypass works. Explore technical exploit methods like Frida scripts and binary patching to secure your mobile apps.
api security
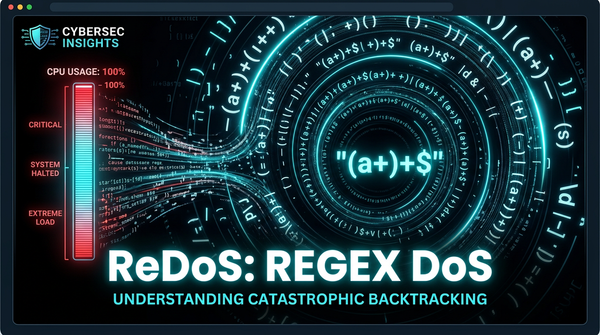
Discover how ReDoS attacks exploit catastrophic backtracking in regex engines. Learn to identify, exploit, and prevent ReDoS with practical examples.
403 bypass
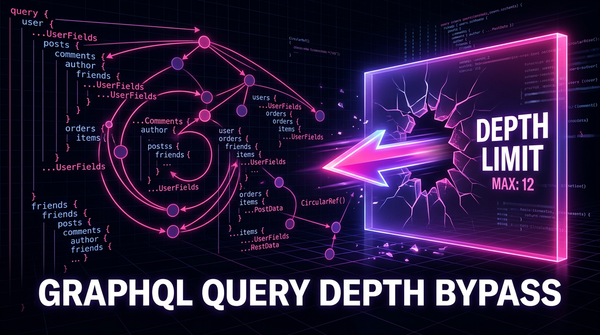
Learn how to identify and exploit GraphQL Query Depth Limit Bypasses. Discover technical payloads, mitigation strategies, and how to protect your APIs.
403 bypass
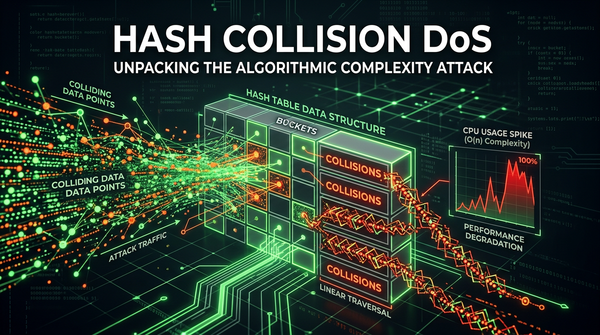
Learn how Hash Collision DoS attacks work, their technical impact on web applications, and how to prevent algorithmic complexity vulnerabilities.
403 bypass
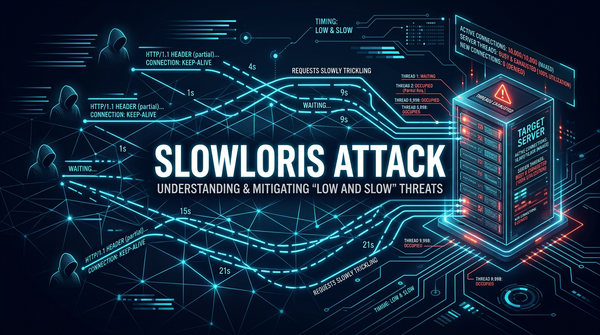
Learn how Slowloris attacks exploit web servers using low-bandwidth HTTP requests. Discover exploitation methods, real-world examples, and mitigation tips.

403 bypass
Discover how Java deserialization leads to RCE. Learn to identify gadget chains, use ysoserial, and implement secure coding practices to protect your apps.

apache
Learn how Apache Struts vulnerabilities like OGNL injection work. Explore technical exploit examples, RCE impact, and essential remediation steps for security.

403 bypass
Discover how Cookie Bomb attacks cause Denial of Service by bloating HTTP headers. Learn technical payloads, real-world impacts, and how to stay protected.

403 bypass
Discover how WordPress plugin vulnerabilities work, see real exploitation examples (XSS, SQLi, RCE), and learn how to secure your site against attacks.
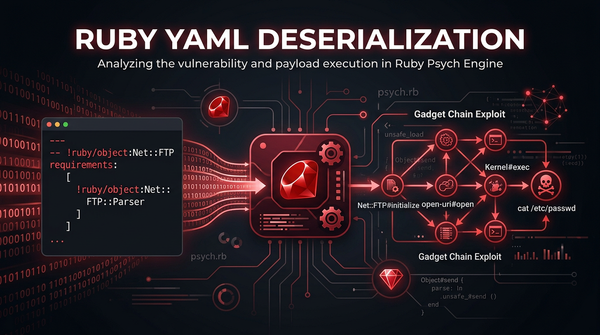
YAML Deserialization
Master Ruby YAML deserialization security. Explore technical exploit examples, gadget chains, and actionable mitigation strategies to protect your apps.
403 bypass
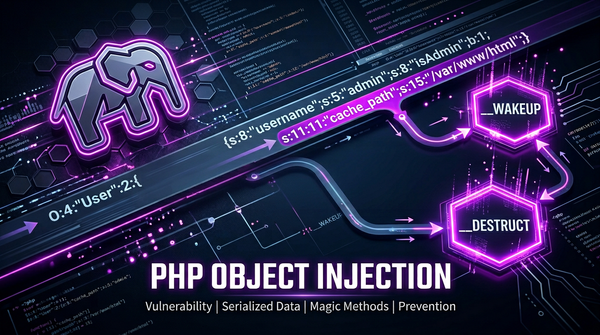
Learn how PHP Object Injection works, the danger of unserialize(), and how to prevent RCE and POP chains in your PHP applications.
bug bounty
403 errors are crucial during bug hunting and penetration testing. When bypassed, they can reveal sensitive information that leads to substantial bounties. Understanding and bypassing these errors is essential for earning good bounties and avoiding duplicate submissions.